Cys535 Lecture03 Pdf Cipher Cryptography

Cipher Pdf Cryptography Secure Communication Cys535 lecture03 free download as pdf file (.pdf), text file (.txt) or read online for free. the document provides an overview of block ciphers and the data encryption standard (des). Besides des, there exist several block ciphers today — the most popular of these being blowfish, cast 128, and kasumi — that are also based on the feistel structure.
Chapter 3 Cryptography Pdf Cryptography Key Cryptography Cryptography studies techniques aimed at securing communication in the presence of adversaries. while encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that. In this section, we will learn: what is a block cipher, and what are the properties of a good block cipher; the different modes of operation of a block cipher; two prime examples of block ciphers: des and aes. Proper implementation with secure algorithms, large random keys, and protection of actual keys is important for cryptosystem strength. download as a pptx, pdf or view online for free. Lecture 03 free download as pdf file (.pdf), text file (.txt) or view presentation slides online.
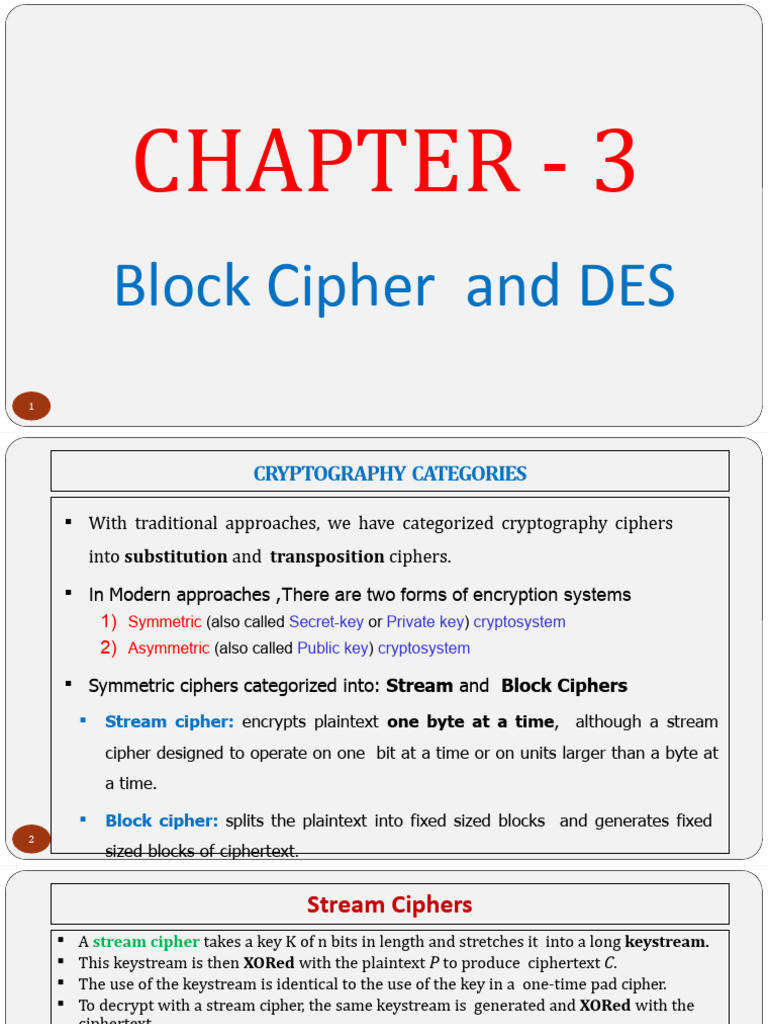
Chapter 3 Cryptography And Encryption Techniques Pdf Cryptography Proper implementation with secure algorithms, large random keys, and protection of actual keys is important for cryptosystem strength. download as a pptx, pdf or view online for free. Lecture 03 free download as pdf file (.pdf), text file (.txt) or view presentation slides online. Lecture 3 free download as pdf file (.pdf), text file (.txt) or read online for free. this document summarizes key aspects of the data encryption standard (des) algorithm presented in lecture 3 of a textbook on computer and network security. Lecture 03 free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. The document provides an overview of stream and block ciphers, detailing their principles, examples, and encryption processes. it specifically focuses on the data encryption standard (des), explaining its structure, key generation, and the f function used in encryption. The document explains the workings of block ciphers, specifically the des algorithm, detailing the processes of key generation, encryption, and decryption.

Cse Unit 3 Cryptography Pdf Lecture 3 free download as pdf file (.pdf), text file (.txt) or read online for free. this document summarizes key aspects of the data encryption standard (des) algorithm presented in lecture 3 of a textbook on computer and network security. Lecture 03 free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. The document provides an overview of stream and block ciphers, detailing their principles, examples, and encryption processes. it specifically focuses on the data encryption standard (des), explaining its structure, key generation, and the f function used in encryption. The document explains the workings of block ciphers, specifically the des algorithm, detailing the processes of key generation, encryption, and decryption.

Cryptography Notes 5 23 Pdf Cryptanalysis Cryptography The document provides an overview of stream and block ciphers, detailing their principles, examples, and encryption processes. it specifically focuses on the data encryption standard (des), explaining its structure, key generation, and the f function used in encryption. The document explains the workings of block ciphers, specifically the des algorithm, detailing the processes of key generation, encryption, and decryption.

Intro Cipher Pdf Cipher Cryptography
Comments are closed.