Cyber Report Pdf Malware Information Security

Cyber Security Report Pdf The 2024 report explored current cybersecurity sentiment and security postures, views on ai powered cyber threats, and the impact of software supply chain attacks. Now in its fifth year, the global cybersecurity outlook has become an authoritative reference, empowering leaders with the insights they need to navigate cyber challenges, as well as an important instrument with which to redefine business strategy, enterprise investments and government initiatives and seize the opportunities of today’s cybersecurity landscape.

Executive Report Cyber Security Testing Pdf Security Computer Date and time discovered: how was the incident detected? (e.g., user report, monitoring system alert) detailed description of the incident (include what occurred, where, and how): was the incident ongoing at the time of report? ☐ yes ☐ no have any files, accounts, or systems been compromised? ☐ yes ☐ no. This report presents a comprehensive analysis of a malware sample proactively intercepted by our soc team during an attempted intrusion. the malware, delivered via the http protocol on port 80 from the ip address 192[.]166[.]244[.]243, located in hong kong, was successfully captured. While the 2024 cybersecurity landscape was marked by rapid changes in attacker strategies and types, we set out to identify which methods were most prevalent figure 1 shows the top threats observed over the past year. Malware is any harmful software that is designed to carry out malicious actions on a computer system. virus, worms, backdoors, trojans, backdoors and adware are some examples for malwares.

Cyber Security Download Free Pdf Security Computer Security While the 2024 cybersecurity landscape was marked by rapid changes in attacker strategies and types, we set out to identify which methods were most prevalent figure 1 shows the top threats observed over the past year. Malware is any harmful software that is designed to carry out malicious actions on a computer system. virus, worms, backdoors, trojans, backdoors and adware are some examples for malwares. Exploitation of vulnerabilities increased 55% compared to 2021. pdfs are the most popular file type for delivering malware as email attachments (66.6% of all attachments). The cyber security committee*2 discusses matters necessary for the implementation of cyber security measures at key group companies and how to respond to cyber security incidents that could develop into a crisis. Beyond the technical limitations of malware analysis tools and the staffing challenges of malware analysis experts, there were a few additional survey questions that yielded interesting results that didn’t quite fit elsewhere. This document provides a standardized format for reporting cyber security incidents at contractor facilities. the format is intended to document initial details of an incident and can be used to supplement national reporting requirements.
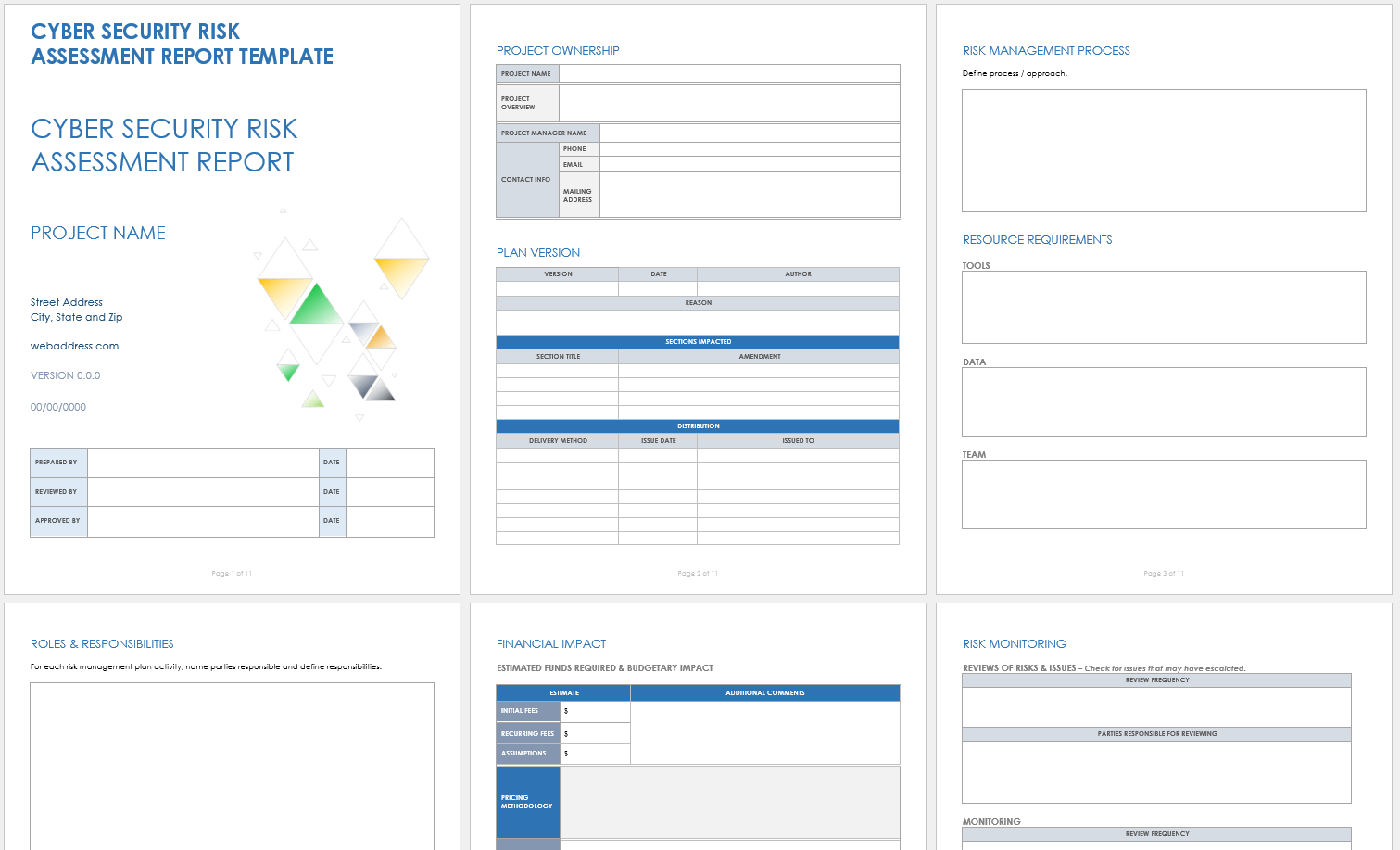
Cyber Security Report Template Exploitation of vulnerabilities increased 55% compared to 2021. pdfs are the most popular file type for delivering malware as email attachments (66.6% of all attachments). The cyber security committee*2 discusses matters necessary for the implementation of cyber security measures at key group companies and how to respond to cyber security incidents that could develop into a crisis. Beyond the technical limitations of malware analysis tools and the staffing challenges of malware analysis experts, there were a few additional survey questions that yielded interesting results that didn’t quite fit elsewhere. This document provides a standardized format for reporting cyber security incidents at contractor facilities. the format is intended to document initial details of an incident and can be used to supplement national reporting requirements.

Malware Report Pdf Malware Computer Virus
Comments are closed.