Cybersecurity Exercises Guide Pdf Encryption Key Cryptography

Chapter 3 Cryptography And Encryption Techniques Pdf Cryptography This document outlines an introduction to cryptography exercises. it begins with cracking a coded message by using online tools like boxentriq cryptogram solver and cyberchef. Exercise 12: your opponent has invented a new stream cipher mode of operation for 128 bit key aes. he thinks that ofb could be improved by feeding back into the key port rather than the data port of the aes chip.

Cyber Security Lab Symmetric Key Encryption Techniques Pdf Cipher Exercise 1.3 design a perfectly secure encryption scheme diferent from the otp such that m = k = c = {0, 1}n. Asymmetric or public key algorithms: different keys, which cannot be derived from each other. public key can be published without compromising private key. By the end of the exercise you will know what encryption, decryption, and cryptography are and how you can build your own method to send and receive secret messages. By nadia karichev cryptography is the practice of techniques for secure communication in the presence of third par ties. encryption is the process of hidi. g or transforming data into a secretive data only the party that knows the key is.

Lab1 Encryption Pdf Key Cryptography Cryptography By the end of the exercise you will know what encryption, decryption, and cryptography are and how you can build your own method to send and receive secret messages. By nadia karichev cryptography is the practice of techniques for secure communication in the presence of third par ties. encryption is the process of hidi. g or transforming data into a secretive data only the party that knows the key is. Observe that, in this way, linear encryption is a two party elgamal encryption: a ciphertext can only be decrypted with the collaboration of two parties a and b, holding each one one of the two secret values. Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k. Exercise 2: analyze the security of the shift, substitution and vigenere ciphers under known plaintext and chosen plaintext attacks. how much known or chosen plaintext is needed for the adversary to completely recover the key. In this challenge, students begin with data representation and are taken on a scaffolded progression through different types of ciphers, how they can work for encryption and decryption, and some of the programming techniques necessary to implement them.
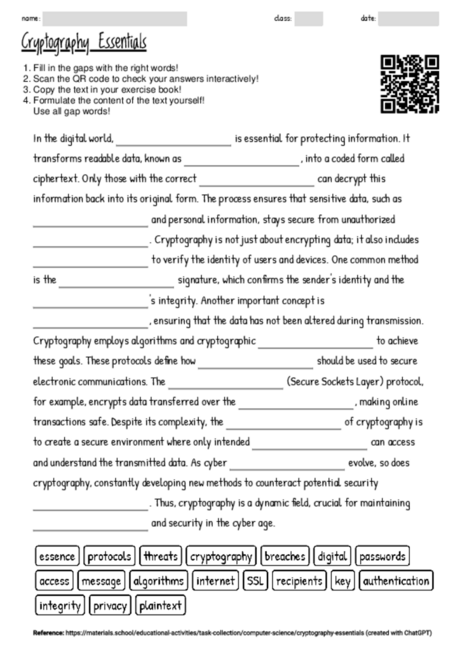
Worksheet With The Topic Cryptography Essentials Materials School Observe that, in this way, linear encryption is a two party elgamal encryption: a ciphertext can only be decrypted with the collaboration of two parties a and b, holding each one one of the two secret values. Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k. Exercise 2: analyze the security of the shift, substitution and vigenere ciphers under known plaintext and chosen plaintext attacks. how much known or chosen plaintext is needed for the adversary to completely recover the key. In this challenge, students begin with data representation and are taken on a scaffolded progression through different types of ciphers, how they can work for encryption and decryption, and some of the programming techniques necessary to implement them.

Symmetric Key Encryption Overview Pdf Cryptography Cryptanalysis Exercise 2: analyze the security of the shift, substitution and vigenere ciphers under known plaintext and chosen plaintext attacks. how much known or chosen plaintext is needed for the adversary to completely recover the key. In this challenge, students begin with data representation and are taken on a scaffolded progression through different types of ciphers, how they can work for encryption and decryption, and some of the programming techniques necessary to implement them.
Comments are closed.