Cyber Attack Countermeasures Edukite

Cyber Attack Countermeasures Edukite This is a course which introduces you to the basic cyber defences in context of modelling and how you can arrange quality, precision and functionality in reducing cyber attacks. you will be introduced to different mathematical techniques to handle the situation when a cyber attack takes place. D3fend is a knowledge base of cybersecurity countermeasure techniques. in the simplest sense, it is a catalog of defensive cybersecurity techniques and their relationships to offensive adversary techniques. the primary goal of the initial d3fend release is to help standardize the vocabulary used to describe defensive cybersecurity technology functionality.

Cyber Attack Countermeasures Datafloq News This course introduces the basics of cyber defense starting with foundational models such as bell lapadula and information flow frameworks. these underlying policy enforcements mechanisms help introduce basic functional protections, starting with authentication methods. To introduce you to the applications of these defence mechanisms against cyber attacks in practical life. to change your thinking about technology and security and how you look at any technological device. this course does not involve any written exams. The present article aims to get an overview of the cyber crime as it is defined and revealed by specialized literature, international legislation and historical facts, and perform an analysis of attacks reported all around the world over the last three years in order to determine patterns and trends in cyber crime. However, cybersecurity is not simply a technical issue. consider the threat of disinformation and countermeasures to it. the internet and other cybertechnologies are embedded in institutions. this is obvious in the case of internet governance bodies such as icann.
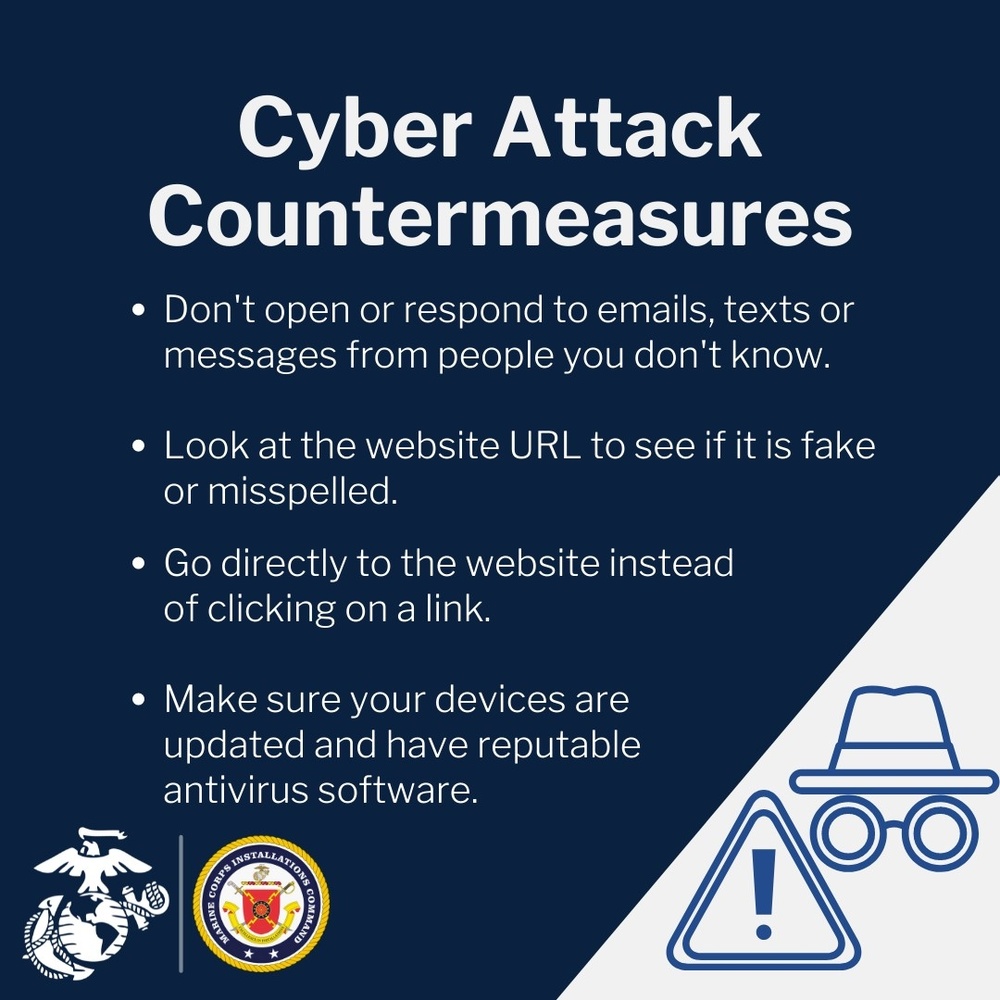
Dvids Graphics The present article aims to get an overview of the cyber crime as it is defined and revealed by specialized literature, international legislation and historical facts, and perform an analysis of attacks reported all around the world over the last three years in order to determine patterns and trends in cyber crime. However, cybersecurity is not simply a technical issue. consider the threat of disinformation and countermeasures to it. the internet and other cybertechnologies are embedded in institutions. this is obvious in the case of internet governance bodies such as icann. This course introduces the basics of cyber defense starting with foundational models such as bell lapadula and information flow frameworks. these underlying policy enforcements mechanisms help introduce basic functional protections, starting with authentication methods. Issue guidelines, advisories, vulnerability notes and whitepapers relating to information security practices, procedures, prevention, response and reporting of cyber incidents. This workshop focuses on the simulation of cyber attack and defense strategies using the cyber kill chain framework. students engage in role playing as red and blue teams to identify vulnerabilities, classify assets, and develop countermeasures against cyber threats, enhancing their understanding of cybersecurity principles and practices. This course introduces the basics of cyber defense starting with foundational models such as bell lapadula and information flow frameworks. these underlying policy enforcements mechanisms help introduce basic functional protections, starting with authentication methods. learners will be introduced to a series of different authentication solutions and protocols, including rsa secureid and.
Comments are closed.