Cypher Tex Ppt Programming Languages Computing

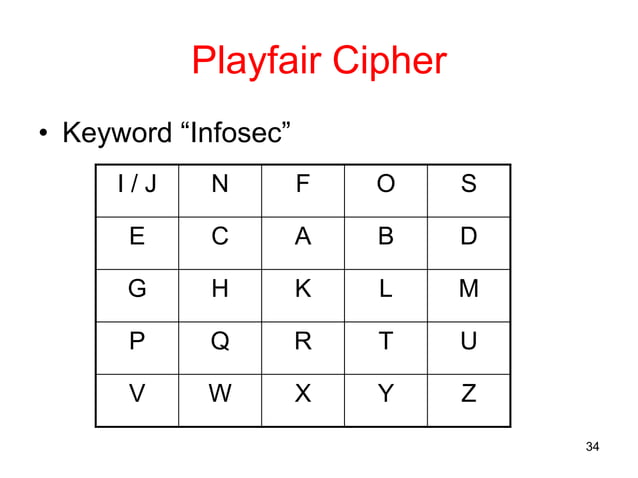
Cs Ppt Chp 3 Part 1 Pdf Cipher Cryptography The one time pad cipher combines a plaintext with a random key of the same length through modular addition to provide theoretically unbreakable encryption if used properly. download as a ppt, pdf or view online for free. Cryptanalysis of these classical ciphers often involves analyzing letter frequencies in ciphertexts to identify patterns and determine the encryption key. the development of polyalphabetic ciphers and product ciphers attempted to strengthen encryption by combining multiple encryption stages. we take content rights seriously.
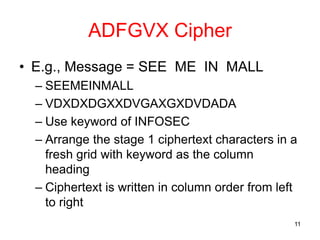
Cypher Tex Ppt Chapter 11: cipher techniques. some problems. types of ciphers. networks. examples. overview problems what can go wrong if you naively use ciphers cipher types stream or block ciphers?. An introductory powerpoint on encryption and decryption, including information about the caesar cipher and the pigpen cipher. powerpoint has been updated: 12th april. The encryption and decryption algorithms are known. there are only 25 keys to try. the language of the plaintext is known and easily recognizable. You can view or download cypher text cleartext pairs presentations for your school assignment or business presentation. browse for the presentations on every topic that you want.

Cypher Tex Ppt The encryption and decryption algorithms are known. there are only 25 keys to try. the language of the plaintext is known and easily recognizable. You can view or download cypher text cleartext pairs presentations for your school assignment or business presentation. browse for the presentations on every topic that you want. From classical encryption methods to modern algorithms, our slides provide a comprehensive overview that caters to various audiences, whether you're teaching a classroom full of eager learners or presenting to industry experts. use cases for our cryptography presentations are vast and varied. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. If we assume the extended riemann hypothesis, then computing the secret key (n, d) from the public key (n, e) is (essentially) the same problem as factoring. however, without erh, we don’t actually know that breaking rsa will always factor the modulus n. Decryption in deciphering the cipher text, we must perform the opposite (or inverse) functions on the cipher text to retrieve the plaintext. once again, the first step is to convert each of the cipher text letters into their integer values.
Cypher Ppt Databases Computer Software And Applications From classical encryption methods to modern algorithms, our slides provide a comprehensive overview that caters to various audiences, whether you're teaching a classroom full of eager learners or presenting to industry experts. use cases for our cryptography presentations are vast and varied. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. If we assume the extended riemann hypothesis, then computing the secret key (n, d) from the public key (n, e) is (essentially) the same problem as factoring. however, without erh, we don’t actually know that breaking rsa will always factor the modulus n. Decryption in deciphering the cipher text, we must perform the opposite (or inverse) functions on the cipher text to retrieve the plaintext. once again, the first step is to convert each of the cipher text letters into their integer values.
Cypher Tex Ppt Programming Languages Computing If we assume the extended riemann hypothesis, then computing the secret key (n, d) from the public key (n, e) is (essentially) the same problem as factoring. however, without erh, we don’t actually know that breaking rsa will always factor the modulus n. Decryption in deciphering the cipher text, we must perform the opposite (or inverse) functions on the cipher text to retrieve the plaintext. once again, the first step is to convert each of the cipher text letters into their integer values.

Cryptography Ppt Computer System Security Ppt Pptx Information
Comments are closed.