Cyber Threat Intelligence Pdf

Cyber Threat Intelligence Pdf Pdf Cyberwarfare Security Organizations need to gather and share real time cyber threat information and to transform it to threat intelligence in order to prevent attacks or at least execute timely disaster recovery. The guide emphasizes the critical importance of cyber threat intelligence in today's security landscape. it outlines essential activities such as developing intelligence requirements, collecting and analyzing data, and utilizing insights to bolster security measures.

Cyber Threat Intelligence Pdf Threat Computer Military Intelligence Learn what cyber threat intelligence is, how it is used, and how to select a supplier. this guide covers the key concepts, principles, levels, sources, types, and applications of cyber threat intelligence. In the simplest possible terms, cyber threat intelligence (cti) is the process of taking disparate pieces of information about a cyber attack and identifying the context in which it happened and what that means. Cyber threat intelligence free download as pdf file (.pdf), text file (.txt) or read online for free. The current state of cyber threat intelligence (cti) procedures and their implications for contemporary security contexts are clarified by interpreting the data in light of the study questions and objectives.
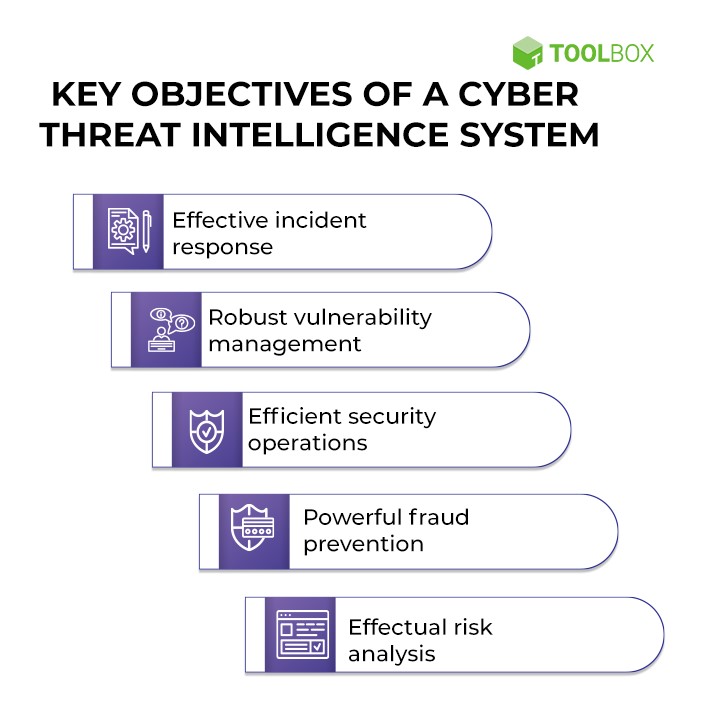
6 Steps To Building A Cyber Threat Intelligence Framework Cyber threat intelligence free download as pdf file (.pdf), text file (.txt) or read online for free. The current state of cyber threat intelligence (cti) procedures and their implications for contemporary security contexts are clarified by interpreting the data in light of the study questions and objectives. Nce has become a cornerstone of effective cybersecurity strategy. this white paper synthesizes the insights of leading government and industry experts, as captured in a recent panel discussion, to provide a comprehensive overview of the curren. Minimizing false positives (and false negatives) with cyber threat intelligence increase the effectiveness of the cyber defense. before using cti, it is important to define and understand it. About the survey as we navigate the ever evolving landscape of cybersecurity, understanding the latest trends and emerging threats is paramount. deloitte’s global cyber threat intelligence (cti) annual cyber threat trends 2025 report offers a comprehensive analysis of the cyberthreat environment, providing actionable insights to help organizations bolster their defenses and stay ahead of. It outlines the key concepts and principles that underpin cyber threat intelligence, along with the ways organisations use cyber threat intelligence to predict, prevent, detect and respond to potential cyber security threats and reduce the overall level of cyber risk faced.
Cyber Threat Intelligence How To Manage Security Strategically Nce has become a cornerstone of effective cybersecurity strategy. this white paper synthesizes the insights of leading government and industry experts, as captured in a recent panel discussion, to provide a comprehensive overview of the curren. Minimizing false positives (and false negatives) with cyber threat intelligence increase the effectiveness of the cyber defense. before using cti, it is important to define and understand it. About the survey as we navigate the ever evolving landscape of cybersecurity, understanding the latest trends and emerging threats is paramount. deloitte’s global cyber threat intelligence (cti) annual cyber threat trends 2025 report offers a comprehensive analysis of the cyberthreat environment, providing actionable insights to help organizations bolster their defenses and stay ahead of. It outlines the key concepts and principles that underpin cyber threat intelligence, along with the ways organisations use cyber threat intelligence to predict, prevent, detect and respond to potential cyber security threats and reduce the overall level of cyber risk faced.
Comments are closed.