Cyber Security Report Template
Cyber Security Incident Report Template In Word Pdf Google Docs Have ready with you a cybersecurity report template to help you begin writing the report. you will find detailed security report examples online that will help you create the structure correctly. Date and time discovered: how was the incident detected? (e.g., user report, monitoring system alert) detailed description of the incident (include what occurred, where, and how): was the incident ongoing at the time of report? ☐ yes ☐ no have any files, accounts, or systems been compromised? ☐ yes ☐ no.

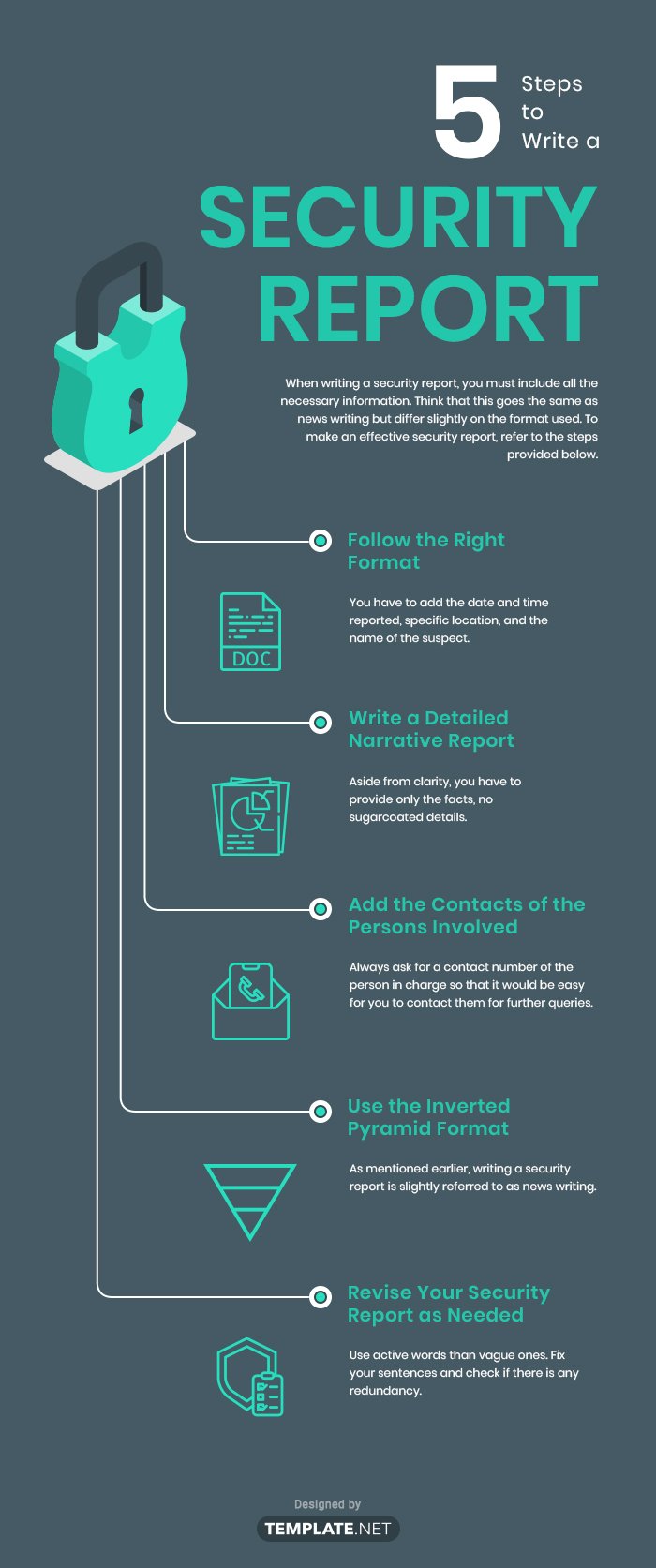
Free Cyber Security Templates To Edit Online Explore cybersecurity report examples, templates, and key components for effective security reporting—all in one blog. An it security incident report documents the particulars of a cyber attack on an organization’s networks, systems, or data. the report describes how and when the issue was found, the nature and extent of the breach, and the actions that were taken in response to the threat. Disclaimer nizations as a reference and guide. this template must be customized and aligned with the

Free Cyber Security Templates To Edit Online Disclaimer nizations as a reference and guide. this template must be customized and aligned with the
Cybersecurity Incident Report Template In Word Pdf Google Docs Below, you can view a sample cybersecurity incident report. this template is customizable using our document editor, you can then download the report in pdf or word format. You can make your one of a kind security report layout or download a cybersecurity report template on the web. the accompanying data is significant in your security report. A cybersecurity incident report includes information about a breach and its impact on services or data. the form assesses how the attacker entered the system and its effect afterward. An overview of the top three most popular cyber security reporting styles commonly requested by senior management and executive teams.
Cybersecurity Report Template A cybersecurity incident report includes information about a breach and its impact on services or data. the form assesses how the attacker entered the system and its effect afterward. An overview of the top three most popular cyber security reporting styles commonly requested by senior management and executive teams.
Comments are closed.