Data Security In A Zero Trust Environment

Data Security In A Zero Trust Environment Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. Learn about zero trust data security, its key principles, benefits, and best practices for securing enterprises and cloud environments.

Rh Isac Data Security For A Zero Trust Environment Rh Isac This research article examines the concept of zero trust architecture and its effectiveness in protecting against insider threats and advanced persistent threats (apts) in modern network. Integrating security environments and requirements with reality, zero trust achieves the goal of three aspects of security: application and device security, authentication and access control security, and network architecture security. Zero trust security means that no one is trusted by default from inside or outside the network, and verification is required from everyone trying to gain access to resources on the network. this added layer of security has been shown to prevent data breaches. studies have shown that the average cost of a single data breach is over $3 million. Through the modules in this learning path, you'll gain an understanding of zero trust and how it applies to identity, endpoints, applications, networks, infrastructure, and data.
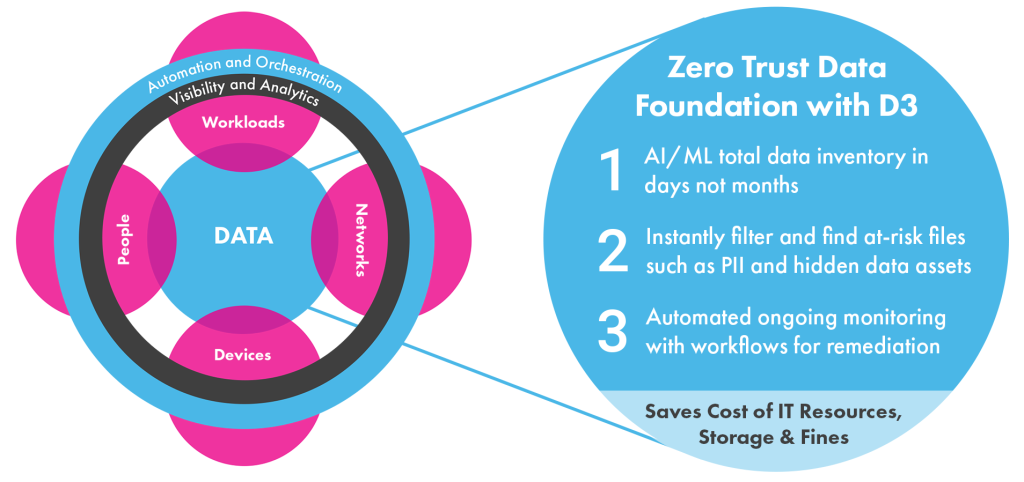
Security Zero Trust And Data Privacy Anacomp Inc Zero trust security means that no one is trusted by default from inside or outside the network, and verification is required from everyone trying to gain access to resources on the network. this added layer of security has been shown to prevent data breaches. studies have shown that the average cost of a single data breach is over $3 million. Through the modules in this learning path, you'll gain an understanding of zero trust and how it applies to identity, endpoints, applications, networks, infrastructure, and data. This architecture guide is focused on the cisco zero trust framework with the user and device security, network and cloud security, and application and data security pillars. Zero trust is a security framework that mandates stringent identity verification for every user and device attempting to access resources, regardless of whether they are inside or outside the organization’s network. Zero trust security moves cyber defenses from static, network based perimeters to a focus on users, assets, and resources. most organizations today are subject to data privacy regulations that emphasize granular access controls, a tenet of zero trust. Zero trust data security extends traditional zero trust principles to data protection by requiring continuous verification. core principles include least privilege access, microsegmentation, continuous monitoring, and data centric protections that follow information throughout its lifecycle.

Zero Trust Data Security A Modern Approach To Data Protection This architecture guide is focused on the cisco zero trust framework with the user and device security, network and cloud security, and application and data security pillars. Zero trust is a security framework that mandates stringent identity verification for every user and device attempting to access resources, regardless of whether they are inside or outside the organization’s network. Zero trust security moves cyber defenses from static, network based perimeters to a focus on users, assets, and resources. most organizations today are subject to data privacy regulations that emphasize granular access controls, a tenet of zero trust. Zero trust data security extends traditional zero trust principles to data protection by requiring continuous verification. core principles include least privilege access, microsegmentation, continuous monitoring, and data centric protections that follow information throughout its lifecycle.

Zero Trust Data Security A Modern Approach To Data Protection Zero trust security moves cyber defenses from static, network based perimeters to a focus on users, assets, and resources. most organizations today are subject to data privacy regulations that emphasize granular access controls, a tenet of zero trust. Zero trust data security extends traditional zero trust principles to data protection by requiring continuous verification. core principles include least privilege access, microsegmentation, continuous monitoring, and data centric protections that follow information throughout its lifecycle.

Understanding Zero Trust Security In The Cloud Environment
Comments are closed.