Cybersecurity Architecture Application Security

Application Security Architecture Securesky Strengthens Your Defenses Examples of a robust cybersecurity architecture include application security, access management, zero day attack prevention, cloud environment protection, antivirus programs, firewalls, and more. Application security architecture entails the systematic design and integration of security measures into software applications in order to prevent vulnerabilities and illegal access.

Cloud Application Security Architecture Framework Ppt Sample Enhance your digital defenses with expert insights on application security. discover strategies to protect your applications from vulnerabilities and cyber threats today. Responsible for ensuring that security requirements are adequately addressed in all aspects of enterprise architecture, including reference models, segment and solution architectures, and the resulting systems that protect and support organizational mission and business processes. Application security is the practice of designing, developing, testing, and maintaining secure applications. it covers the full lifecycle — from secure coding to runtime protection — and applies to web, mobile, desktop, and cloud native apps. Application security focuses on secure coding practices, vulnerability analysis, and software testing to reduce security risks in the production environment.

Secure Application Architecture Overview Pdf Design Use Case Application security is the practice of designing, developing, testing, and maintaining secure applications. it covers the full lifecycle — from secure coding to runtime protection — and applies to web, mobile, desktop, and cloud native apps. Application security focuses on secure coding practices, vulnerability analysis, and software testing to reduce security risks in the production environment. Explores the key components of a cyber security architecture and best practices to fortify your organization against modern threats. Application security is fundamental to protecting an organization by creating resilient systems. this architecture brief provides guidance for security and risk management professionals to ensure that security is pervasive throughout the application life cycle. It involves creating a structured approach to safeguard applications against vulnerabilities that can be exploited by malicious actors. this architecture includes various layers of protection, such as secure coding practices, authentication, encryption, and regular security testing. Cybersecurity can be effectively managed with an architecture based approach, composed with three viewpoints, namely system, security and process. using models for describing a system and its security objectives enables a systemic and exhaustive risk management process.
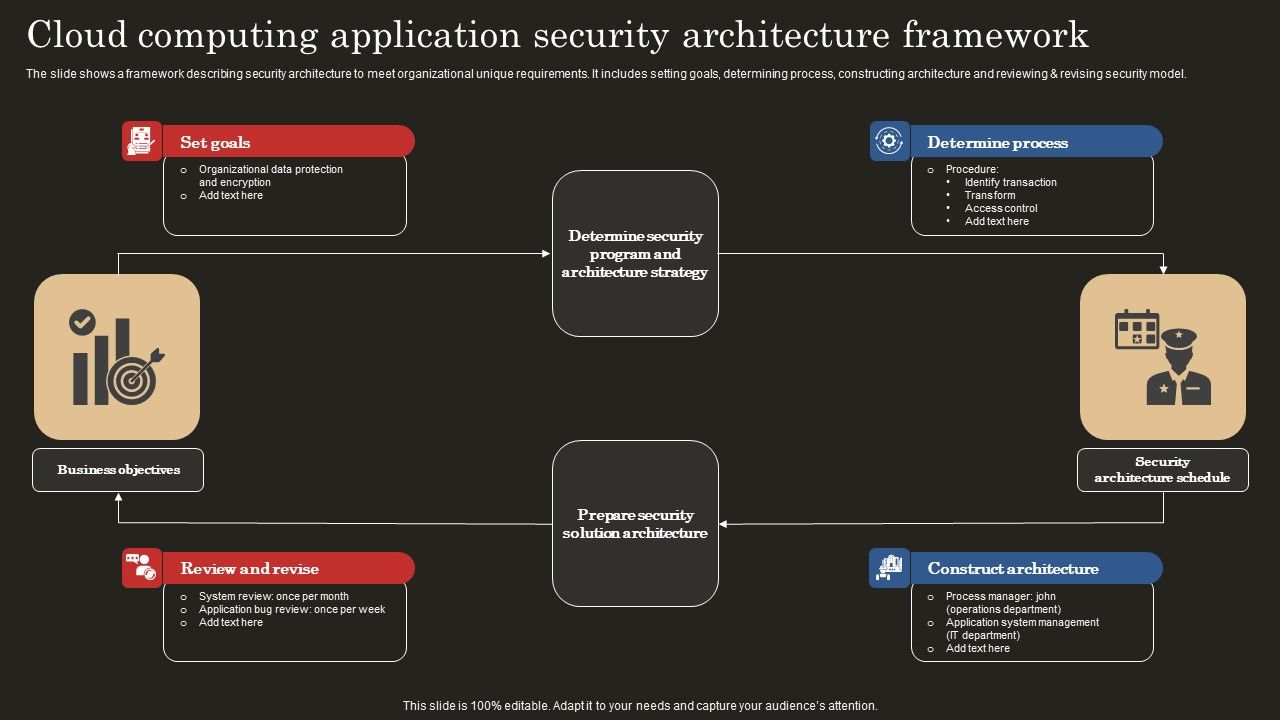
Cloud Computing Application Security Architecture Framework Elements Pdf Explores the key components of a cyber security architecture and best practices to fortify your organization against modern threats. Application security is fundamental to protecting an organization by creating resilient systems. this architecture brief provides guidance for security and risk management professionals to ensure that security is pervasive throughout the application life cycle. It involves creating a structured approach to safeguard applications against vulnerabilities that can be exploited by malicious actors. this architecture includes various layers of protection, such as secure coding practices, authentication, encryption, and regular security testing. Cybersecurity can be effectively managed with an architecture based approach, composed with three viewpoints, namely system, security and process. using models for describing a system and its security objectives enables a systemic and exhaustive risk management process.

Architecture Of Effective Application Security Implementation Ppt Sample It involves creating a structured approach to safeguard applications against vulnerabilities that can be exploited by malicious actors. this architecture includes various layers of protection, such as secure coding practices, authentication, encryption, and regular security testing. Cybersecurity can be effectively managed with an architecture based approach, composed with three viewpoints, namely system, security and process. using models for describing a system and its security objectives enables a systemic and exhaustive risk management process.

Expertise In Application Security Architecture Design
Comments are closed.