Cybersecurity Pentesting Ethicalhacking Osint Dataexposure
How To Use Osint Framework Tools For Effective Pentesting This repository curates the best bug bounty resources, osint tools, ctf challenges, and privilege escalation techniques, along with linux commands, metasploit usage, and networking fundamentals — making it a perfect learning hub for aspiring ethical hackers and seasoned professionals. Osint is the process of gathering and analysing publicly available information. it’s widely used in penetration testing, threat analysis, journalism, and investigations. the beauty of osint.

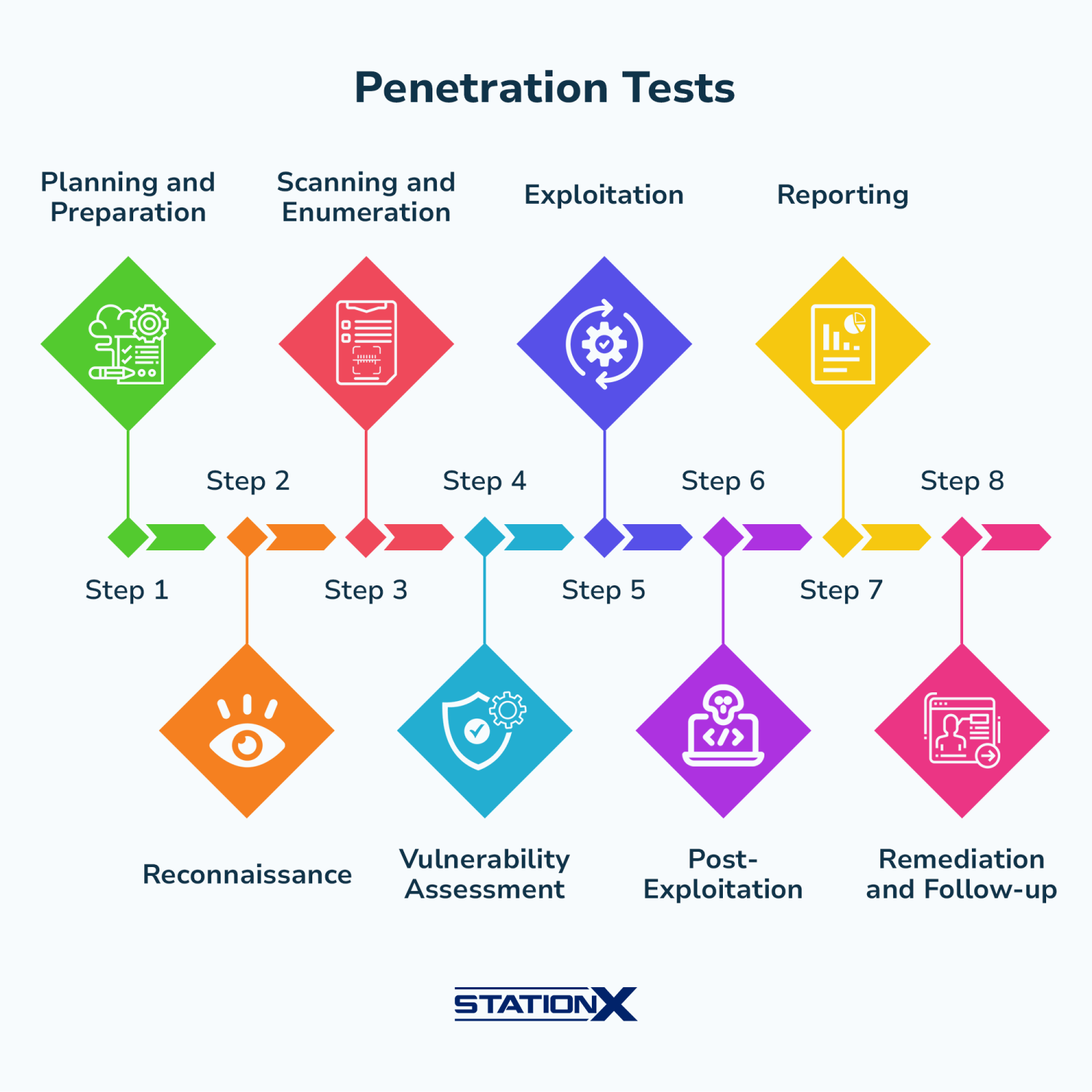
How To Use Osint Framework Tools For Effective Pentesting Cybersecurity professionals perform penetration testing using osint as a proactive measure to protect organizations. using publicly available information, the tester can determine which areas are open to exploits. Penetration testing, often referred to as ethical hacking, is a crucial component of modern cybersecurity practices. it involves simulating real world attacks on systems, networks, and applications to identify vulnerabilities before malicious hackers can exploit them. 🕵️ most people think hacking is about writing complex code. it’s not. 80% of real attacks start with osint — open source intelligence. before any exploit, the best ethical hackers spend. By mapping the target’s digital presence, osint shapes effective risk management, influencing how resources are allocated in an organization’s overall security posture. this synergy extends beyond ethical hacking into threat intelligence, brand protection, or competitor research.

How To Use Osint Framework Tools For Effective Pentesting 🕵️ most people think hacking is about writing complex code. it’s not. 80% of real attacks start with osint — open source intelligence. before any exploit, the best ethical hackers spend. By mapping the target’s digital presence, osint shapes effective risk management, influencing how resources are allocated in an organization’s overall security posture. this synergy extends beyond ethical hacking into threat intelligence, brand protection, or competitor research. Ethical hackers leverage osint tools to gather information before performing security assessments. in this guide, we’ll explore osint fundamentals, its importance in cybersecurity, popular osint tools, and how they are used effectively. In the ever evolving landscape of cybersecurity, one aspect often overlooked by organizations is the power and risk of open source intelligence (osint). this article discusses osint for penetration testers. Discover the most powerful open source intelligence tools used by ethical hackers, bug bounty hunters, and cybersecurity professionals complete with safety protocols and real world case studies. Tools like master osint v3 enable deep social media reconnaissance, username tracking, and data aggregation—but must be used ethically. this guide explores key osint techniques, python based tools, and best practices for responsible intelligence gathering.
Comments are closed.