Cyber Attack Detection On Iot Project Pdf

Detection Of Cyber Attacks On Iot Based Cyber Phys Download Free Pdf Following a thorough literature review on machine learning methods and the necessity of iot security, this study will assess numerous ml algorithms for threat detection and the various security. We propose a novel hybrid framework combining ml based attack detection with llm based reasoning to analyze attack behavior and generate tailored mitigations for 13 different attack types in iot iiot networks.
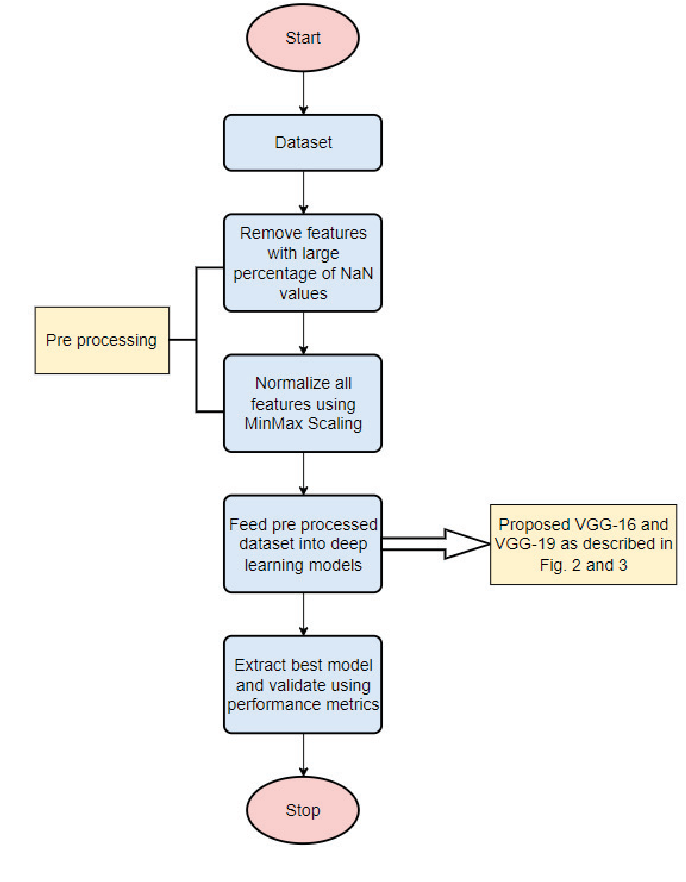
Figure 1 From Cyber Attack Detection In Iot Using Deep Learning We employ a combination of supervised, unsupervised, and hybrid ml models to identify key threats, including unauthorized access, data breaches, and denial of service (dos) attacks. the study uses a detailed dataset based on transient network traffic in iot systems for performance evaluation. Following a thorough literature review on machine learning methods and the necessity of iot security, this study will assess numerous ml algorithms for threat detection and the various security methods which are associated with machine learning techniques. Following a thorough literature review on machine learning methods and the necessity of iot security, this study will assess numerous ml algorithms for threat detection and the various security methods, which are associated with machine learning techniques. Our solution combines a mix of gradient boosting, convolutional neural networks (cnns), long short term memory networks (lstms), and recurrent neural networks (rnns) trained on massive iot datasets to identify and categorize network trafic patterns suggestive of possible cyber hazards.

Pdf A Honeypot Based Cyber Attack Detection System For Iot Devices Following a thorough literature review on machine learning methods and the necessity of iot security, this study will assess numerous ml algorithms for threat detection and the various security methods, which are associated with machine learning techniques. Our solution combines a mix of gradient boosting, convolutional neural networks (cnns), long short term memory networks (lstms), and recurrent neural networks (rnns) trained on massive iot datasets to identify and categorize network trafic patterns suggestive of possible cyber hazards. G, y. liu, machine learning based intrusion detection systems for iot: a comparative analysis. this paper compares various machine learning based intrusion detection systems applied to iot environments. it evaluates the performance of algorit. To address these issues, we propose a deep learning based novel method to detect cybersecurity vulnerabilities and breaches in cyber physical systems. the proposed framework contrasts the unsupervised and deep learning based discriminative approaches. Iot networks have become an increasingly valuable target of malicious attacks due to the increased amount of valuable user data they contain. in response, network intrusion detection systems have been developed to detect suspicious network activity. Ncreased vulnerability to sophisticated cyber threats. this project presents an advanced ai powered intrusion detection system (ids) tailored for iot environments, combining convolutional neural networks (cnn), long short term memory (lstm), spiking neural networks (snn), and isolati.

Pdf Energy Analysis Based Cyber Attack Detection By Iot With G, y. liu, machine learning based intrusion detection systems for iot: a comparative analysis. this paper compares various machine learning based intrusion detection systems applied to iot environments. it evaluates the performance of algorit. To address these issues, we propose a deep learning based novel method to detect cybersecurity vulnerabilities and breaches in cyber physical systems. the proposed framework contrasts the unsupervised and deep learning based discriminative approaches. Iot networks have become an increasingly valuable target of malicious attacks due to the increased amount of valuable user data they contain. in response, network intrusion detection systems have been developed to detect suspicious network activity. Ncreased vulnerability to sophisticated cyber threats. this project presents an advanced ai powered intrusion detection system (ids) tailored for iot environments, combining convolutional neural networks (cnn), long short term memory (lstm), spiking neural networks (snn), and isolati.

Pdf Threats Detection In Iot Network Iot networks have become an increasingly valuable target of malicious attacks due to the increased amount of valuable user data they contain. in response, network intrusion detection systems have been developed to detect suspicious network activity. Ncreased vulnerability to sophisticated cyber threats. this project presents an advanced ai powered intrusion detection system (ids) tailored for iot environments, combining convolutional neural networks (cnn), long short term memory (lstm), spiking neural networks (snn), and isolati.
Detection Of Real Time Malicious Intrusions And Attacks In Iot
Comments are closed.