Cybersift Tutela Getting Started
Tutela By Cybersift Medium Tutela simplifies the process with easy setup for asset inventory, web filtering, and host forensics – all achievable within minutes. prioritize threats based on severity, allowing you to focus on what truly matters for your organization. 1 share 224 views 4 years ago login or signup: vas.cybersift.io more details: more.
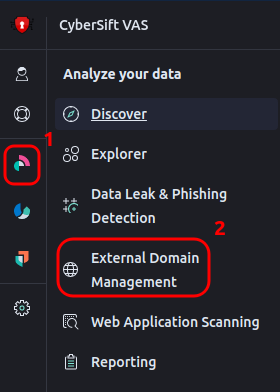
Tutela Windows Agent Now Ships With Forensics And In Built Ids By A modern team knowledge base for your internal documentation, product specs, support answers, meeting notes, onboarding, & more…. 1 installation 2 ship data 3 add ai install the cybersift server. View on how to login and get started on tutela a new cybersecurity product for vulnerability scanning, phishing and data leakage detection. Cybersift tutela is a vulnerability assessment solution that performs network scanning to identify security weaknesses and potential exploitation points. the platform conducts infrastructure scans to detect vulnerabilities and provides compliance support through automated reporting.

Cisa S Known Exploited Vulnerabilities Catalog By David Vassallo View on how to login and get started on tutela a new cybersecurity product for vulnerability scanning, phishing and data leakage detection. Cybersift tutela is a vulnerability assessment solution that performs network scanning to identify security weaknesses and potential exploitation points. the platform conducts infrastructure scans to detect vulnerabilities and provides compliance support through automated reporting. Cybersift tutela login sign up documentation forgot password cybersift tutela. Tutela does not use any heavy weight appliances to run your network scans, but instead uses a lightweight agent that can be installed on any linux machine. this allows you to get started with scanning your network in a few minutes. Tutela by cybersift helps you discover your attack surface, by scanning both internal and external infrastructure, as well as 3rd party sites for potential credential leaks. Tutela, our cutting edge vulnerability assessment solution, proactively strengthens infrastructure security by identifying and alerting to potential threats. conducting a detailed scan of your network, it identifies devices, operating systems, and application versions.
Comments are closed.