Data Protection Considerations Microsoft Entra Microsoft Learn
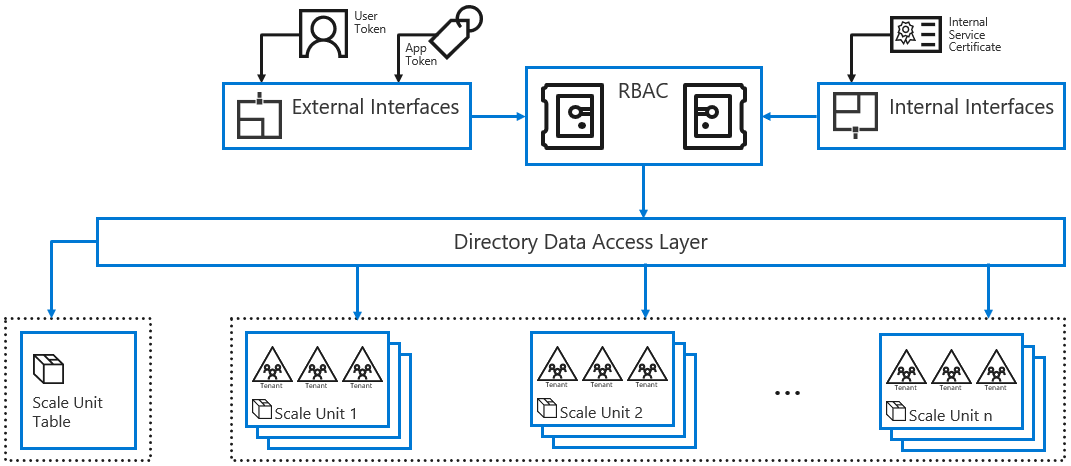
Data Protection Considerations Microsoft Entra Microsoft Learn Learn how services store and retrieve microsoft entra object data through an rbac authorization layer. Learn how services store and retrieve microsoft entra object data through an rbac authorization layer. the following diagram illustrates how services store and retrieve microsoft entra object data through a role based access control (rbac) authorization layer.

Microsoft Entra Data Protection Guide Pdf Password Encryption Learn how services store and retrieve microsoft entra object data through an rbac authorization layer. In this article, learn about data operational considerations for your configuration. there's information about how log files and other features work in relation to microsoft entra id, such as usage data and operator security. The document discusses data protection considerations when using microsoft entra, including how it stores and retrieves object data through role based access control and authorization layers. it also covers tenant isolation, data encryption, secret storage, and auditing capabilities. In this article, learn about data operational considerations for your configuration. there's information about how log files and other features work in relation to microsoft entra id, such as usage data and operator security.

Assess Personal Data And Privacy Risks Microsoft Priva And Microsoft The document discusses data protection considerations when using microsoft entra, including how it stores and retrieves object data through role based access control and authorization layers. it also covers tenant isolation, data encryption, secret storage, and auditing capabilities. In this article, learn about data operational considerations for your configuration. there's information about how log files and other features work in relation to microsoft entra id, such as usage data and operator security. Learn about best practices for effectively using microsoft entra id protection, such as enabling and configuring risk policies and integrating with conditional access for enhanced access security. In this short guide, we’ll walk through the first 4 steps you should consider when implementing or securing microsoft entra id. After analyzing countless security incidents and microsoft's latest 2025 updates, i've compiled the essential configurations that separate secure organizations from tomorrow's breach headlines. Explore advanced data protection with microsoft entra authentication contexts. learn to secure data using authentication contexts effectively.
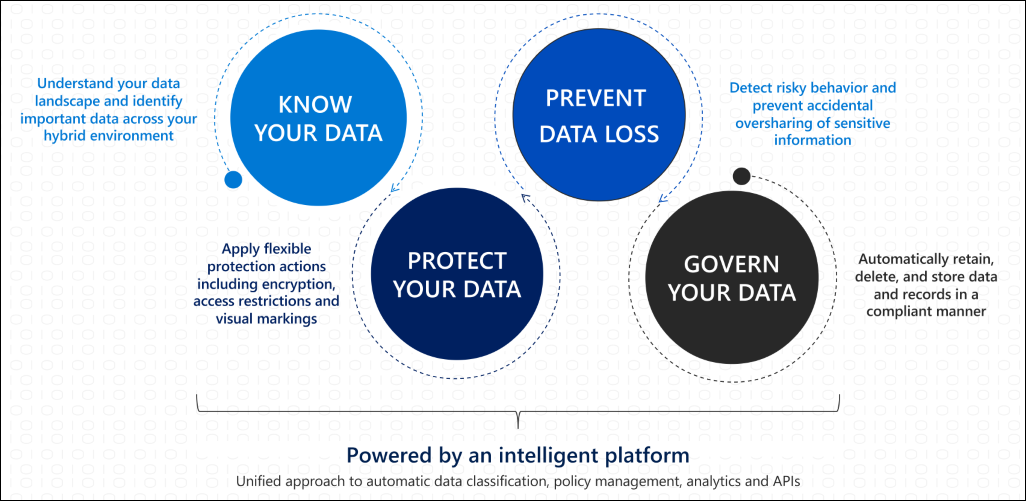
Microsoft Purview Information Protection Microsoft Learn Learn about best practices for effectively using microsoft entra id protection, such as enabling and configuring risk policies and integrating with conditional access for enhanced access security. In this short guide, we’ll walk through the first 4 steps you should consider when implementing or securing microsoft entra id. After analyzing countless security incidents and microsoft's latest 2025 updates, i've compiled the essential configurations that separate secure organizations from tomorrow's breach headlines. Explore advanced data protection with microsoft entra authentication contexts. learn to secure data using authentication contexts effectively.

Data Protection With Microsoft Purview For M365 Iti After analyzing countless security incidents and microsoft's latest 2025 updates, i've compiled the essential configurations that separate secure organizations from tomorrow's breach headlines. Explore advanced data protection with microsoft entra authentication contexts. learn to secure data using authentication contexts effectively.
Comments are closed.