Custom Java Deserialization Exploit Serial Snyker

Free Video Custom Java Deserialization Exploit Serial Snyker From Resolving could not get a user id. account functions will be unavailable. try again in a bit. Java deserialization vulnerabilities remain a critical security threat, with existing detection tools facing significant challenges in generating functional exploit payloads due to semantic blindness and constraint complexity. this paper presents llm jdfuzz, the framework that leverages large language models for automated java deserialization payload generation. by reframing payload generation.
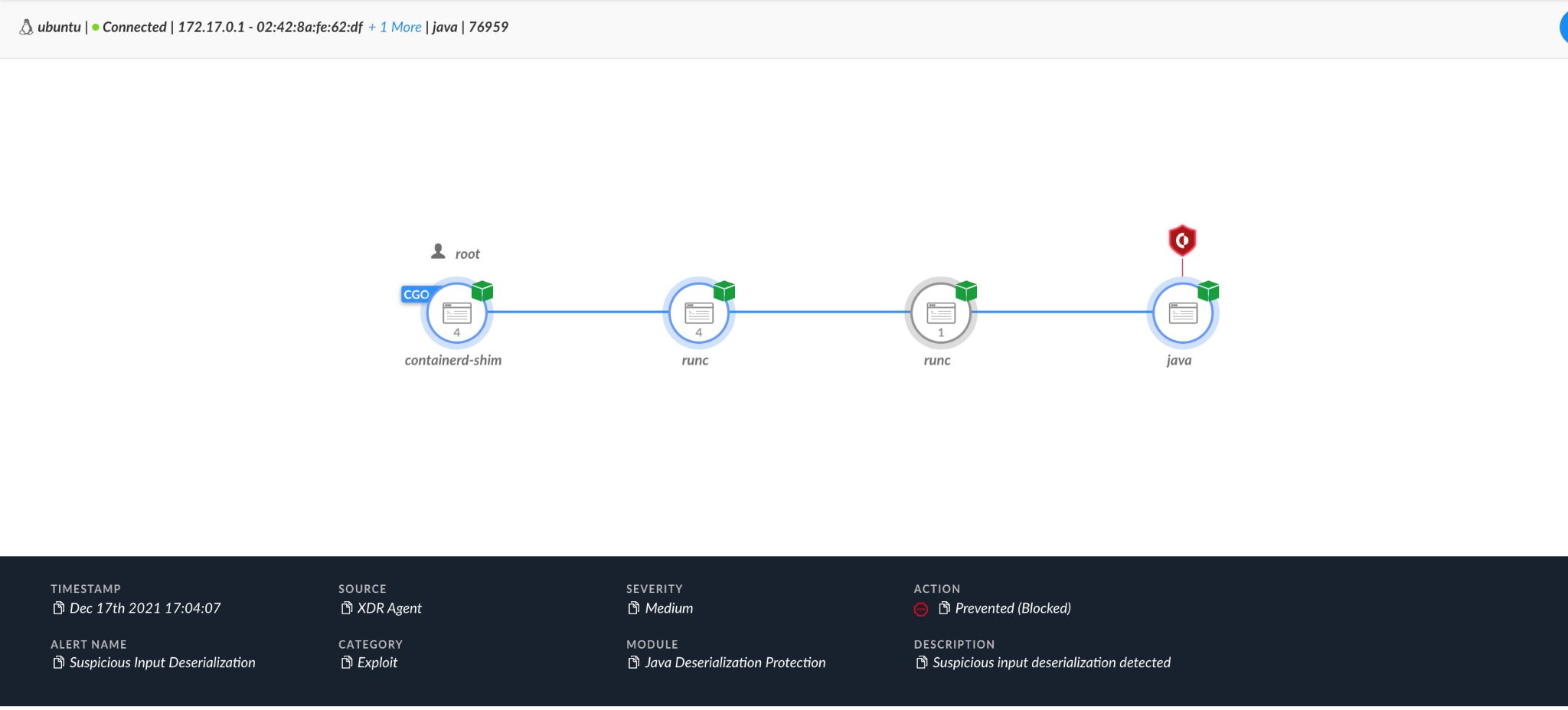
How Cortex Xdr Blocks Log4shell Exploits With Java Deserialization This exploit was mitigated in java 1.7.0 03 by having the object of type atomicreferencearray<> validate its array upon deserialization. the readobject () method inspects the array contents, and if the array is of the wrong type, it makes a defensive copy of the array, foiling the exploit. Opentelemetry java instrumentation provides opentelemetry auto instrumentation and instrumentation libraries for java. in versions prior to 2.26.1, the rmi instrumentation registered a custom endpoint that deserialized incoming data without applying serialization filters. on jdk version 16 and earlier, an attacker with network access to a jmx or rmi port on an instrumented jvm could exploit. Custom java deserialization exploit serial snyker john hammond 2.12m subscribers subscribed. Explore a comprehensive tutorial on exploiting java deserialization vulnerabilities in the "serial snyker" challenge from snyk fetch the flag. learn to analyze source code, use snyk for vulnerability detection, create custom exploits, achieve remote code execution, and build reverse shell scripts.
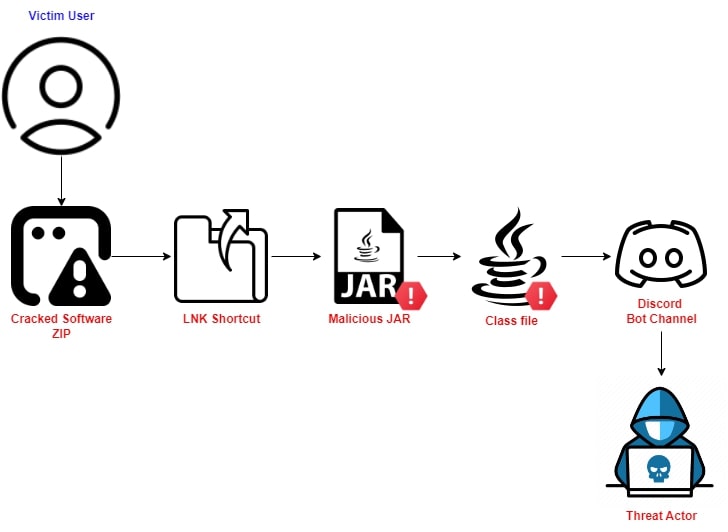
Java Based Sophisticated Stealer Using Discord Bot As Eventlistener Custom java deserialization exploit serial snyker john hammond 2.12m subscribers subscribed. Explore a comprehensive tutorial on exploiting java deserialization vulnerabilities in the "serial snyker" challenge from snyk fetch the flag. learn to analyze source code, use snyk for vulnerability detection, create custom exploits, achieve remote code execution, and build reverse shell scripts. In this article, we’ve covered how an attacker may use deserialization to exploit a vulnerable system. in addition, we have covered some practices to maintain good security hygiene in a java system. 14k views | 9 months ago custom java deserialization exploit serial snyker duration: 3:39 27.6k views | nov 15, 2022 serialization in c duration: 38:47 3.7k views | dec 9, 2021 attacking net deserialization alvaro muñoz duration: 4:08 17.1k views | apr 28, 2018 pharmaceutical serialization with deacom erp duration: 19:07 4.7k views | nov 18, 2016. Ysoserial the "ysoserial" project is a collection of publicly known gadgets and gadget chains. it further contains exploits and bypasses for early filter implementations. github frohoff ys oserial. Showcasing some custom java deserialization attack for the recent "fetch the flag" competition, building up our own serialized payload and firing it off to catch a reverse shell and.
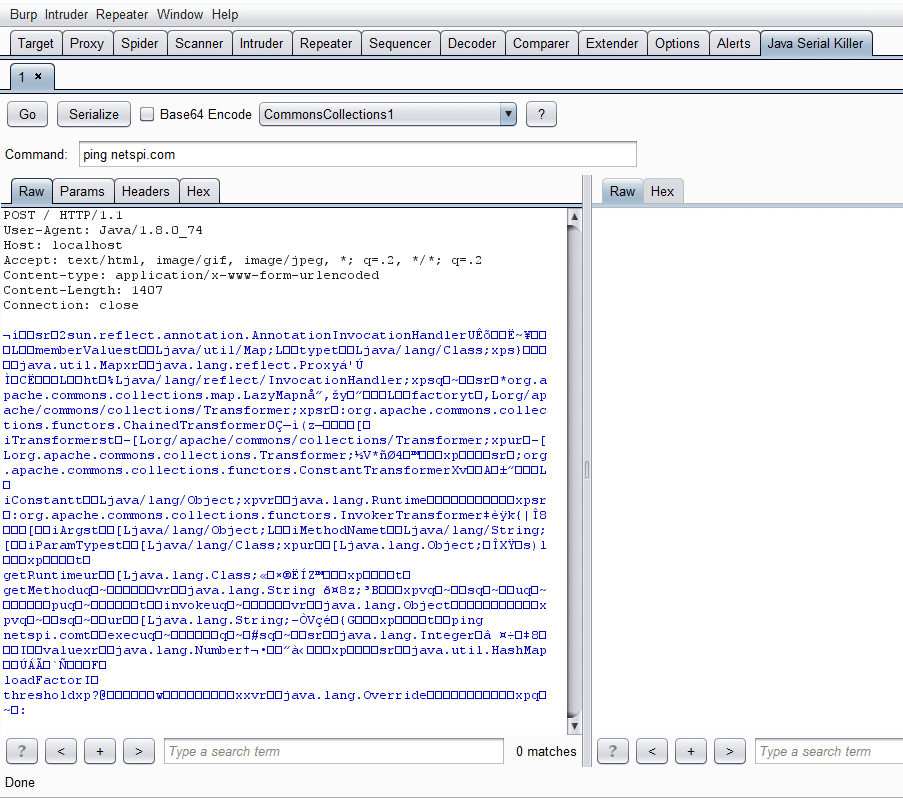
Java Deserialization Attacks With Burp In this article, we’ve covered how an attacker may use deserialization to exploit a vulnerable system. in addition, we have covered some practices to maintain good security hygiene in a java system. 14k views | 9 months ago custom java deserialization exploit serial snyker duration: 3:39 27.6k views | nov 15, 2022 serialization in c duration: 38:47 3.7k views | dec 9, 2021 attacking net deserialization alvaro muñoz duration: 4:08 17.1k views | apr 28, 2018 pharmaceutical serialization with deacom erp duration: 19:07 4.7k views | nov 18, 2016. Ysoserial the "ysoserial" project is a collection of publicly known gadgets and gadget chains. it further contains exploits and bypasses for early filter implementations. github frohoff ys oserial. Showcasing some custom java deserialization attack for the recent "fetch the flag" competition, building up our own serialized payload and firing it off to catch a reverse shell and.
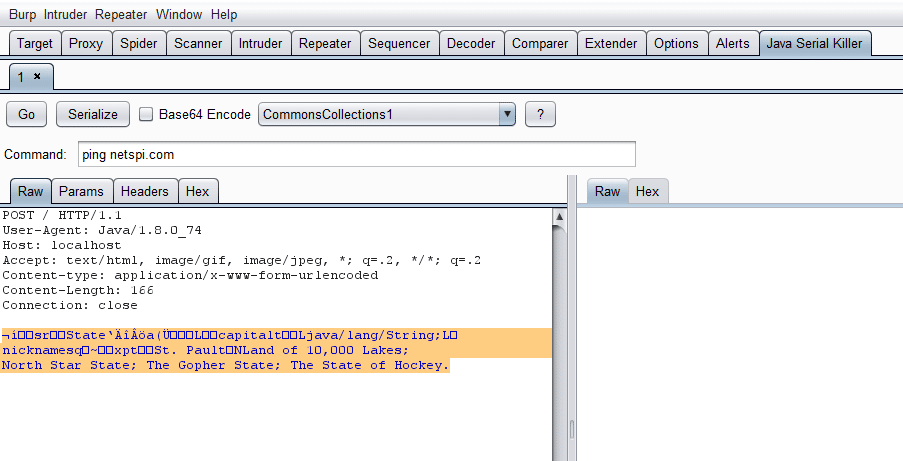
Java Deserialization Attacks With Burp Ysoserial the "ysoserial" project is a collection of publicly known gadgets and gadget chains. it further contains exploits and bypasses for early filter implementations. github frohoff ys oserial. Showcasing some custom java deserialization attack for the recent "fetch the flag" competition, building up our own serialized payload and firing it off to catch a reverse shell and.
Comments are closed.