Cyber Security Internet Browsing Analysis Database Forensics

Forensics Analysis Of Privacy Of Portable Web Browsers Pdf Computer Overall, this paper contributes to a deeper understanding of browser forensic analysis and identifies key areas for enhancing privacy protection and forensic methodologies. For browser data acquisition, we employed foren sic browser analysis tools, sqlite database analysis, and browser specific extraction techniques. these tools are specifically designed to analyze and gather browser related artifacts.

Browser Forensics Special Info Pdf World Wide Web Internet Web Overall, this paper contributes to a deeper understanding of browser forensic analysis and identifies key areas for enhancing privacy protection and forensic methodologies. Digital investigations pertaining to criminal cases, cybersecurity incidents, or other illicit actions require important insights into people’s online behaviour, which can be obtained through the analysis of browser artifacts. Experimental results reveal vulnerabilities, such as crashes, that can lead to the loss of sensitive information. this methodology provides a promising foundation for advancing browser forensic analysis and enhancing cybercrime investigations. It is a powerful tool used by digital forensics professionals to extract, parse, and analyze browsing history and other relevant data from web browsers like google chrome and mozilla firefox.

Private Browsing Forensic Analysis A Case Study Pdf Computer Experimental results reveal vulnerabilities, such as crashes, that can lead to the loss of sensitive information. this methodology provides a promising foundation for advancing browser forensic analysis and enhancing cybercrime investigations. It is a powerful tool used by digital forensics professionals to extract, parse, and analyze browsing history and other relevant data from web browsers like google chrome and mozilla firefox. Db browser, combined with kape, provides a powerful toolkit for forensic analysis of browser artifacts. by following the steps outlined above, you can extract, analyze, and interpret data from popular web browsers, turning raw data into meaningful insights. Since so much activity is conducted using the browser online, we should be able to find artifacts or evidence of nearly all the suspect’s activity in the browser and its associated directories and databases. This article will explain what browser forensics are and the role they play in cybersecurity. we will discuss some of the challenges involved in implementing forensic analysis, before explaining the use case for in depth browser monitoring. Master web browser forensics with our guide. learn expert solutions for conducting browser forensics and recovering data from top engines.

Analysis Of Digital Forensic Techniques For Investigating Crimes On The Db browser, combined with kape, provides a powerful toolkit for forensic analysis of browser artifacts. by following the steps outlined above, you can extract, analyze, and interpret data from popular web browsers, turning raw data into meaningful insights. Since so much activity is conducted using the browser online, we should be able to find artifacts or evidence of nearly all the suspect’s activity in the browser and its associated directories and databases. This article will explain what browser forensics are and the role they play in cybersecurity. we will discuss some of the challenges involved in implementing forensic analysis, before explaining the use case for in depth browser monitoring. Master web browser forensics with our guide. learn expert solutions for conducting browser forensics and recovering data from top engines.

Web Browser Forensics Evidence Collection And Analysis For Most This article will explain what browser forensics are and the role they play in cybersecurity. we will discuss some of the challenges involved in implementing forensic analysis, before explaining the use case for in depth browser monitoring. Master web browser forensics with our guide. learn expert solutions for conducting browser forensics and recovering data from top engines.
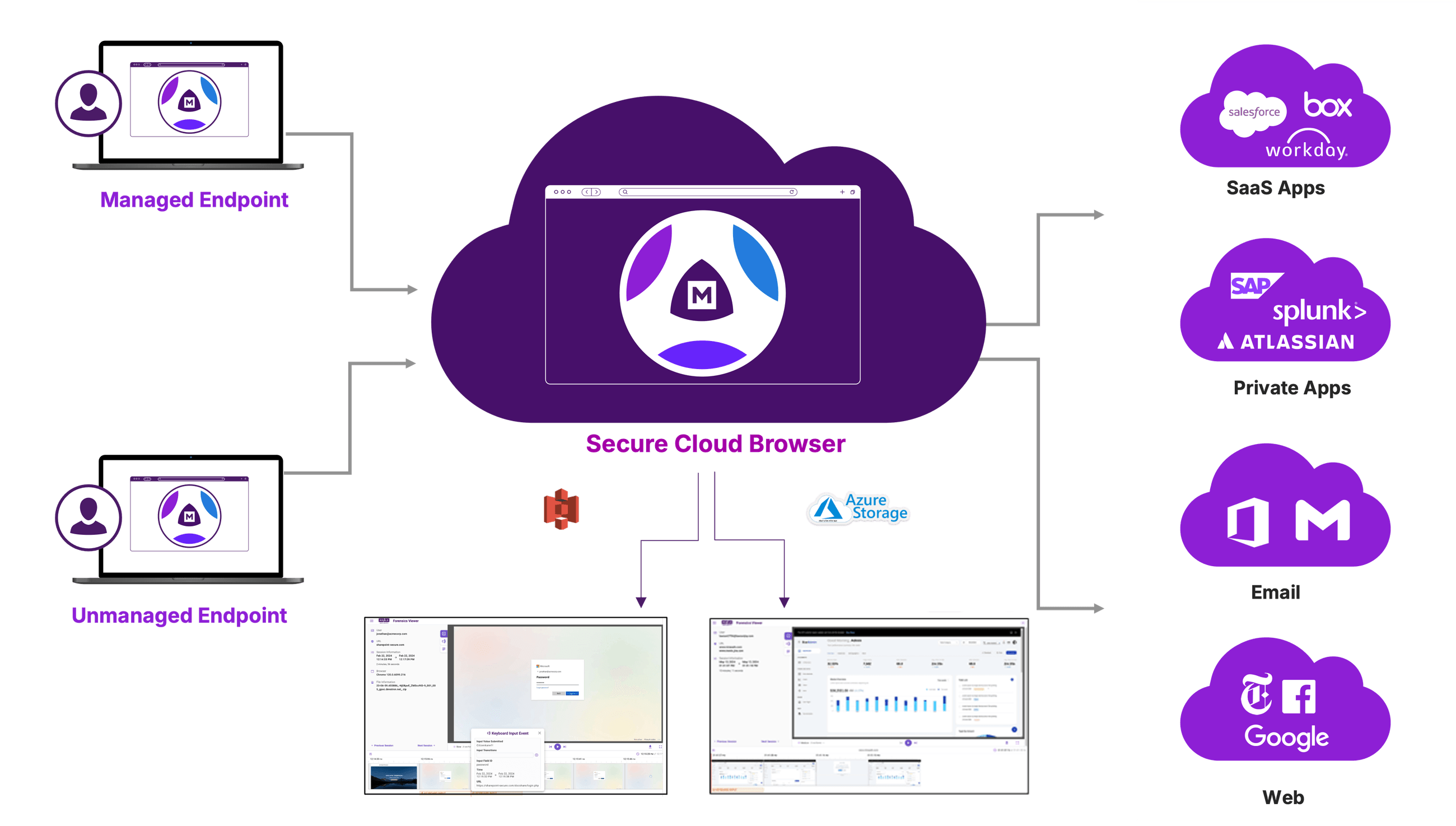
Browsing Forensics Menlo Security
Comments are closed.