Data Encryption In Data Encryption Examples Xncuc
Data Encryption In Data Encryption Examples Xncuc The most popular symmetric key cryptography systems are data encryption systems (des) and advanced encryption systems (aes) . symmetric key cryptography example: data encryption standard (des) des (data encryption standard) is an older encryption algorithm that is used to convert 64 bit plaintext data into 48 bit encrypted ciphertext. This repository was created to address the ever growing number of poor encryption code examples that float about the internet. this repository will expand over time to include examples in more languages.
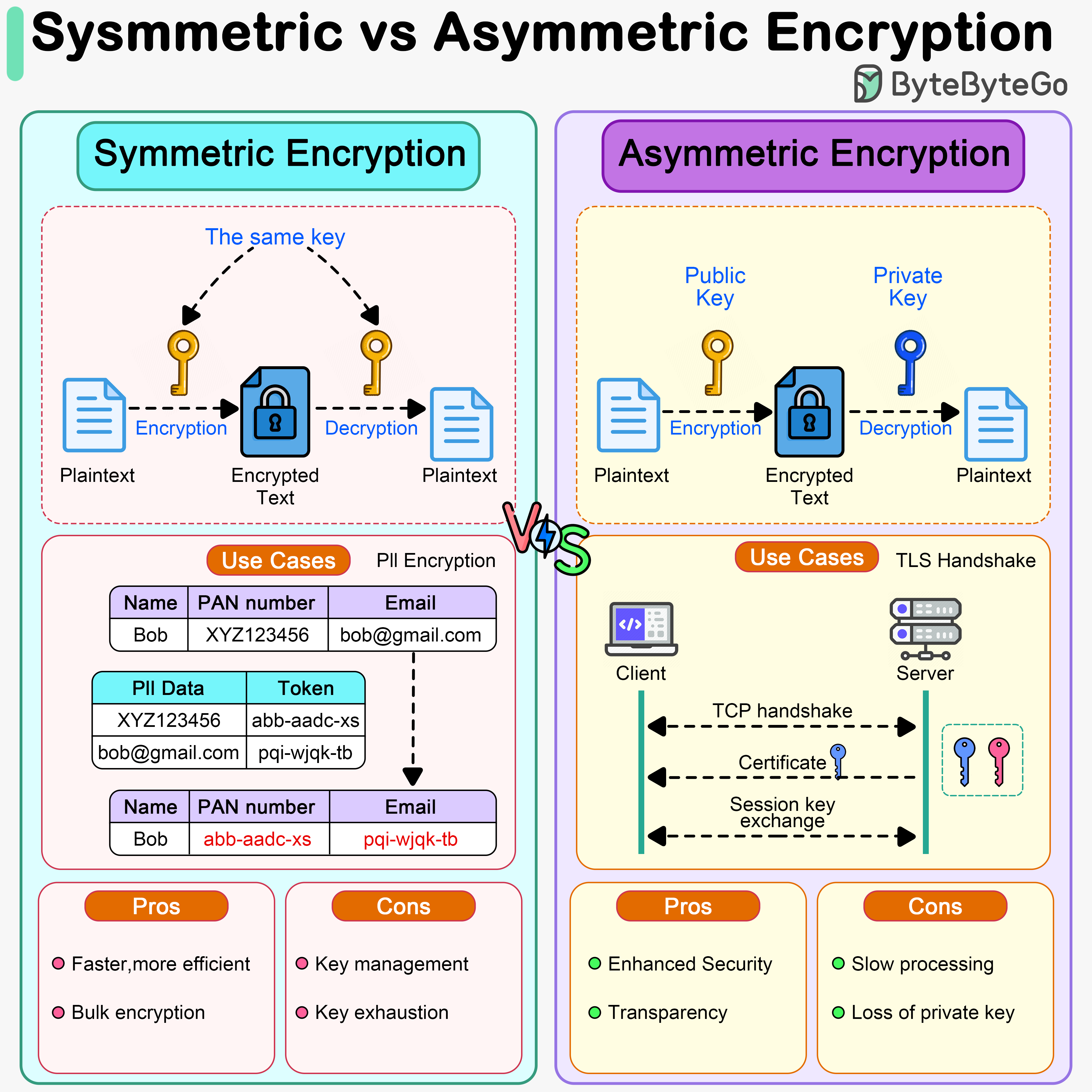
Bytebytego Symmetric Vs Asymmetric Encryption What is data encryption? learn how encryption works, explore key types of encryption, and see how cloud and database encryption protect sensitive data. Examples of symmetric encryption algorithms include the advanced encryption standard (aes) and the data encryption standard (des). on the other hand, asymmetric encryption uses two different keys (one public and one private) to protect data. Data encryption scrambles a piece of data, making it unreadable to any person, service, or device without the key to unlock its content. encryption makes files, disks, objects, streams, and other types of data private between an encryptor and a key holder. Explore the importance of encryption in safeguarding sensitive data, with examples like aes and rsa, crucial for security in banking, healthcare, and e commerce.
.jpg)
What Is Data Encryption Examples And Types Analytics Steps Data encryption scrambles a piece of data, making it unreadable to any person, service, or device without the key to unlock its content. encryption makes files, disks, objects, streams, and other types of data private between an encryptor and a key holder. Explore the importance of encryption in safeguarding sensitive data, with examples like aes and rsa, crucial for security in banking, healthcare, and e commerce. The act of data encryption gives birth to a hash derivative, which accompanies encrypted data. when the receiver applies the initial hash function to the received data and the resulting hash value matches the provided one, it is safe to deduce that the data endured an unaltered journey. The advanced encryption standard (aes), also known by its original name rijndael (dutch pronunciation: [ˈrɛindaːl]), [5] is a specification for the encryption of electronic data established by the us national institute of standards and technology (nist) in 2001. Data encryption is the process of transforming readable information into a coded format that can only be understood by someone who possesses the correct key to decode it. Ive understanding of data security through encryption. the methodology is structured to systematically explore the fundamental principles of encryption, assess its effectiveness in.
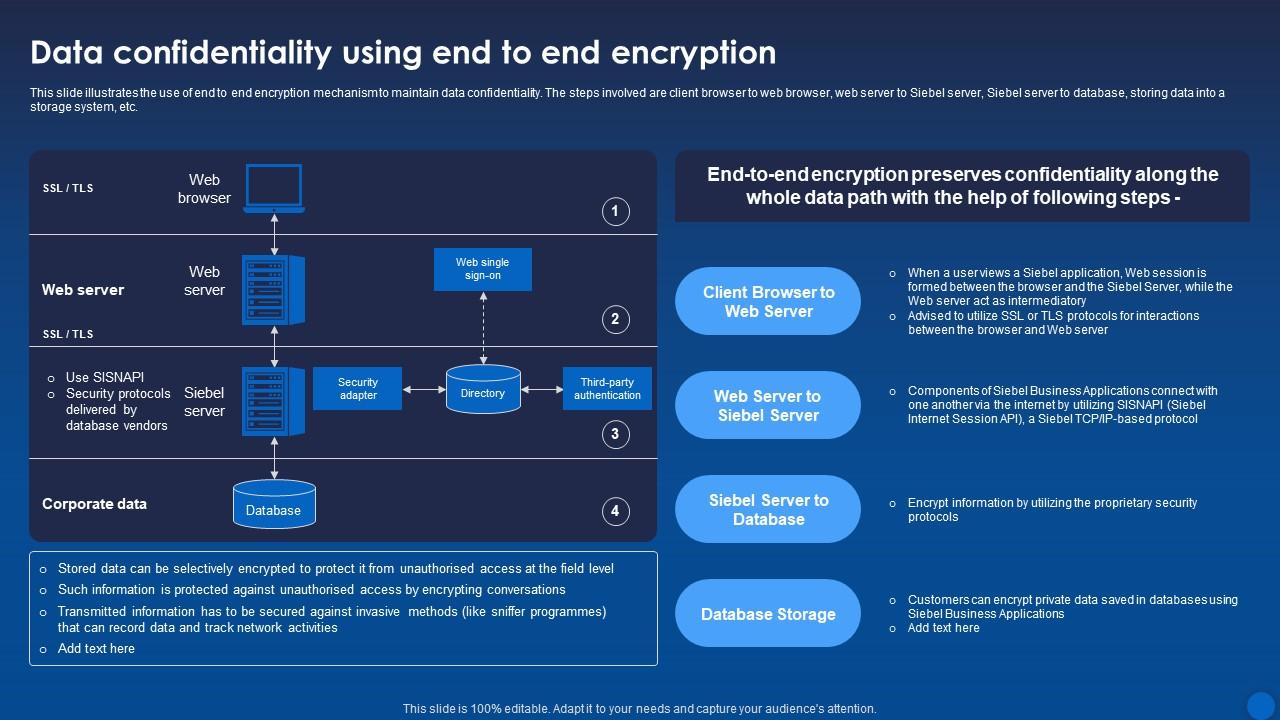
Data Confidentiality Using End To End Encryption Encryption For Data The act of data encryption gives birth to a hash derivative, which accompanies encrypted data. when the receiver applies the initial hash function to the received data and the resulting hash value matches the provided one, it is safe to deduce that the data endured an unaltered journey. The advanced encryption standard (aes), also known by its original name rijndael (dutch pronunciation: [ˈrɛindaːl]), [5] is a specification for the encryption of electronic data established by the us national institute of standards and technology (nist) in 2001. Data encryption is the process of transforming readable information into a coded format that can only be understood by someone who possesses the correct key to decode it. Ive understanding of data security through encryption. the methodology is structured to systematically explore the fundamental principles of encryption, assess its effectiveness in.
Comments are closed.