Cyber Security And Open Source Intelligence Techniques Security
Open Source Intelligence Techniques Cybertalents In this paper, we have described the current state of osint tools techniques and the state of the art for various applications of osint in cyber security. in addition, we have discussed the challenges and future directions to develop autonomous models. The objectives of the study were outlined, including delving into the basics of osint, its use in cyber security and investigations of some selected tools and techniques employed in osint.
Open Source Intelligence Techniques Cybertalents This paper will provide a current and comprehensive summary of research connected with open source techniques. we will focus on the tools and techniques driving progress in the cybersecurity sector. Every method to be used for the safety of cyber security and the systems to be developed have some considerations. these relevant matters are explained in detail in table 1. Open source intelligence (osint) plays a crucial role in modern cybersecurity and threat assessment, serving as a key tool for organizations aiming to secure their digital resources. Ethical hackers leverage osint tools to gather information before performing security assessments. in this guide, we’ll explore osint fundamentals, its importance in cybersecurity, popular osint tools, and how they are used effectively.
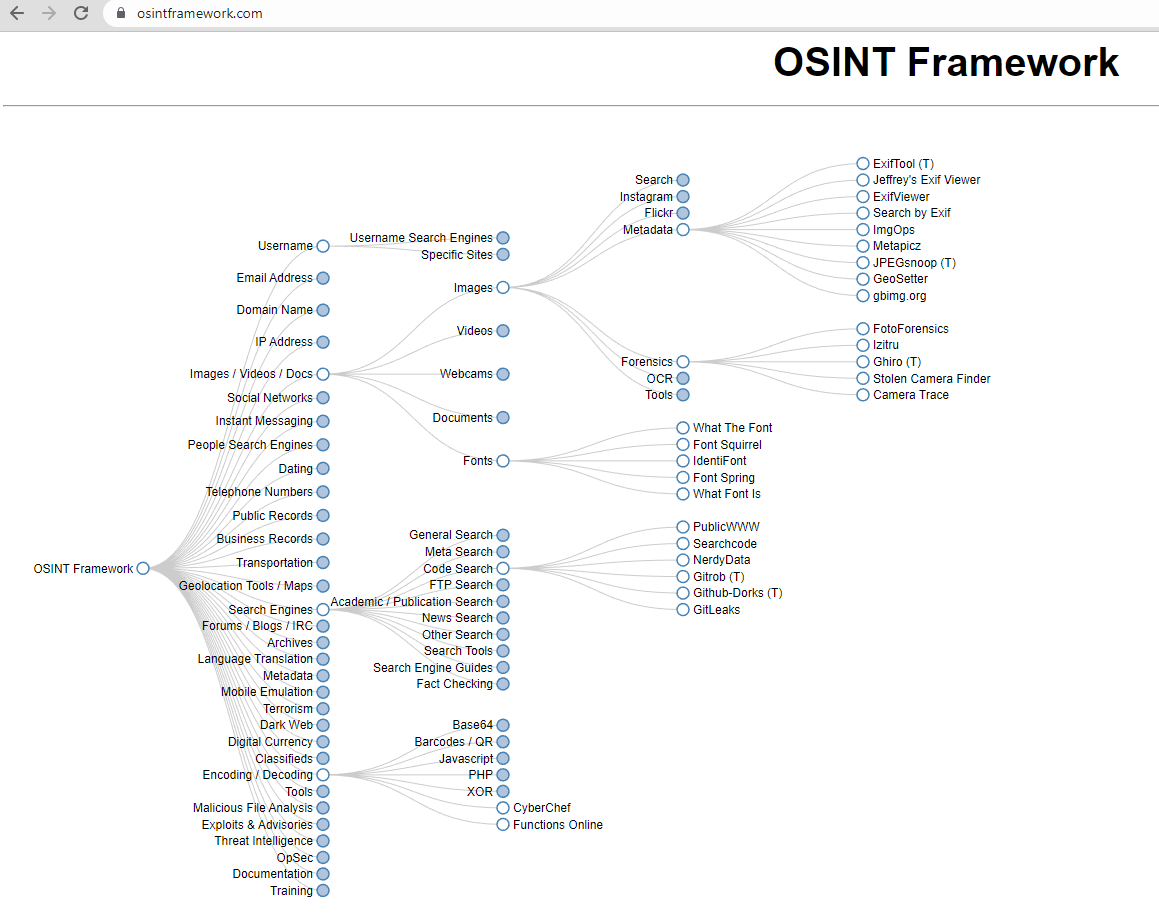
Open Source Intelligence Techniques Various Styles Brunofuga Adv Br Open source intelligence (osint) plays a crucial role in modern cybersecurity and threat assessment, serving as a key tool for organizations aiming to secure their digital resources. Ethical hackers leverage osint tools to gather information before performing security assessments. in this guide, we’ll explore osint fundamentals, its importance in cybersecurity, popular osint tools, and how they are used effectively. Purpose: the osint framework is not a tool itself, but rather a collection of resources and tools organized by category for conducting open source intelligence investigations. Understanding what osint is forms the foundation, but how exactly is open source intelligence leveraged practically in cybersecurity? let's explore how osint is actively used to detect threats, prevent cyberattacks, and strengthen your organization's defense strategies. Learn what open source intelligence (osint) is and how security teams use it. discover osint techniques and tools for threat detection. Explore the course syllabus below to view the full range of topics covered in sec587: advanced open source intelligence (osint) gathering and analysis. use this justification letter template to share the key details of this training opportunity with your boss.

Open Source Intelligence Techniques Various Styles Brunofuga Adv Br Purpose: the osint framework is not a tool itself, but rather a collection of resources and tools organized by category for conducting open source intelligence investigations. Understanding what osint is forms the foundation, but how exactly is open source intelligence leveraged practically in cybersecurity? let's explore how osint is actively used to detect threats, prevent cyberattacks, and strengthen your organization's defense strategies. Learn what open source intelligence (osint) is and how security teams use it. discover osint techniques and tools for threat detection. Explore the course syllabus below to view the full range of topics covered in sec587: advanced open source intelligence (osint) gathering and analysis. use this justification letter template to share the key details of this training opportunity with your boss.

Open Source Intelligence Techniques Cyberlearning Academy Learn what open source intelligence (osint) is and how security teams use it. discover osint techniques and tools for threat detection. Explore the course syllabus below to view the full range of topics covered in sec587: advanced open source intelligence (osint) gathering and analysis. use this justification letter template to share the key details of this training opportunity with your boss.

Cyber Security And Open Source Intelligence Techniques Security
Comments are closed.