Cyber Threat Intelligence Use Cases

Cyber Threat Intelligence Use Cases Ppt Presentation Threat intelligence use cases encompass a wide range of activities and strategies aimed at identifying, mitigating, and responding to cyberthreats. the specific use cases that are most relevant to an organization depend on its industry, size, and unique cybersecurity needs. Explore common threat intelligence examples and use cases to learn how cyber intelligence strengthens security and aids proactive threat response.

Use Cases Of Cyber Threat Intelligence Ppt Powerpoint Discover the top 5 use cases and examples of threat intelligence solutions and learn how they can enhance your cybersecurity strategy and protect your organization. Explore cyber threat intelligence use cases for enterprises. discover strategic, tactical applications, industry examples, and ai driven cti strategies with informatix.systems solutions. There are four main types of threat intelligence, each with its own use cases and focus. here’s a closer look:. The 2026 x force threat intelligence index reveals that cybercriminals are exploiting basic security gaps at dramatically higher rates, now accelerated by ai tools that help attackers identify weaknesses faster than ever. read on for the biggest highlights from the report.
Ti Lookup Real World Use Cases From A Malware Researcher There are four main types of threat intelligence, each with its own use cases and focus. here’s a closer look:. The 2026 x force threat intelligence index reveals that cybercriminals are exploiting basic security gaps at dramatically higher rates, now accelerated by ai tools that help attackers identify weaknesses faster than ever. read on for the biggest highlights from the report. Learn what cyber threat intelligence is, including its types, sources, and real world use cases, and how it strengthens proactive cybersecurity defense. Threat intelligence is the process of gathering, analyzing, and interpreting information about potential or actual cyber threats to an organization. it’s a proactive approach that helps organizations understand the threat landscape, identify risks, and implement effective security measures. Learn the cyber threat intelligence lifecycle, its 6 phases, top tools, real world use cases, and best practices to build a proactive cybersecurity defence strategy. Cyber threat data collection provides raw information, which is initially not useful until it is analyzed and packaged into a useful format for security investigation. cyber threat intelligence builds on data collection and provides data that can be used to detect, block and mitigate threats. it leverages analysis to derive operational intelligence from raw security data—such as the types of.
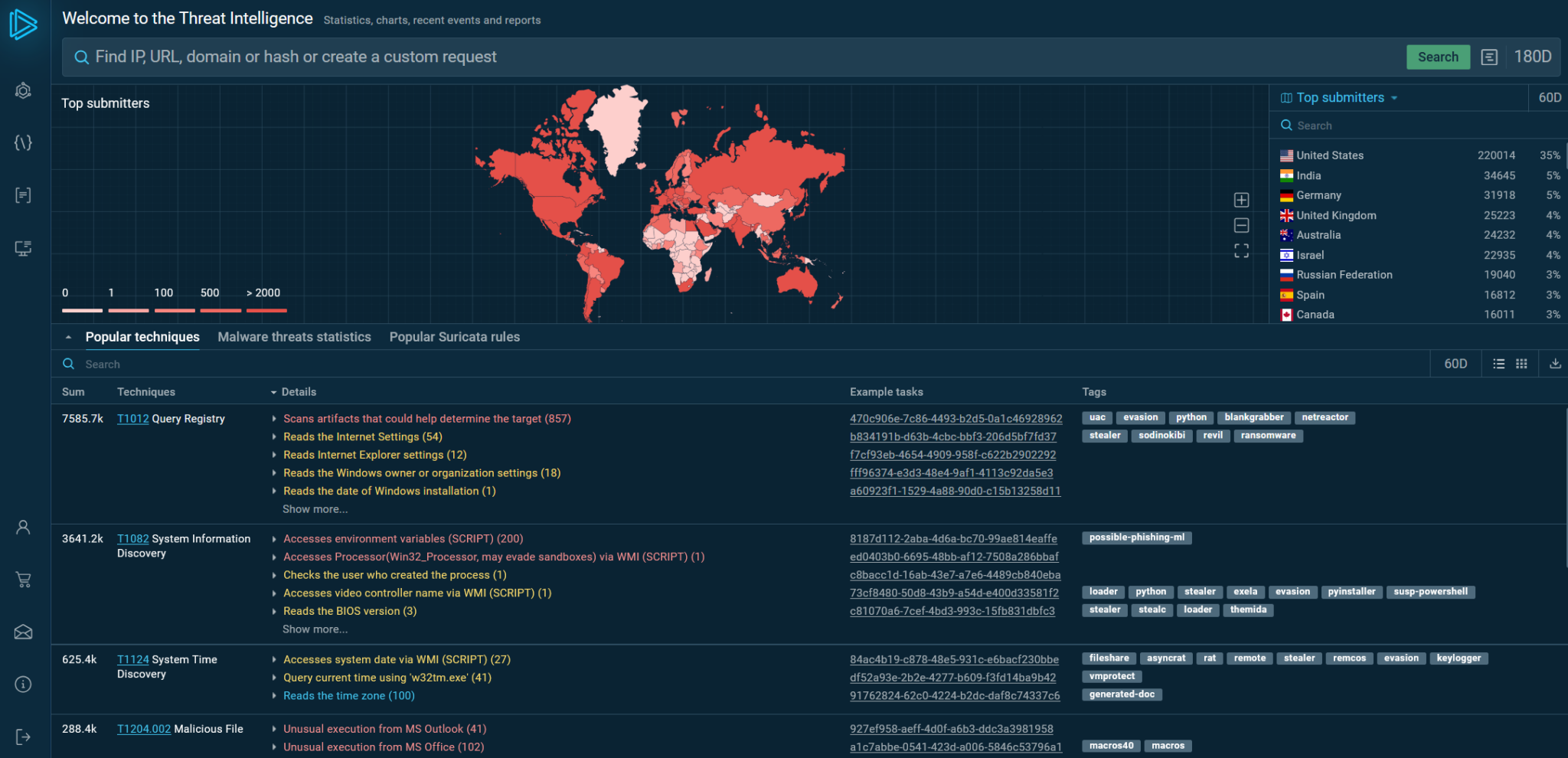
Ti Lookup Real World Use Cases From A Malware Researcher Learn what cyber threat intelligence is, including its types, sources, and real world use cases, and how it strengthens proactive cybersecurity defense. Threat intelligence is the process of gathering, analyzing, and interpreting information about potential or actual cyber threats to an organization. it’s a proactive approach that helps organizations understand the threat landscape, identify risks, and implement effective security measures. Learn the cyber threat intelligence lifecycle, its 6 phases, top tools, real world use cases, and best practices to build a proactive cybersecurity defence strategy. Cyber threat data collection provides raw information, which is initially not useful until it is analyzed and packaged into a useful format for security investigation. cyber threat intelligence builds on data collection and provides data that can be used to detect, block and mitigate threats. it leverages analysis to derive operational intelligence from raw security data—such as the types of.
Comments are closed.