Ddos Attacks Network Security Stable Diffusion Online

Evolution Of Network Layer Ddos Attacks Fastnetmon Ddos Detection Tool The generated image shows a network with multiple attacks, but the representation is not very clear and could benefit from more visual cues to indicate ddos attacks. Netscout cyber threat horizon provides a highly contextualized and customizable real time view into the global cyber threat landscape.
How To Identify And Respond To A Ddos Network Attack Infosecurity Preventing ddos attacks can be challenging, particularly during high traffic periods or across a vast and distributed network architecture. a truly proactive ddos threat defense hinges on several key factors: attack surface reduction, threat monitoring, and scalable ddos mitigation tools. Through detailed examination of real world incidents, current defense tools, ethical and legal implications, and future trends such as ai based attacks and decentralized security, this paper. What are the most efficient and effective strategies for detecting, preventing, and mitigating ddos attacks in cloud environments, considering factors such as performance, cost, and security?. Protect systems and services by enrolling in a ddos protection service that can monitor network traffic, confirm the presence of an attack, identify the source, and mitigate the situation by rerouting malicious traffic away from your network.
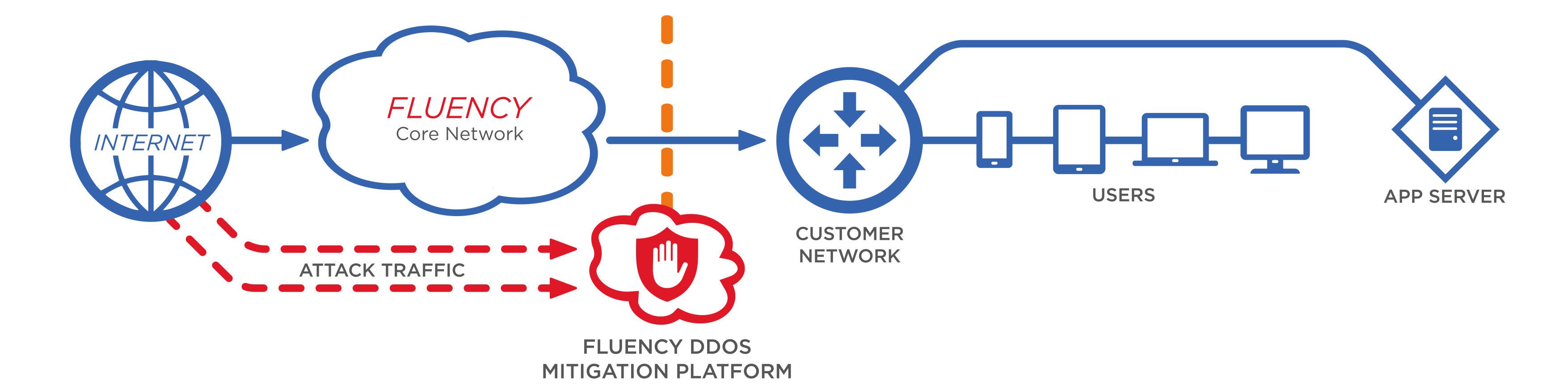
Commsworld Ddos Mitigation What are the most efficient and effective strategies for detecting, preventing, and mitigating ddos attacks in cloud environments, considering factors such as performance, cost, and security?. Protect systems and services by enrolling in a ddos protection service that can monitor network traffic, confirm the presence of an attack, identify the source, and mitigate the situation by rerouting malicious traffic away from your network. Our guide teaches you how to prevent ddos attacks and covers everything to know about them. ddos attacks are volume based attacks designed to overwhelm the target’s network bandwidth and flood it. they exploit network protocol weaknesses and disrupt business services. Learn how to stop a ddos attack fast. discover early warning signs and prevention tools to protect your website from future threats. Securityonline is a huge security community. it is committed to the sharing of high quality technical articles and safety reports, focusing on high quality security and security incidents in the industry. A denial of service (dos) attack is an attempt to overload a website or network, with the aim of degrading its performance or even making it completely inaccessible.
Comments are closed.