Data Security Audit Process Checklist

Data Security Audit Checklist Template V1 Pdf Discover how a data security audit safeguards sensitive information, ensures compliance and reduces risk. learn the key steps, common threats, and best practices in this comprehensive guide. Understanding the process helps you know how the data security audit works. however, with the data security audit checklist, you know exactly what to look out for:.

Data Security Audit Checklist Ciso2ciso Com Cyber Security Group It helps to identify vulnerabilities, ensure compliance with regulations, and protect against data breaches. this document outlines a detailed data security audit checklist to guide you through the evaluation of your data security measures. Discover how to perform a data security audit. learn the components of a comprehensive data security audit. Learn how to perform a data security audit step by step. this guide covers planning, risk assessment, technical evaluation, and provides a detailed checklist to strengthen your organization’s protection. Data security audits are a preventive solution that is highly cost effective when compared to dealing with the costly blowout of a data breach. this article will detail the top tools for data security audits, provide a checklist, and explain the common risks and targets of a data breach.
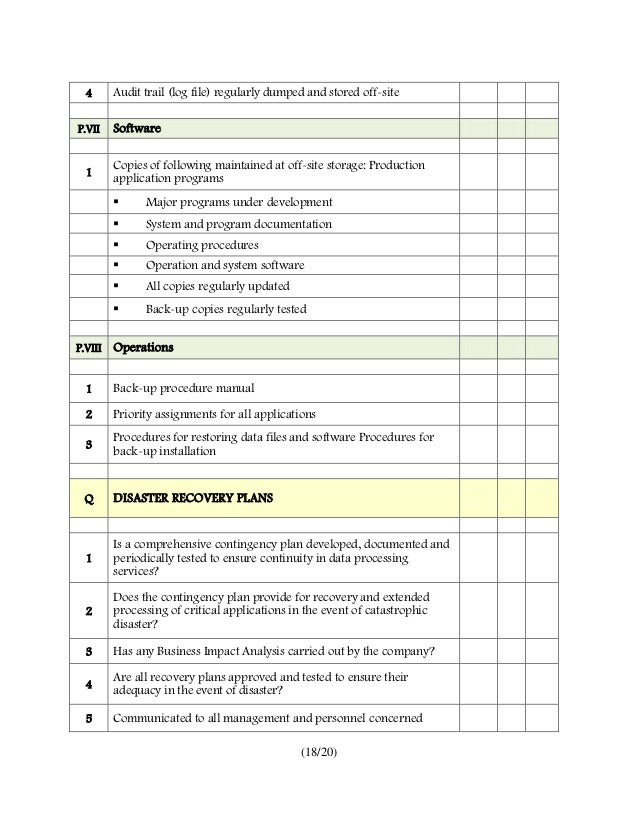
Security Audit Checklist Template Learn how to perform a data security audit step by step. this guide covers planning, risk assessment, technical evaluation, and provides a detailed checklist to strengthen your organization’s protection. Data security audits are a preventive solution that is highly cost effective when compared to dealing with the costly blowout of a data breach. this article will detail the top tools for data security audits, provide a checklist, and explain the common risks and targets of a data breach. Cybersecurity audit checklist for 2025: run smarter audits, reduce risk, and meet compliance faster. Fortify your systems with our comprehensive security audit checklist. this guide covers the 10 critical areas for a robust defense in 2025. Checklist: 8 steps to conducting a data security audit for your organisation this guide covers how to conduct effective audits, including scope definition, technical controls, risk assessment, and reporting. Ensure your organization is compliant with data protection regulations by using our comprehensive data protection audit checklist. this checklist covers all areas of data protection, including data storage, access controls, encryption, and data breach response.
8 Security Audit Checklist Templates In Pdf Doc Cybersecurity audit checklist for 2025: run smarter audits, reduce risk, and meet compliance faster. Fortify your systems with our comprehensive security audit checklist. this guide covers the 10 critical areas for a robust defense in 2025. Checklist: 8 steps to conducting a data security audit for your organisation this guide covers how to conduct effective audits, including scope definition, technical controls, risk assessment, and reporting. Ensure your organization is compliant with data protection regulations by using our comprehensive data protection audit checklist. this checklist covers all areas of data protection, including data storage, access controls, encryption, and data breach response.
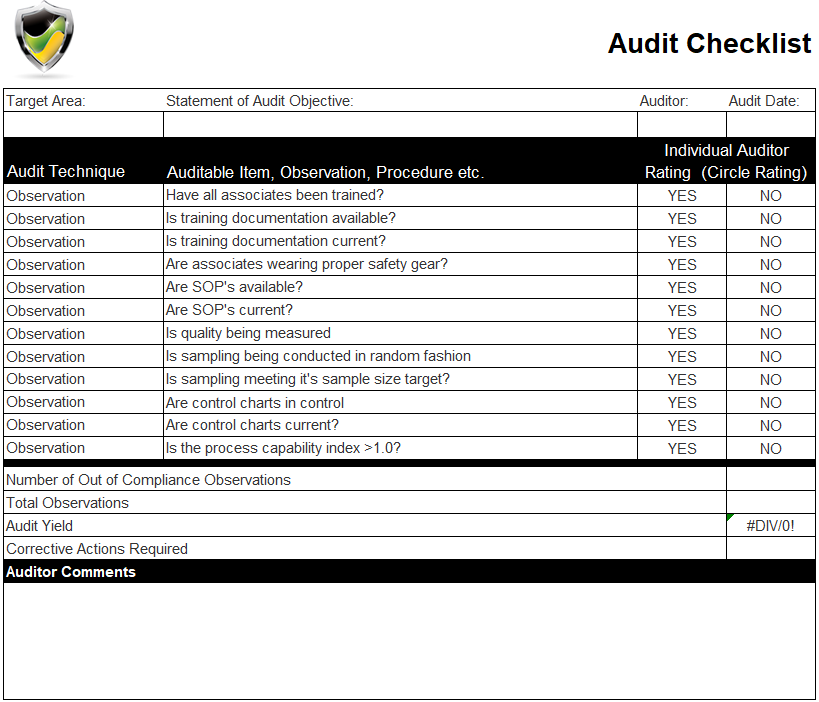
Software Process Audit Checklist Eyonm Checklist: 8 steps to conducting a data security audit for your organisation this guide covers how to conduct effective audits, including scope definition, technical controls, risk assessment, and reporting. Ensure your organization is compliant with data protection regulations by using our comprehensive data protection audit checklist. this checklist covers all areas of data protection, including data storage, access controls, encryption, and data breach response.

Download Free It Security Audit Checklist Template Captain It
Comments are closed.