Cybersecurity Regulations Sbom Security Pattern
What Is An Sbom Why Are They Important An Intro To Sboms A “software bill of materials” (sbom) has emerged as a key building block in software security and software supply chain risk management. an sbom is a nested inventory, a list of ingredients that make up software components. The eu cyber resilience act (cra) is the most important binding product security regulation affecting software and digital products in the eu. most teams should prepare by automating sbom generation, validating output, and tying sboms into vulnerability and compliance workflows.

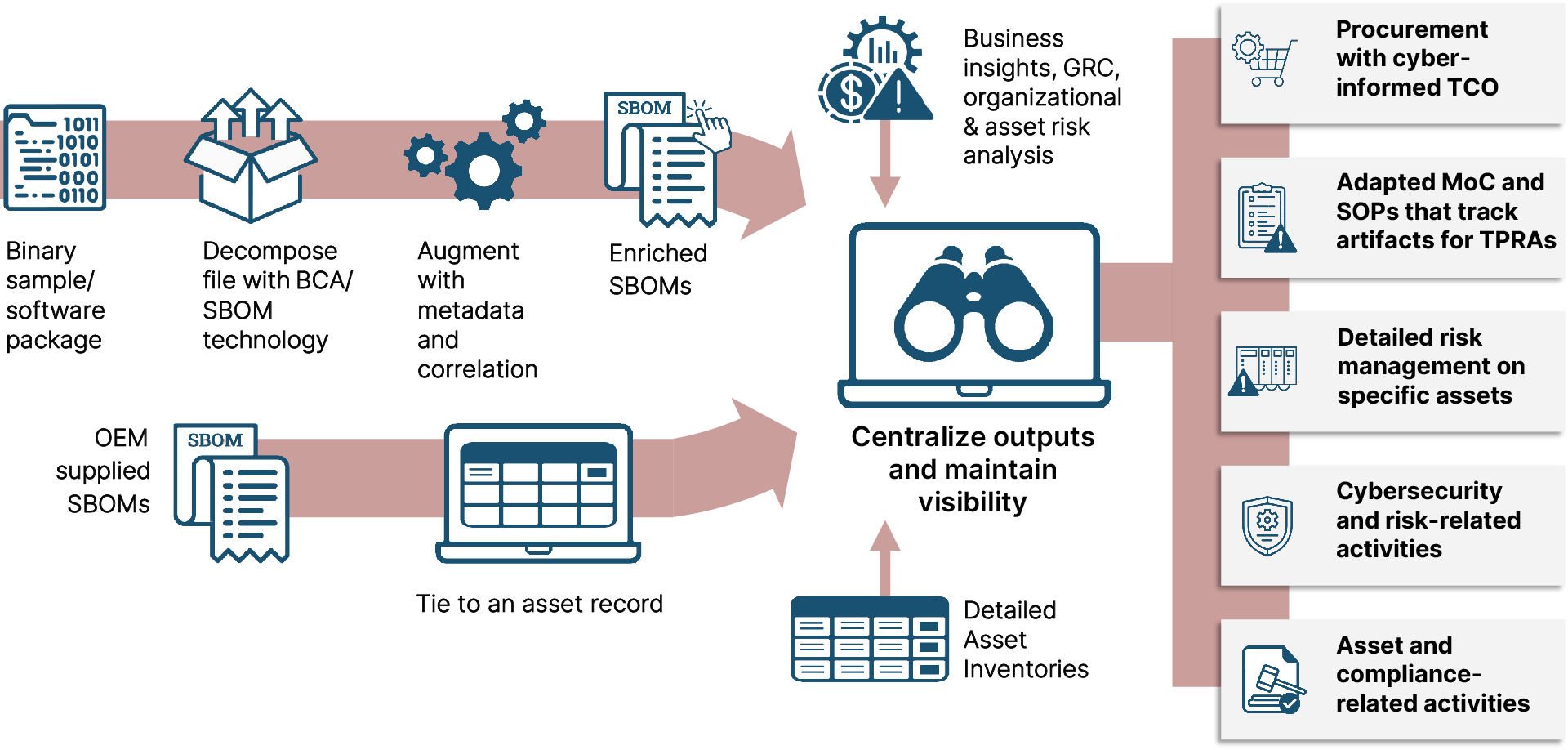
Cybersecurity Regulations Sbom Security Pattern This cybersecurity information sheet (csi) highlights best practices and provides recommendations for users of national security systems (nss) to help them incorporate sbom management functions. Explore how global policy frameworks like the eu cyber resilience act (cra) and u.s. cisa minimum elements are shaping the evolution of software bill of materials (sbom) standards. The european union has significantly elevated its cybersecurity posture with the adoption of regulation (eu) 2024 2847, also known as the cra (cyber resilience act). as the first horizontal cybersecurity regulation for pdes (products with digital elements), the cra establishes legally binding security requirements for both hardware and software placed on the eu market. in 2024, the regulation. Understand cra sbom requirements and boost product security. start preparing today for full eu cyber resilience act compliance.

Security Pattern Embedded Security By Design For Automotive The european union has significantly elevated its cybersecurity posture with the adoption of regulation (eu) 2024 2847, also known as the cra (cyber resilience act). as the first horizontal cybersecurity regulation for pdes (products with digital elements), the cra establishes legally binding security requirements for both hardware and software placed on the eu market. in 2024, the regulation. Understand cra sbom requirements and boost product security. start preparing today for full eu cyber resilience act compliance. The eu cyber resilience act makes sboms mandatory for software products sold in europe starting december 2027, with fines up to €15 million for non compliance. here's what software vendors need to know and how to prepare. Learn about sbom requirements and standards around the globe, from the fda to the eu cyber resilience act, and how to use sboms for compliance. Ntia’s guidance acknowledges that sbom capabilities are currently nascent for federal acquirers and that the minimum elements are only the first key step in a process that will mature over time. This post will summarize recent guidelines, regulations, or government memos that encourage increased usage and standards around sboms, fboms, and hboms. we’ll cover what the requirements actually say, how to achieve them, and how to add value for your team’s cyber risk management programs with sboms.

Continuous Compliance Sbom The eu cyber resilience act makes sboms mandatory for software products sold in europe starting december 2027, with fines up to €15 million for non compliance. here's what software vendors need to know and how to prepare. Learn about sbom requirements and standards around the globe, from the fda to the eu cyber resilience act, and how to use sboms for compliance. Ntia’s guidance acknowledges that sbom capabilities are currently nascent for federal acquirers and that the minimum elements are only the first key step in a process that will mature over time. This post will summarize recent guidelines, regulations, or government memos that encourage increased usage and standards around sboms, fboms, and hboms. we’ll cover what the requirements actually say, how to achieve them, and how to add value for your team’s cyber risk management programs with sboms.

Security Pattern On Linkedin Cybersecurity Newsletter Sbom Ntia’s guidance acknowledges that sbom capabilities are currently nascent for federal acquirers and that the minimum elements are only the first key step in a process that will mature over time. This post will summarize recent guidelines, regulations, or government memos that encourage increased usage and standards around sboms, fboms, and hboms. we’ll cover what the requirements actually say, how to achieve them, and how to add value for your team’s cyber risk management programs with sboms.
Comments are closed.