Cybersecurity Vulnerability Utf8 Encoding Unicode

Vulnerability In Rules Files With Hidden Unicode Characters In this post, we will look at the basics of unicode encoding and use that as a foundation for understanding the technical intricacies of invalid, overlong utf 8 sequences. armed with this knowledge, we can begin to explore the associated security risks. This guide has been designed to give web application developers, software engineers, and application security researchers a reference for understanding unicode related security issues in operating systems, applications, and the web.

How I Found An Xss Vulnerability Via Using Emojis By Exploiting Unicode The invisible unicode characters were devised decades ago and then largely forgotten. that is, until 2024, when hackers began using the characters to conceal malicious prompts fed to ai engines. According to the rfc 3629, a particularly subtle form of this attack can be carried out against a parser which performs security critical validity checks against the utf 8 encoded form of its input, but interprets certain illegal octet sequences as characters. An attacker can use this technique to encode certain characters in the url to bypass application filters, thus accessing restricted resources on the web server or to force browsing to protected pages. The overlong utf 8 encoding attack is a security vulnerability associated with improperly handling or validating utf 8 encoded data. here's a breakdown of the issue and its implications:.
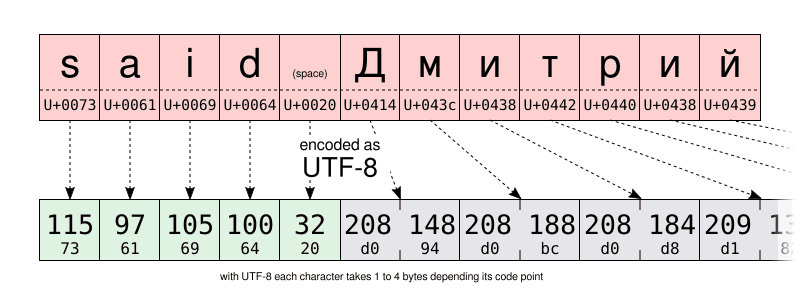
Battle Of The Texts And The Unicode Savior An attacker can use this technique to encode certain characters in the url to bypass application filters, thus accessing restricted resources on the web server or to force browsing to protected pages. The overlong utf 8 encoding attack is a security vulnerability associated with improperly handling or validating utf 8 encoded data. here's a breakdown of the issue and its implications:. Of these four, utf 7 has been deprecated, utf 8 is the most commonly used on the web, and both utf 16 and utf 32 can be serialized in little or big endian format. Security researchers have identified a sophisticated phishing technique where threat actors embed invisible unicode characters directly into email subject lines to evade automated detection systems. This document specifies mechanisms that can be used to detect possible security problems. this document has been reviewed by unicode members and other interested parties, and has been approved for publication by the unicode consortium. However, improper usage of unicode can introduce security vulnerabilities, including visual security issues, utf 8 exploits, text comparison vulnerabilities, buffer overflows, and code point deletions.
Comments are closed.