Cybersecurity Data Security And Data Access Must Be Recognized First

Cybersecurity Data Security And Data Access Must Be Recognized First Data security is the process of maintaining the confidentiality, integrity, and availability of an organization’s data in a manner consistent with the organization’s risk strategy. before an incident happens, companies must have a security architecture and response plan in place. Access data governance is an essential component in cloud security, since unauthorized exposure of sensitive data is typically the first step to a cybersecurity attack, such as ransomware or ip theft.

Preventing Unauthorized Access Best Practices For Data Security Rec 01 – business operations resumption: residual security risks for systems (infrastructure, operating systems, applications and data), including inherited and shared security risks, are accepted prior to the resumption of normal business operations following cyber security incidents. Learn data security compliance requirements and best practices to protect information across systems. This article outlines a framework for data privacy and protection, explores strategies to secure information across digital ecosystems, and shares best practices for identifying, minimizing, and controlling data risks while ensuring global regulatory compliance. Learn about key data security standards and how they help businesses protect sensitive data, mitigate cyber risks, and ensure compliance.
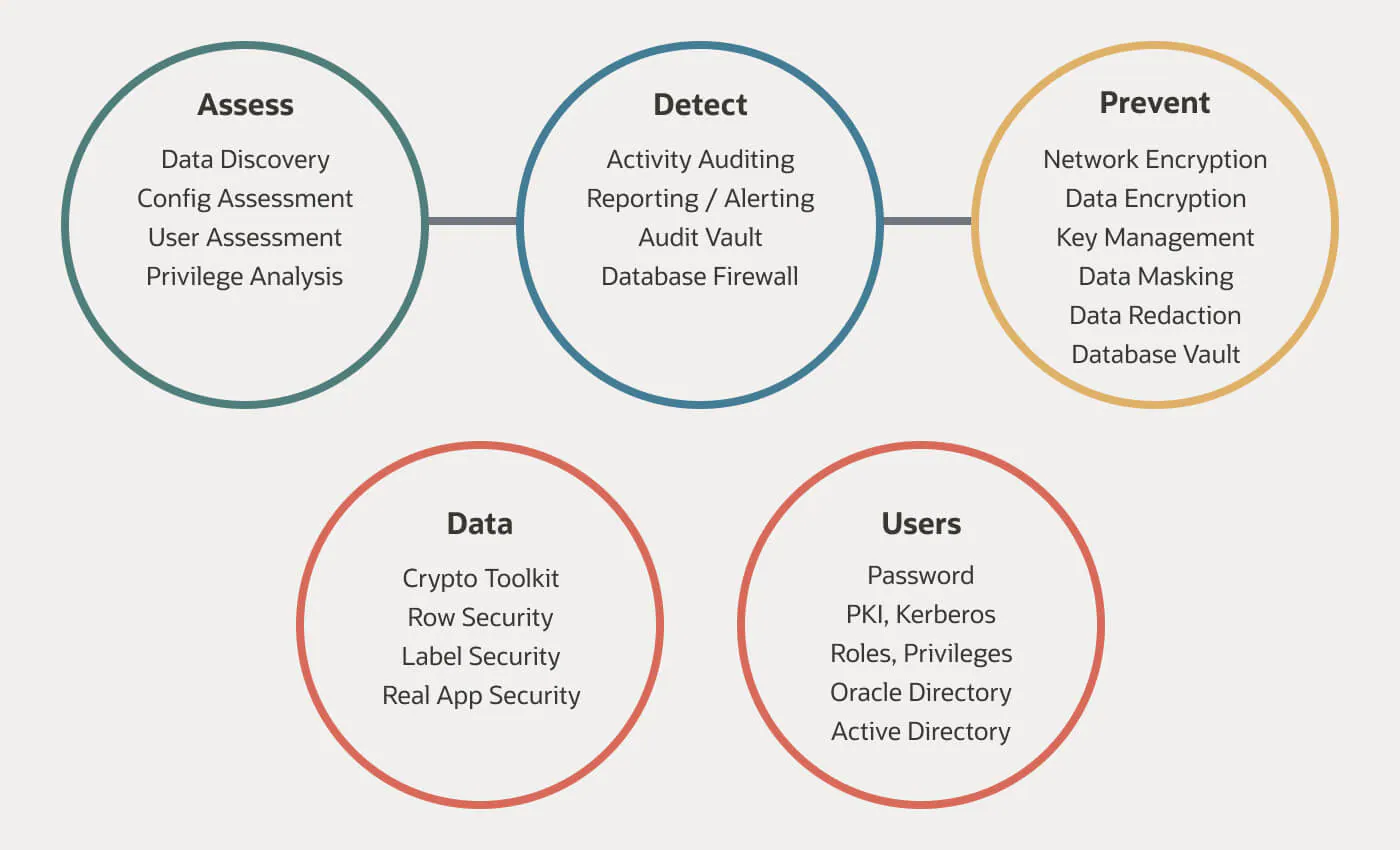
Data Security First Logic This article outlines a framework for data privacy and protection, explores strategies to secure information across digital ecosystems, and shares best practices for identifying, minimizing, and controlling data risks while ensuring global regulatory compliance. Learn about key data security standards and how they help businesses protect sensitive data, mitigate cyber risks, and ensure compliance. Learn how to achieve data security compliance with our step by step guide. explore key regulations, best practices, and compliance requirements. This guide explores the most widely adopted data security standards, outlines key regulatory frameworks, and shares actionable best practices tailored to modern enterprises. A key principle of the uk gdpr is that you process personal data securely by means of ‘appropriate technical and organisational measures’ – this is the ‘security principle’. doing this requires you to consider things like risk analysis, organisational policies, and physical and technical measures. Effective data access management is vital for organizations to secure their data and allow authorized users to access it easily. organizations face challenges like maintaining data integrity and preventing unauthorized access, making strong security measures essential.
Comments are closed.