Cyber Security Indirect Syscalls Shellcode Loader On Windows
Github Susmdt Indirect Syscall Shellcode Loader I decided to create a standalone shellcode loader, as this is simply easier to debug and does not need a cobalt strike license to play around. at a high level the loader re implements hellsgate but uses indirect instead of direct syscalls to make the callstack look less suspcicious. Be better than yesterday in this video, we will explore how we can setup and compile publicly available tools that utilise syscalls, such as the tartarus tpallocinject loader by nettitude.

Hadesldr Shellcode Loader Implementing Indirect Dynamic Syscall Api This page provides a high level introduction to the shellcodeloader indirect syscalls project, an educational shellcode loader that employs indirect syscalls and multiple evasion techniques to bypass user mode edr (endpoint detection and response) hooks. For this post, we’re going to cover a possible way to bypass signature analysis from av using obfuscation and nt api inspection from edr using indirect syscalls with a shellcode loader pe. For the purpose of this tutorial, we will implement our own indirect syscall loader that can operate reliably even when native functions are hooked. specifically, we’ll enhance our loader by integrating the halos gate approach to dynamically retrieve ssns under adversarial conditions. System calls are typically executed in ntdll.dll. to have our program invoke a syscall without the syscall coming from ntdll.dll is very suspicious and places extra unwanted scrutiny on our program. indirect syscalls attempt to remedy this by jumping to a syscall instruction located inside of ntdll.dll.
Shellcode Loader Windows Execution Callback Callwindowproc C Code Cpp For the purpose of this tutorial, we will implement our own indirect syscall loader that can operate reliably even when native functions are hooked. specifically, we’ll enhance our loader by integrating the halos gate approach to dynamically retrieve ssns under adversarial conditions. System calls are typically executed in ntdll.dll. to have our program invoke a syscall without the syscall coming from ntdll.dll is very suspicious and places extra unwanted scrutiny on our program. indirect syscalls attempt to remedy this by jumping to a syscall instruction located inside of ntdll.dll. This post documents an experimental shellcode execution project developed in c . the goal was to explore progressively more evasive techniques to defeat windows defender and similar avs, starting from basic encoding up to polymorphic loaders with indirect syscalls and api hashing. The code for this article is part of a shellcode loader implementing indirect dynamic syscall & api hashing and fileless shellcode using winsock2 can be found on this github repository. Dubbed indirect shellcode executor, the tool leverages the readprocessmemory function to inject shellcode, effectively avoiding standard api calls that security vendors monitor for malicious activity. Compiling on windows is recommended for anti virus evasion, as some products may categorize mingw compilation artefacts.
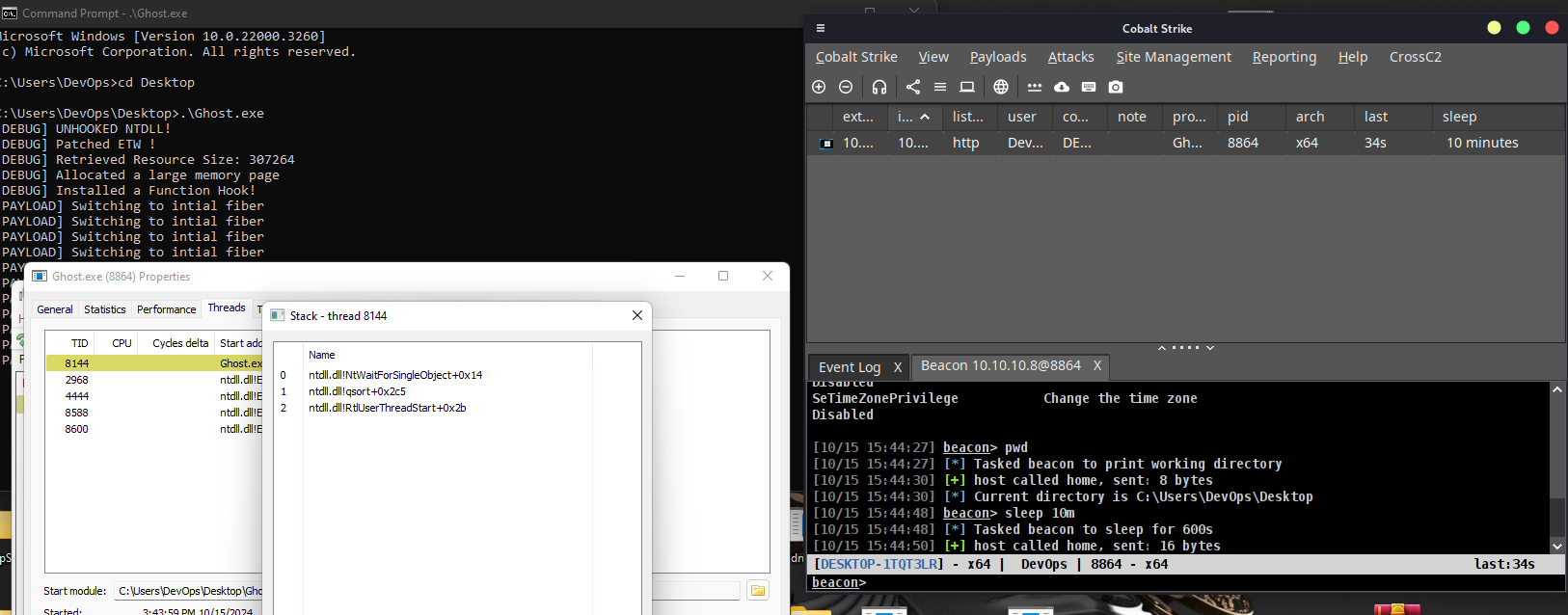
Ghost Evasive Shellcode Loader This post documents an experimental shellcode execution project developed in c . the goal was to explore progressively more evasive techniques to defeat windows defender and similar avs, starting from basic encoding up to polymorphic loaders with indirect syscalls and api hashing. The code for this article is part of a shellcode loader implementing indirect dynamic syscall & api hashing and fileless shellcode using winsock2 can be found on this github repository. Dubbed indirect shellcode executor, the tool leverages the readprocessmemory function to inject shellcode, effectively avoiding standard api calls that security vendors monitor for malicious activity. Compiling on windows is recommended for anti virus evasion, as some products may categorize mingw compilation artefacts.
Comments are closed.