Cybersecurity 101 Mastering Authentication
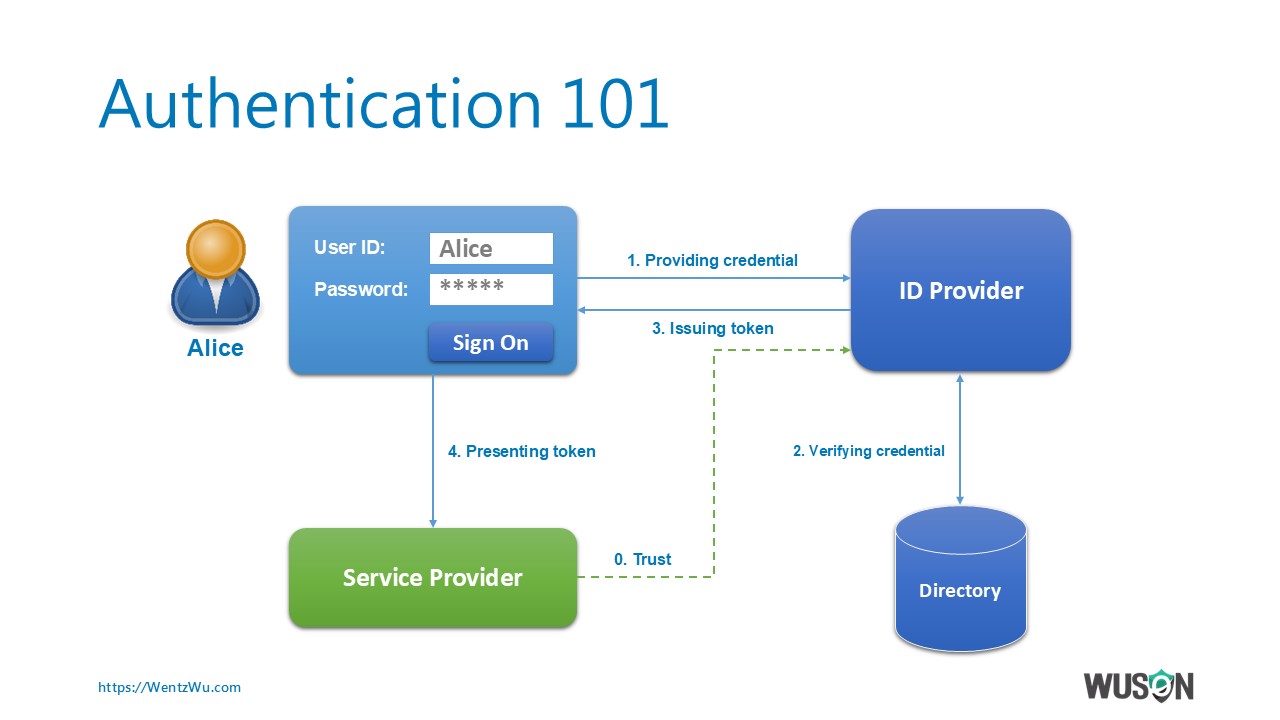
Authentication 101 By Wentz Wu Issap Issep Issmp Cissp Ccsp Csslp 🔐 cybersecurity 101: mastering authenticationready to level up your online security? 💻🔒in this must watch guide, we break down the power of authentication. Cybersecurity refers to the practice of protecting computer systems, networks, and data from theft, damage, or unauthorized access. in today’s digital age, with increasing threats and sophisticated cyber attacks, it’s crucial to safeguard personal, corporate, and government information.
Mastering Authentication Vulnerabilities Ultimate Course Expert Strong user authentication methods are the foundation of a robust cybersecurity strategy. implementing these best practices helps organizations mitigate risks, protect sensitive data, and provide users with secure access to systems and applications in a way that still preserves productivity:. Identity and access management (iam) is critical for protecting digital systems, data, and users. this course offers practical guidance for building, managing, and securing authentication systems in modern enterprises. Dive deep into the world of authentication. learn about types, steps, and real life examples to secure your digital identity. Secure authentication and authorization are a cornerstone of protecting against cybersecurity threats. learn about common identity based attacks, different authentication methods, and ways to protect against unauthorized access.
Mastering Cybersecurity Wow Ebook Dive deep into the world of authentication. learn about types, steps, and real life examples to secure your digital identity. Secure authentication and authorization are a cornerstone of protecting against cybersecurity threats. learn about common identity based attacks, different authentication methods, and ways to protect against unauthorized access. Learn about authentication types, processes, and real life examples. understand how authentication secures your online presence and data. As cyber threats like phishing have evolved, authentication has had to adapt. initially reliant on passwords, it now incorporates advanced methods such as biometrics and multi factor authentication (mfa). the challenge today is to strike a balance between strong security and seamless user experience. authentication vs authorization. Cybersecurity is an ongoing effort, and staying informed is your best defense. strong passwords and multi factor authentication are just the beginning—emerging technologies like biometrics and passwordless logins are shaping the future of secure access. Enter cybersecurity 101: adopting a security mindset. led by ai & cybersecurity expert jordan sauchuk, this course is designed to get you up to speed with core and foundational cybersecurity material.

Amazon Mastering Secure Authentication A Comprehensive Guide To Learn about authentication types, processes, and real life examples. understand how authentication secures your online presence and data. As cyber threats like phishing have evolved, authentication has had to adapt. initially reliant on passwords, it now incorporates advanced methods such as biometrics and multi factor authentication (mfa). the challenge today is to strike a balance between strong security and seamless user experience. authentication vs authorization. Cybersecurity is an ongoing effort, and staying informed is your best defense. strong passwords and multi factor authentication are just the beginning—emerging technologies like biometrics and passwordless logins are shaping the future of secure access. Enter cybersecurity 101: adopting a security mindset. led by ai & cybersecurity expert jordan sauchuk, this course is designed to get you up to speed with core and foundational cybersecurity material.
Comments are closed.