Cybersecurity Red Teaming Explained Simply
Red Teaming Ciberon Red teaming is a process for testing cybersecurity effectiveness where ethical hackers conduct a simulated and nondestructive cyberattack. the simulated attack helps an organization identify vulnerabilities in its system and make targeted improvements to security operations. What is red teaming? red teaming in the context of cybersecurity is the process through which an organization assesses its cybersecurity stances using techniques and methods that mimic real life adversaries.

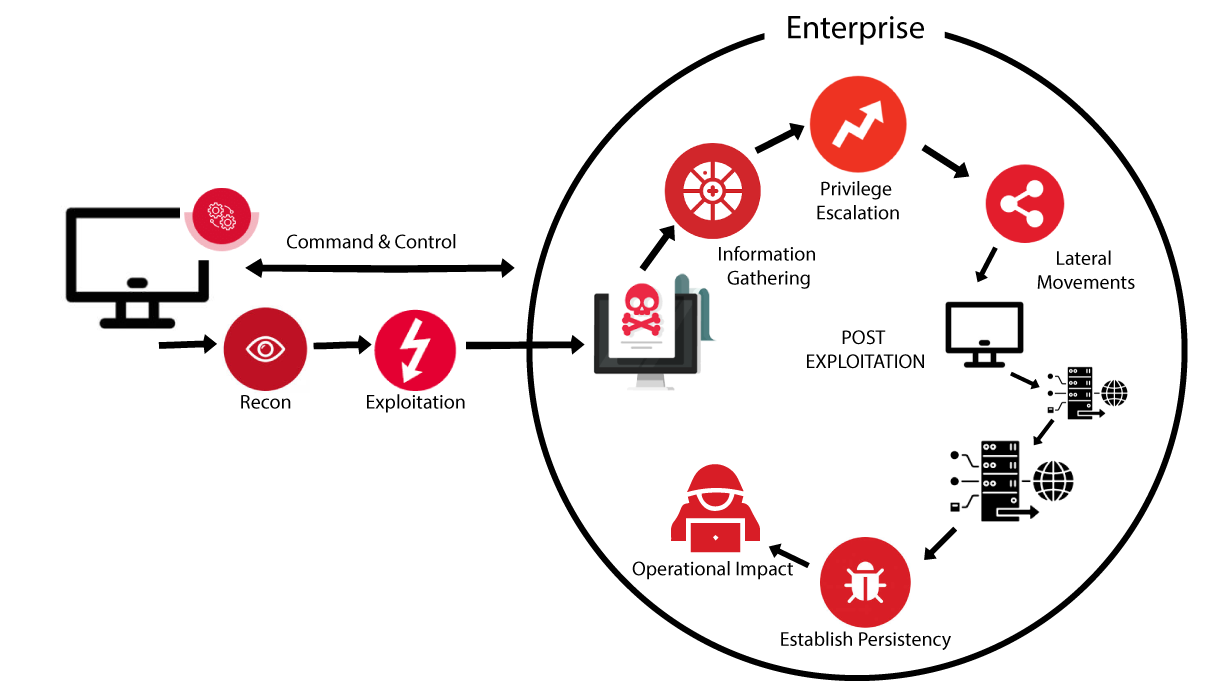
Red Teaming Cyber Shadow Red teaming involves a group of security professionals who act as adversaries, attempting to breach an organization’s defenses using the same tactics, techniques, and procedures (ttps) employed by real attackers. The article explains what red teaming is and how it simulates real world cyberattacks to test an organization's security posture. it describes how red teaming works in cybersecurity, involving ethical hackers conducting exercises like social engineering and adversary emulation. Red teaming is a proactive approach to cybersecurity where a group of ethical hackers (the red team) uses the latest adversarial exploits to gain unauthorized access to an organization’s systems or data. the goal of red teaming is to identify vulnerabilities by simulating real world threats. Red teaming is a simulated cyberattack conducted by cybersecurity professionals who emulate the tactics, techniques and procedures (ttps) of real world hackers like threat actors, cyber criminal groups and advanced persistent threats (apts).
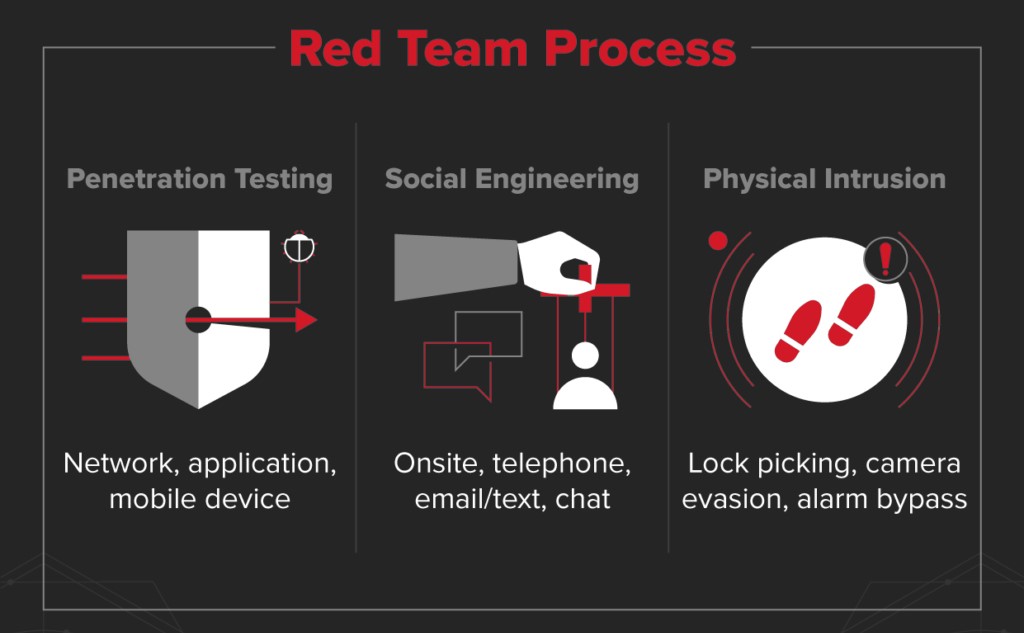
Red Teaming Isec Services And Products Red teaming is a proactive approach to cybersecurity where a group of ethical hackers (the red team) uses the latest adversarial exploits to gain unauthorized access to an organization’s systems or data. the goal of red teaming is to identify vulnerabilities by simulating real world threats. Red teaming is a simulated cyberattack conducted by cybersecurity professionals who emulate the tactics, techniques and procedures (ttps) of real world hackers like threat actors, cyber criminal groups and advanced persistent threats (apts). A red team is a group of individuals simulating real world cyber attacks against an organization’s systems and defenses. the goal of a red team is to test the organization’s defenses and identify any weaknesses or vulnerabilities that a real attacker could exploit. Red teaming is an advanced and effective way for organizations to test the strength of their security system. when used along with other security measures, like endpoint security and threat hunting, red teaming can help you ensure your organization is protected from potential attackers. Red teaming is a powerful tool for testing and improving an organization’s cybersecurity posture. by simulating real world attacks, red teams provide unparalleled insights into vulnerabilities, defenses, and response capabilities. Learn what a red team is in cybersecurity. this beginner's guide explains how ethical hackers simulate real attacks to build powerful, proactive defenses for any organization.

Red Teaming Bluedog Cyber Security Monitoring A red team is a group of individuals simulating real world cyber attacks against an organization’s systems and defenses. the goal of a red team is to test the organization’s defenses and identify any weaknesses or vulnerabilities that a real attacker could exploit. Red teaming is an advanced and effective way for organizations to test the strength of their security system. when used along with other security measures, like endpoint security and threat hunting, red teaming can help you ensure your organization is protected from potential attackers. Red teaming is a powerful tool for testing and improving an organization’s cybersecurity posture. by simulating real world attacks, red teams provide unparalleled insights into vulnerabilities, defenses, and response capabilities. Learn what a red team is in cybersecurity. this beginner's guide explains how ethical hackers simulate real attacks to build powerful, proactive defenses for any organization.
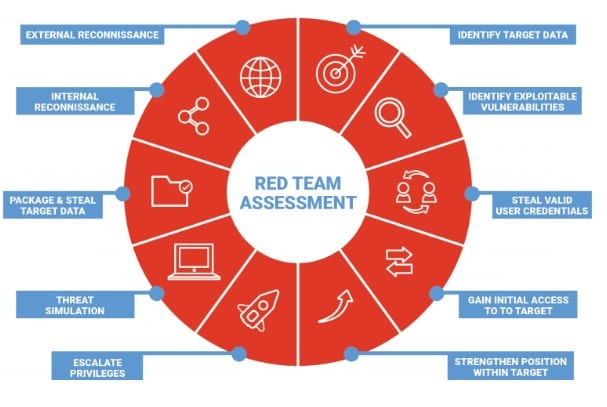
What Is Red Teaming And How Does It S Working Red teaming is a powerful tool for testing and improving an organization’s cybersecurity posture. by simulating real world attacks, red teams provide unparalleled insights into vulnerabilities, defenses, and response capabilities. Learn what a red team is in cybersecurity. this beginner's guide explains how ethical hackers simulate real attacks to build powerful, proactive defenses for any organization.
Comments are closed.