Cybersecurity Penetration Testing
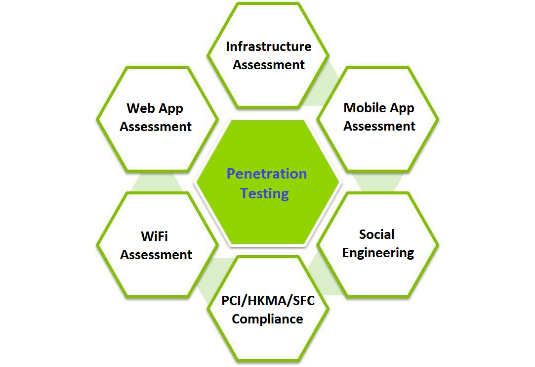
Penetration Testing Services Source Code Review Other Tests Penetration testers are security professionals skilled in the art of ethical hacking, which is the use of hacking tools and techniques to fix security weaknesses rather than cause harm. companies hire pen testers to launch simulated attacks against their apps, networks, and other assets. Learn what penetration testing is, why it is important, and how it is performed. explore different types of pen tests, such as social engineering, network, web application, wireless, iot, and more.
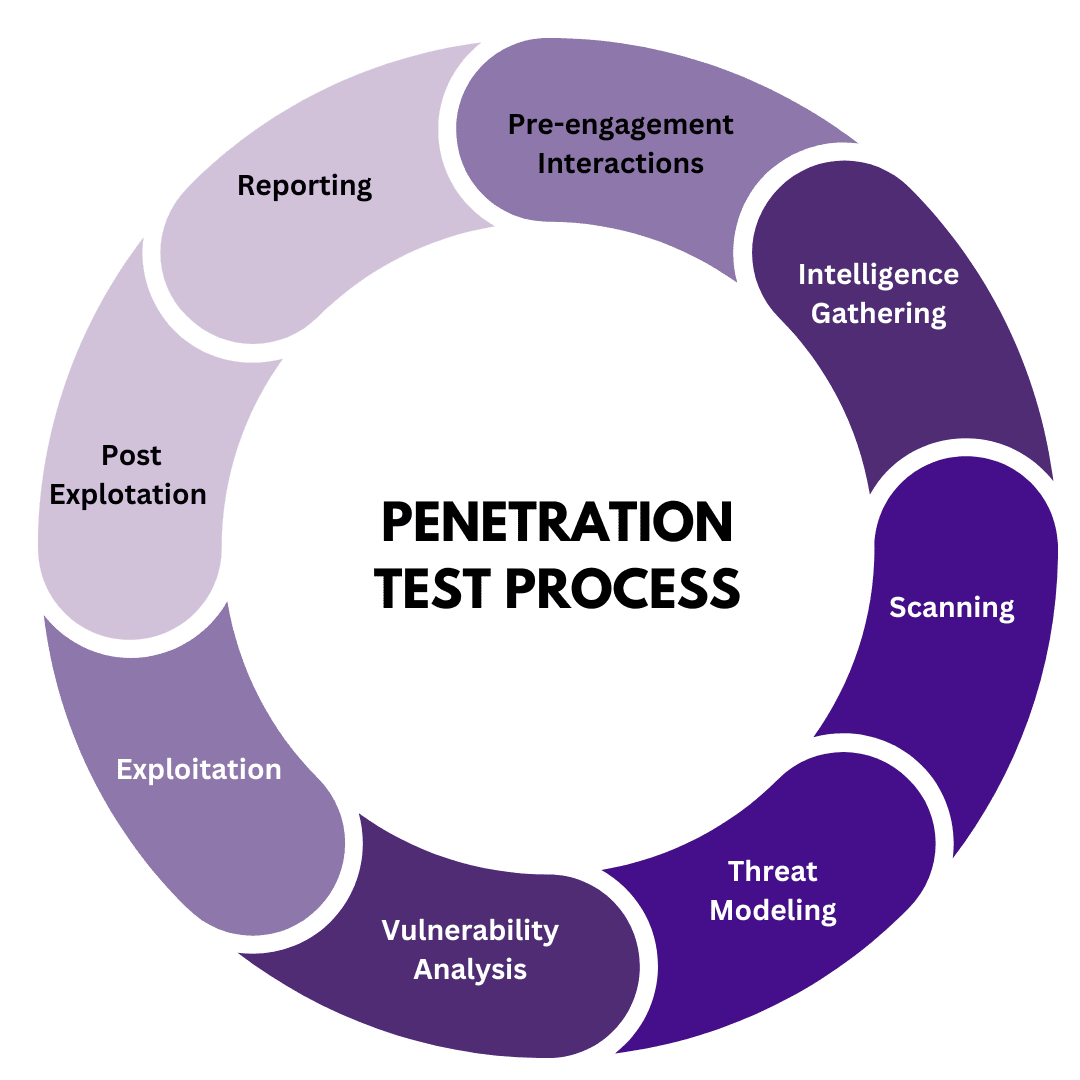
Penetration Testing Network Penetration Oppos Cybersecurity Penetration testing (or pen testing) is a security exercise where a cyber security expert attempts to find and exploit vulnerabilities in a computer system. the purpose of this simulated attack is to identify any weak spots in a system’s defenses which attackers could take advantage of. In this article, you will learn all about penetration testing – what it is, why each phase of the process is important, and the tools pentesters use to do their jobs. Learn what penetration testing is, why it is important, and how it can be applied to various areas and scenarios. explore different types of penetration testing, such as web applications, network infrastructure, social engineering, and more. The uk national cyber security center describes penetration testing as: "a method for gaining assurance in the security of an it system by attempting to breach some or all of that system's security, using the same tools and techniques as an adversary might." [7].
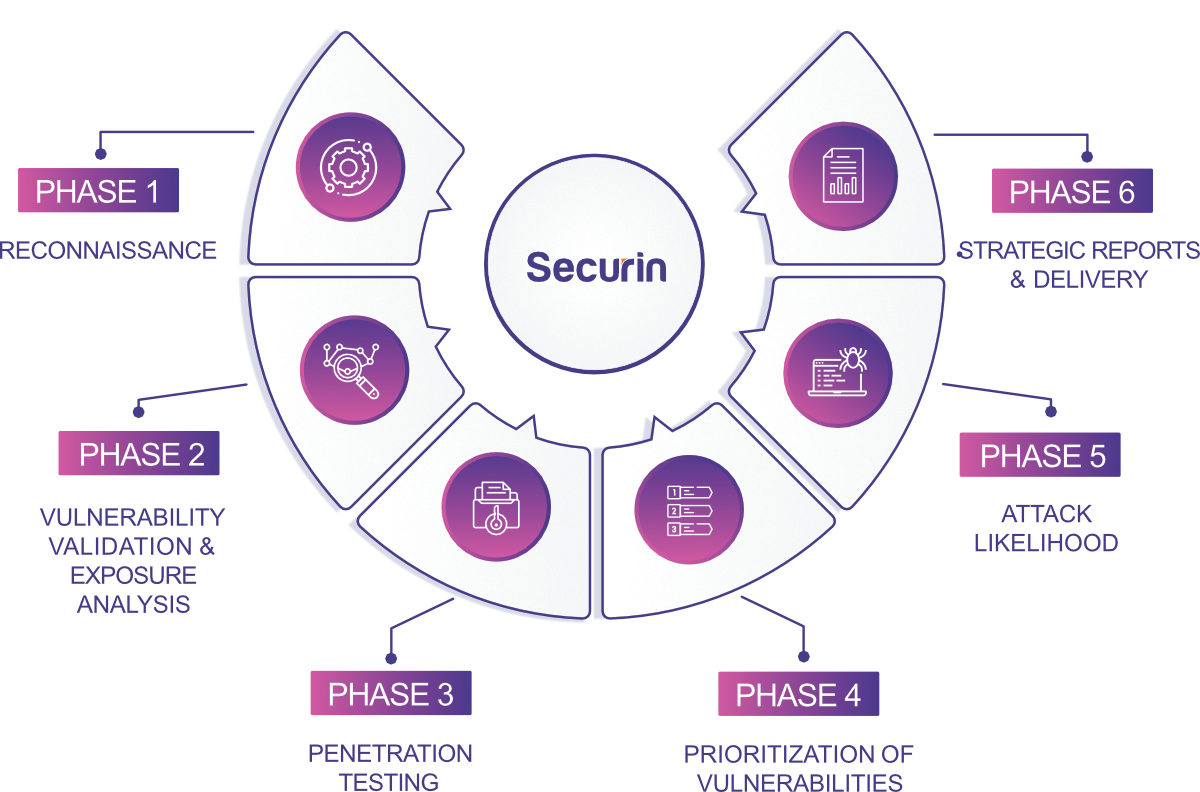
Securin Network Infrastructure Penetration Testing Learn what penetration testing is, why it is important, and how it can be applied to various areas and scenarios. explore different types of penetration testing, such as web applications, network infrastructure, social engineering, and more. The uk national cyber security center describes penetration testing as: "a method for gaining assurance in the security of an it system by attempting to breach some or all of that system's security, using the same tools and techniques as an adversary might." [7]. Penetration testing represents a critical cybersecurity practice that systematically evaluates an organization’s security posture through authorized simulated attacks. What is penetration testing (pen testing)? penetration testing is an important component of every organization’s cyber security. it finds weaknesses before your adversaries. learn how they work, their different types, and more. Penetration testing or pen testing, is a practice where a simulated cyber attack is conducted on your computer systems to find and fix any weak spots before real attackers can exploit them. Learn what penetration testing is, how it simulates real world cyber attacks, and why it is important for cybersecurity. explore the different types of pen tests, the mitre att&ck framework, and the best practices for conducting them.

Ai Based Application Penetration Testing Tools Types And Process Penetration testing represents a critical cybersecurity practice that systematically evaluates an organization’s security posture through authorized simulated attacks. What is penetration testing (pen testing)? penetration testing is an important component of every organization’s cyber security. it finds weaknesses before your adversaries. learn how they work, their different types, and more. Penetration testing or pen testing, is a practice where a simulated cyber attack is conducted on your computer systems to find and fix any weak spots before real attackers can exploit them. Learn what penetration testing is, how it simulates real world cyber attacks, and why it is important for cybersecurity. explore the different types of pen tests, the mitre att&ck framework, and the best practices for conducting them.

Top 10 Penetration Testing Methodologies Expert Guide Penetration testing or pen testing, is a practice where a simulated cyber attack is conducted on your computer systems to find and fix any weak spots before real attackers can exploit them. Learn what penetration testing is, how it simulates real world cyber attacks, and why it is important for cybersecurity. explore the different types of pen tests, the mitre att&ck framework, and the best practices for conducting them.
Comments are closed.