Cybersecurity Basics Phishing Spoofing Impersonation And More

The Phishing Impersonation Protection Handbook Cyberint Phishing and spoofing attacks are similar, but they are two distinct cybersecurity threats. understanding the difference between phishing and spoofing and the dangers they pose can boost your cybersecurity awareness and help you protect your business. Explore the key spoofing vs phishing comparison in cybersecurity: how attackers impersonate versus deceive to steal data and credentials.
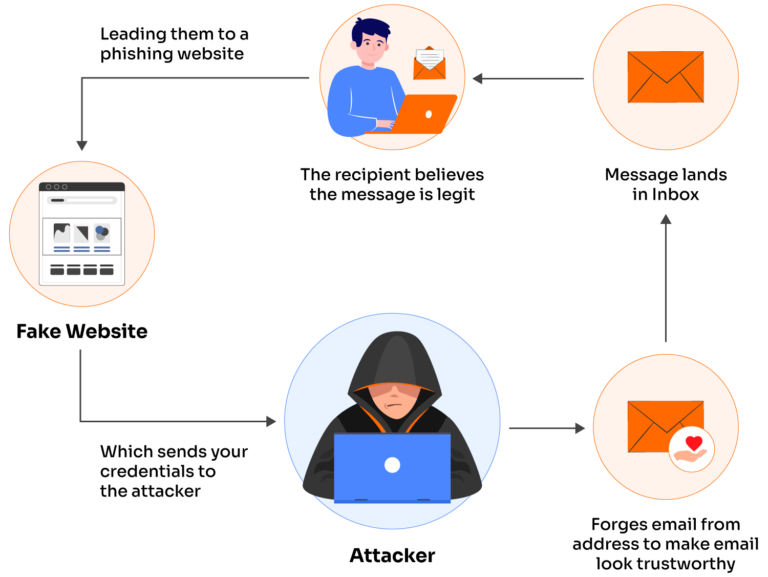
Phishing Vs Spoofing What S The Difference Valimail Spoofing can be used to gain access to the victim's login credentials, while phishing can be used to steal credit card details, passwords, and other sensitive information. Join dani to learn all about the basics of cybersecurity with topics including spoofing, phishing (email fraud), vishing (phone call fraud), smishing (text message fraud), impersonation,. Learn the difference between spoofing and phishing attacks and discover simple steps to protect yourself and your data online. Understand the key differences between spoofing vs phishing, their risks, examples, and how to protect against these cyber threats.

Phishing Vs Spoofing And How To Avoid It Bank Of Commerce Learn the difference between spoofing and phishing attacks and discover simple steps to protect yourself and your data online. Understand the key differences between spoofing vs phishing, their risks, examples, and how to protect against these cyber threats. Discover spoofing attacks with types, examples, risks and prevention methods to help you stay safe from phishing, fraud and data theft. Almost any type of cyberattack can start with spoofing or phishing, so knowing how to spot these tactics is a critical safety net your organization needs to have. this blog breaks down the key differences between spoofing and phishing in the wild. Email impersonation, email spoofing, and account takeover what are they, and is there any difference between them? this article will explain the operations and dynamics of these three types of threats and how to prevent cyber attacks from damaging your organization. In this article, we’ll explore the differences between email spoofing and email impersonation, explain their risks, and offer practical advice on how to defend against them.

The Difference Between Phishing Spoofing Discover spoofing attacks with types, examples, risks and prevention methods to help you stay safe from phishing, fraud and data theft. Almost any type of cyberattack can start with spoofing or phishing, so knowing how to spot these tactics is a critical safety net your organization needs to have. this blog breaks down the key differences between spoofing and phishing in the wild. Email impersonation, email spoofing, and account takeover what are they, and is there any difference between them? this article will explain the operations and dynamics of these three types of threats and how to prevent cyber attacks from damaging your organization. In this article, we’ll explore the differences between email spoofing and email impersonation, explain their risks, and offer practical advice on how to defend against them.
Comments are closed.