Data Flows National Security Ppt

Data Flows National Security Ppt It highlights the evolution of national security since historical events like europe's thirty years war and outlines both internal and external threats, such as organized crime, poverty, and transnational terrorism. Visual analysis of security data flows – a free powerpoint ppt presentation (displayed as an html5 slide show) on powershow id: 102e5c ndvmz.
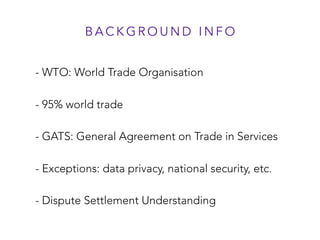
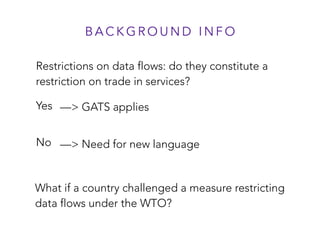
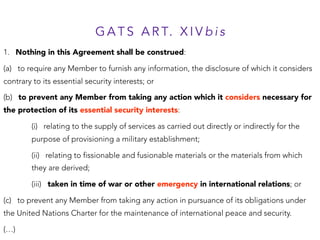
Data Flows National Security Ppt “a covered data transaction is any transaction that involves any bulk u.s. sensitive personal data or government related data and that involves: (1) data brokerage; (2) a vendor agreement; (3) an employment agreement; or (4) an investment agreement.”. The document outlines the historical evolution of national security concepts, key elements, and various internal and external threats faced by nations today. it emphasizes the importance of a flexible national security strategy for effectively navigating global security challenges. Engage your audience with professionally designed ppts with national security presentation templates and google slides. This research investigates the tension between national security imperatives, data sovereignty and the benefits of global data interoperability.
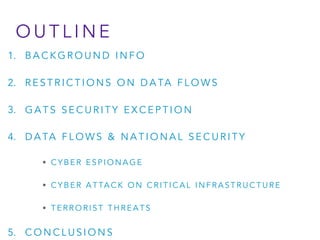
Data Flows National Security Ppt Engage your audience with professionally designed ppts with national security presentation templates and google slides. This research investigates the tension between national security imperatives, data sovereignty and the benefits of global data interoperability. Browse and edit among the wide collection of national security presentation templates and google slides. This document defines and discusses national security. it explains that national security originally referred to defense against military attacks but now includes non military threats like terrorism, crime, cyber attacks, and natural disasters. This paper explores the evolution of national security in the context of modern communication and information technologies (ict). it examines how globalization, terrorism, and the role of non state actors have transformed security dynamics, particularly in africa. Welcome to the “opsec for all” briefing, today we’ll talk about operations security opsec, what it is and why it’s important; and we’ll look at each of the five steps: analyze the threat, identify critical information, analyze vulnerabilities, assess risk, and apply countermeasures.
Data Flows National Security Ppt Browse and edit among the wide collection of national security presentation templates and google slides. This document defines and discusses national security. it explains that national security originally referred to defense against military attacks but now includes non military threats like terrorism, crime, cyber attacks, and natural disasters. This paper explores the evolution of national security in the context of modern communication and information technologies (ict). it examines how globalization, terrorism, and the role of non state actors have transformed security dynamics, particularly in africa. Welcome to the “opsec for all” briefing, today we’ll talk about operations security opsec, what it is and why it’s important; and we’ll look at each of the five steps: analyze the threat, identify critical information, analyze vulnerabilities, assess risk, and apply countermeasures.
Data Flows National Security Ppt This paper explores the evolution of national security in the context of modern communication and information technologies (ict). it examines how globalization, terrorism, and the role of non state actors have transformed security dynamics, particularly in africa. Welcome to the “opsec for all” briefing, today we’ll talk about operations security opsec, what it is and why it’s important; and we’ll look at each of the five steps: analyze the threat, identify critical information, analyze vulnerabilities, assess risk, and apply countermeasures.
Comments are closed.