Cybersecurity Essentials Threat Modeling Sboms Compliance Documentation
Threat Modeling Meets The Sbom Why Continuous Is Key Reversinglabs This report from the netherlands national cyber security centre (ncsc) captures the state of the sbom landscape and the potential purposes and uses of sbom in a cybersecurity context. Learn about key documentation requirements, threat modeling strategies, sbom creation and management, and different types of testing.
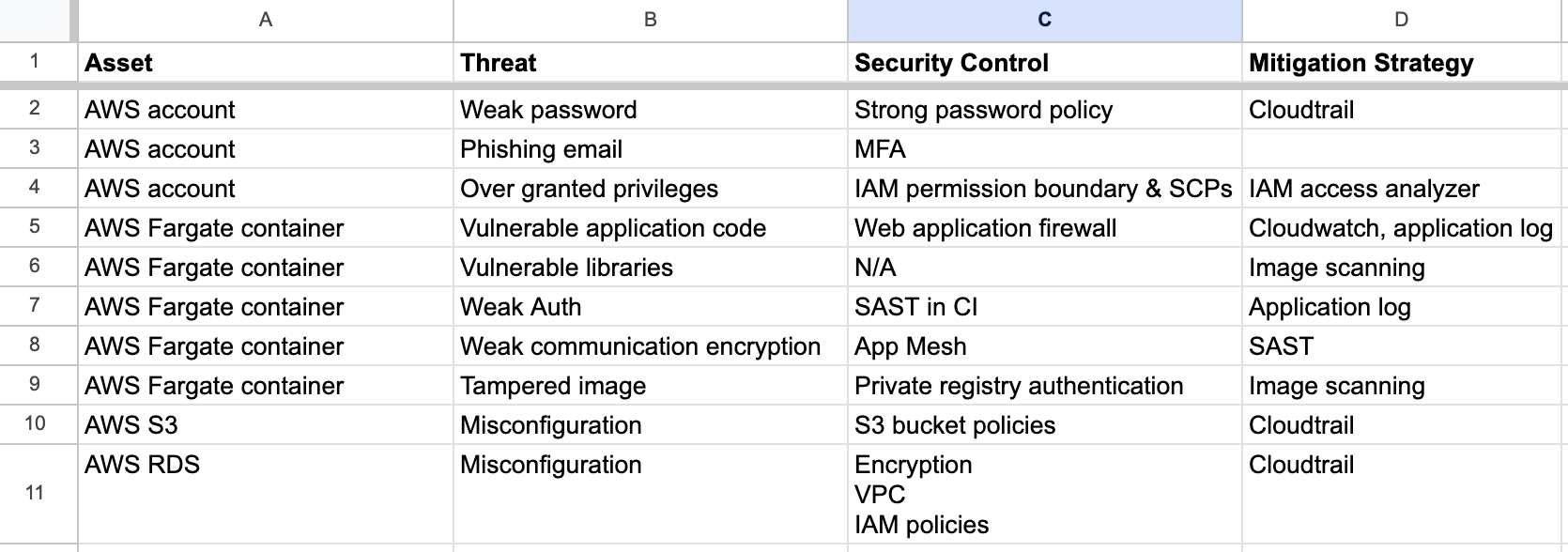
Threat Modeling Templates Kwm This guidance, authored by the u.s. cybersecurity and infrastructure security agency (cisa) and the following partners0f1, presents a shared vision of software bill of materials (sbom) and the value that increased software component and supply chain transparency can offer the global community. Update documentation and reports regularly: keep detailed records of sboms for each software release, crucial for audits and compliance checks. conduct regular audits of sboms to ensure accuracy and completeness, using these audits to identify gaps and improve the sbom generation process. Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. Learn about proposed updates to the minimum elements of sboms and how these have evolved in recent years. on august 22, 2025, the cybersecurity & infrastructure security agency (cisa) released a draft 2025 guide for software bill of materials (sbom).

Mastering Threat Modeling Ultimate Resource Guide For Cybersecurity Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. Learn about proposed updates to the minimum elements of sboms and how these have evolved in recent years. on august 22, 2025, the cybersecurity & infrastructure security agency (cisa) released a draft 2025 guide for software bill of materials (sbom). This guide will break down the biggest sbom compliance regulations in effect today, including timelines, impacted organizations, and technical requirements. it will also provide a brief overview of sbom recommendations that could conceivably become requirements in the years ahead. This cybersecurity information sheet (csi) highlights best practices and provides recommendations for users of national security systems (nss) to help them incorporate sbom management functions. Threat modeling visualizes systems and documents specific risks tied to real architectural decisions, enabling security teams to demonstrate compliance with id.ra‑1 through id.ra‑5. This document describes specific operations that software producers and consumers can perform on sbom data to draw valuable insights that can be applied to improve security risk decisions for software.

Balancing Compliance And Confidentiality With Sboms This guide will break down the biggest sbom compliance regulations in effect today, including timelines, impacted organizations, and technical requirements. it will also provide a brief overview of sbom recommendations that could conceivably become requirements in the years ahead. This cybersecurity information sheet (csi) highlights best practices and provides recommendations for users of national security systems (nss) to help them incorporate sbom management functions. Threat modeling visualizes systems and documents specific risks tied to real architectural decisions, enabling security teams to demonstrate compliance with id.ra‑1 through id.ra‑5. This document describes specific operations that software producers and consumers can perform on sbom data to draw valuable insights that can be applied to improve security risk decisions for software.
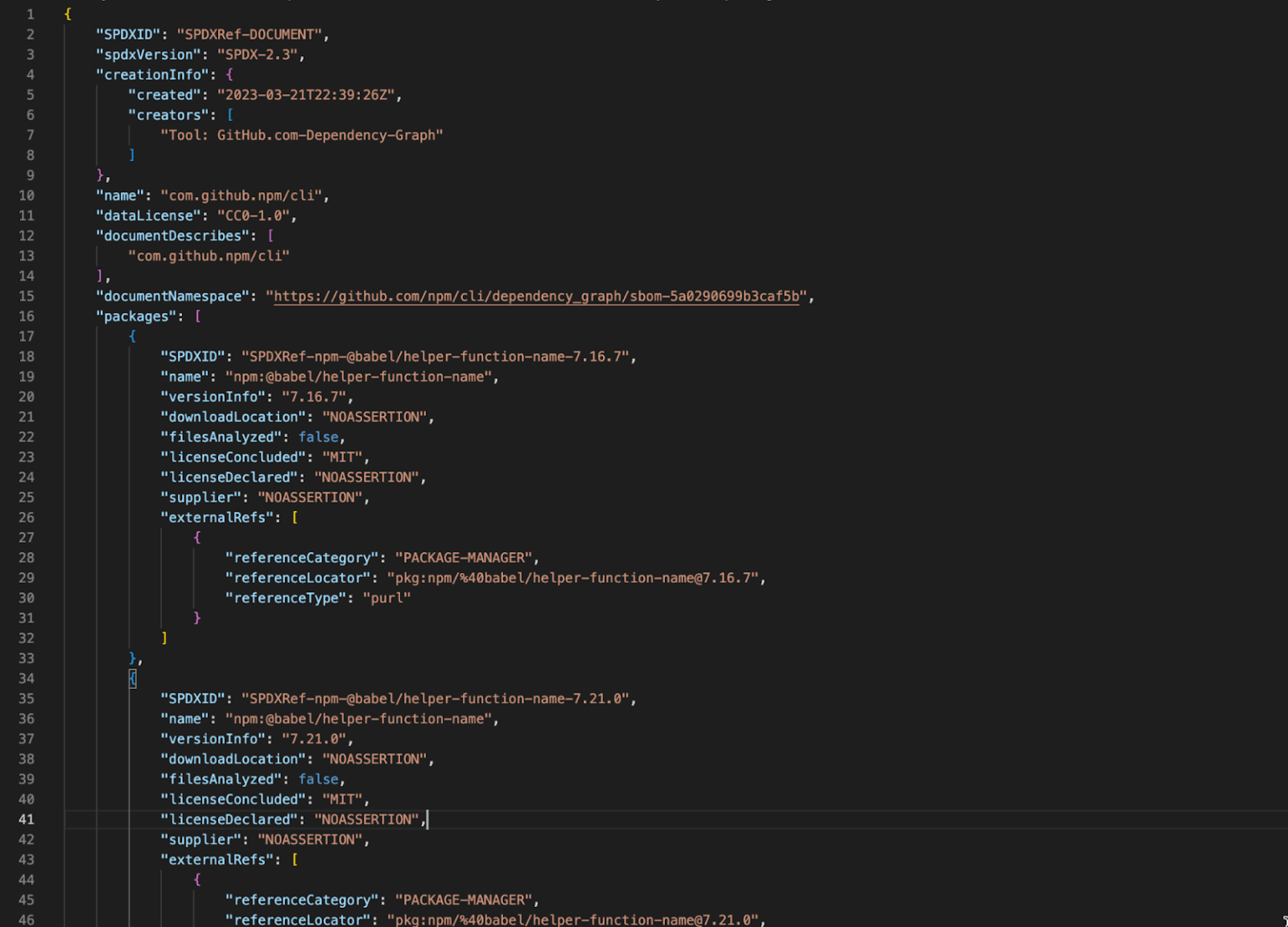
Introducing Self Service Sboms The Github Blog Threat modeling visualizes systems and documents specific risks tied to real architectural decisions, enabling security teams to demonstrate compliance with id.ra‑1 through id.ra‑5. This document describes specific operations that software producers and consumers can perform on sbom data to draw valuable insights that can be applied to improve security risk decisions for software.

S2l1 What Is Threat Modeling Documentation Pdf
Comments are closed.