Data Security Lifecycle Colourbox

Diagram Of Information Security Lifecycle Stock Image Colourbox Colourbox explore photos holidays & celebrations weddings wedding ring photo: #13819859. The data security lifecycle is different from information lifecycle management in that it reflects the different needs of the security audience. it includes six phases from creation to destruction.
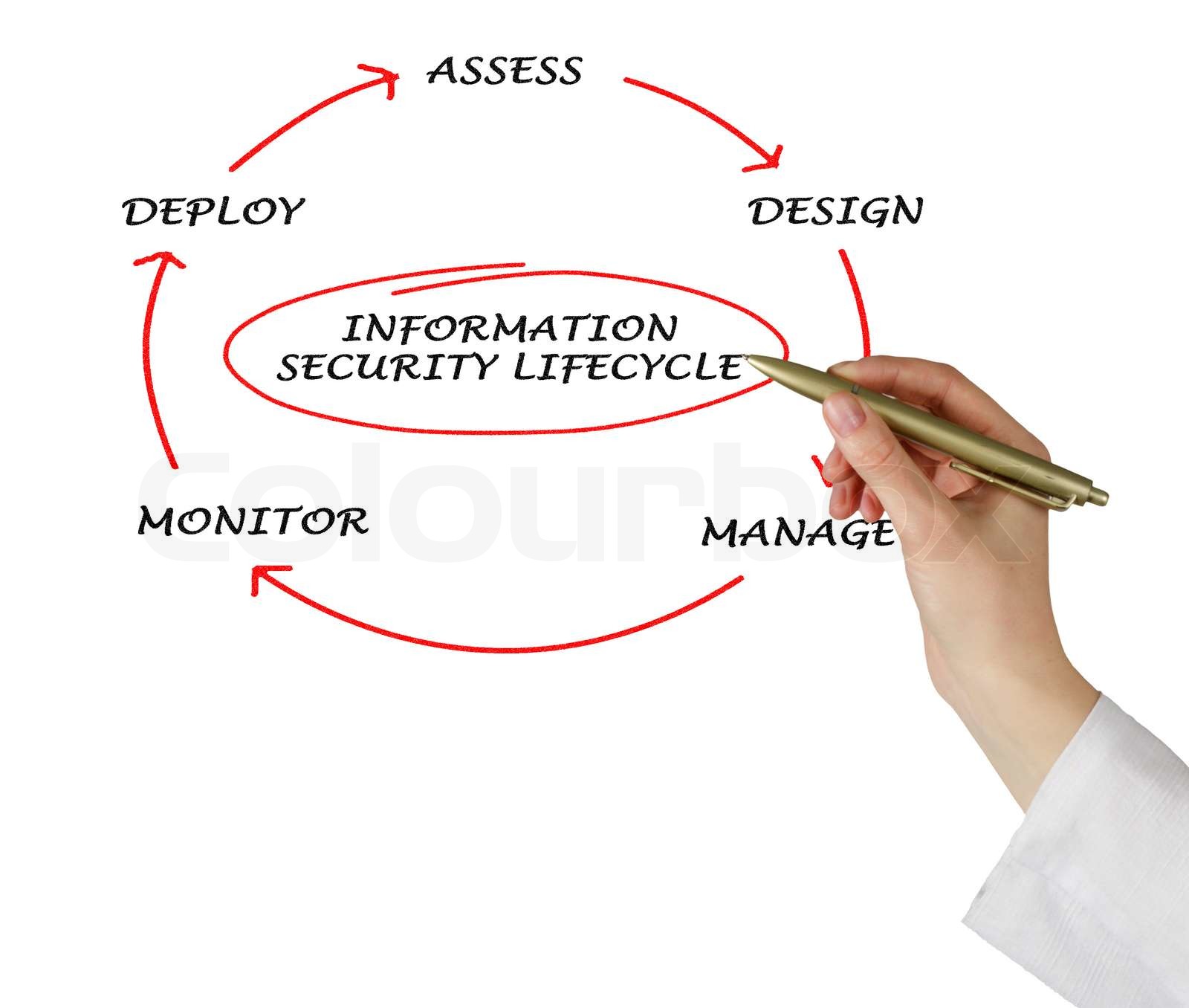
Diagram Of Information Security Lifecycle Stock Image Colourbox Use this guide to think through how your project will handle data at each stage, from creation to deletion. this is where you are now. as you scope your project, here are things to consider. define a data owner: who is ultimately responsible for the stewardship of this data?. Learn about data security, compliance, and governance concepts in microsoft purview for developers building compliant applications. Data security is the practice of protecting digital information from unauthorized access, corruption or theft throughout its lifecycle. it spans both physical and digital environments—including on premises systems, mobile devices, cloud platforms and third party applications. The six phases of the data security lifecycle include data discovery and classification, data protection and monitoring, data retention and storage, data backup and recovery, incident response and management, and compliance.

Diagram Of Information Security Lifecycle Stock Image Colourbox Data security is the practice of protecting digital information from unauthorized access, corruption or theft throughout its lifecycle. it spans both physical and digital environments—including on premises systems, mobile devices, cloud platforms and third party applications. The six phases of the data security lifecycle include data discovery and classification, data protection and monitoring, data retention and storage, data backup and recovery, incident response and management, and compliance. Data security lifecycle (csusad): a framework used to ensure the protection of data throughout its entire lifecycle, from creation to destruction. the stages typically include create, store, use, share, archive, and destroy. In this article, we explore each phase in depth, demonstrating how they interconnect to build a resilient, future proof data security posture that reduces risk, streamlines operations, and aligns with business objectives. data environments today are more complex and rapidly growing than ever before. Cybersecurity efforts must align with the stages of the data lifecycle to safeguard sensitive information against evolving threats. this publication outlines the unique security challenges and practical best practices for securing your organization's data at every stage. In the contemporary world, the security of data and privacy policies are major concerns in cloud computing. data stored on the cloud has been claimed to be unsafe and liable to be hacked.
Comments are closed.