Cryptography Simplified Asymmetric Encryption Ppt
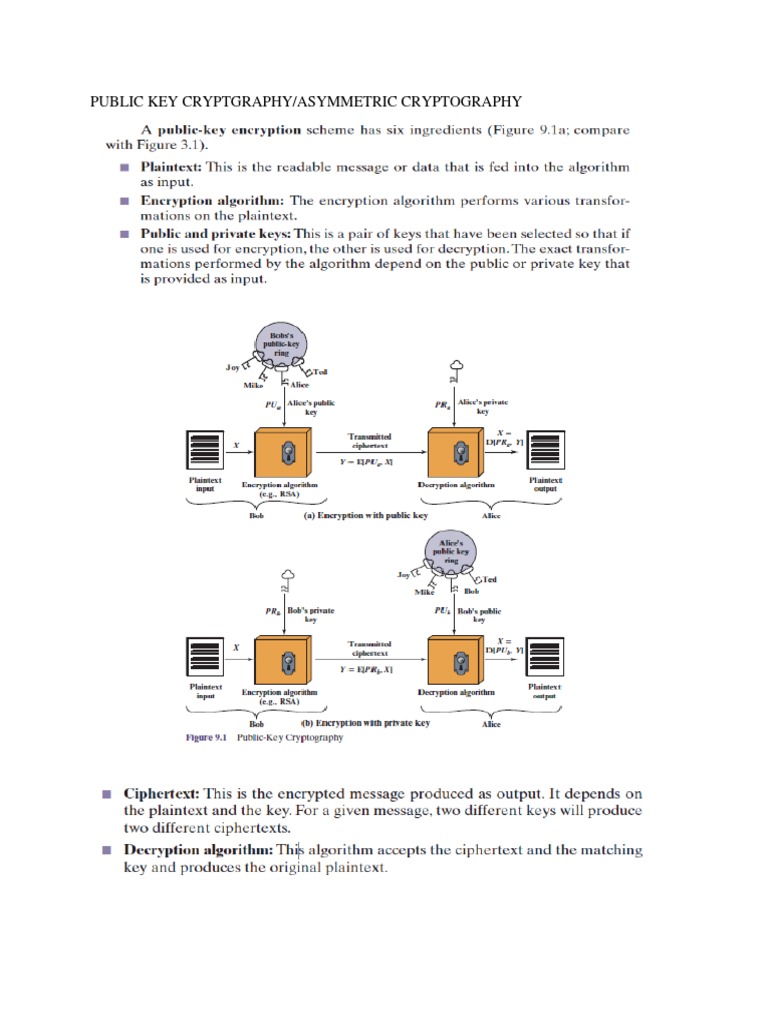
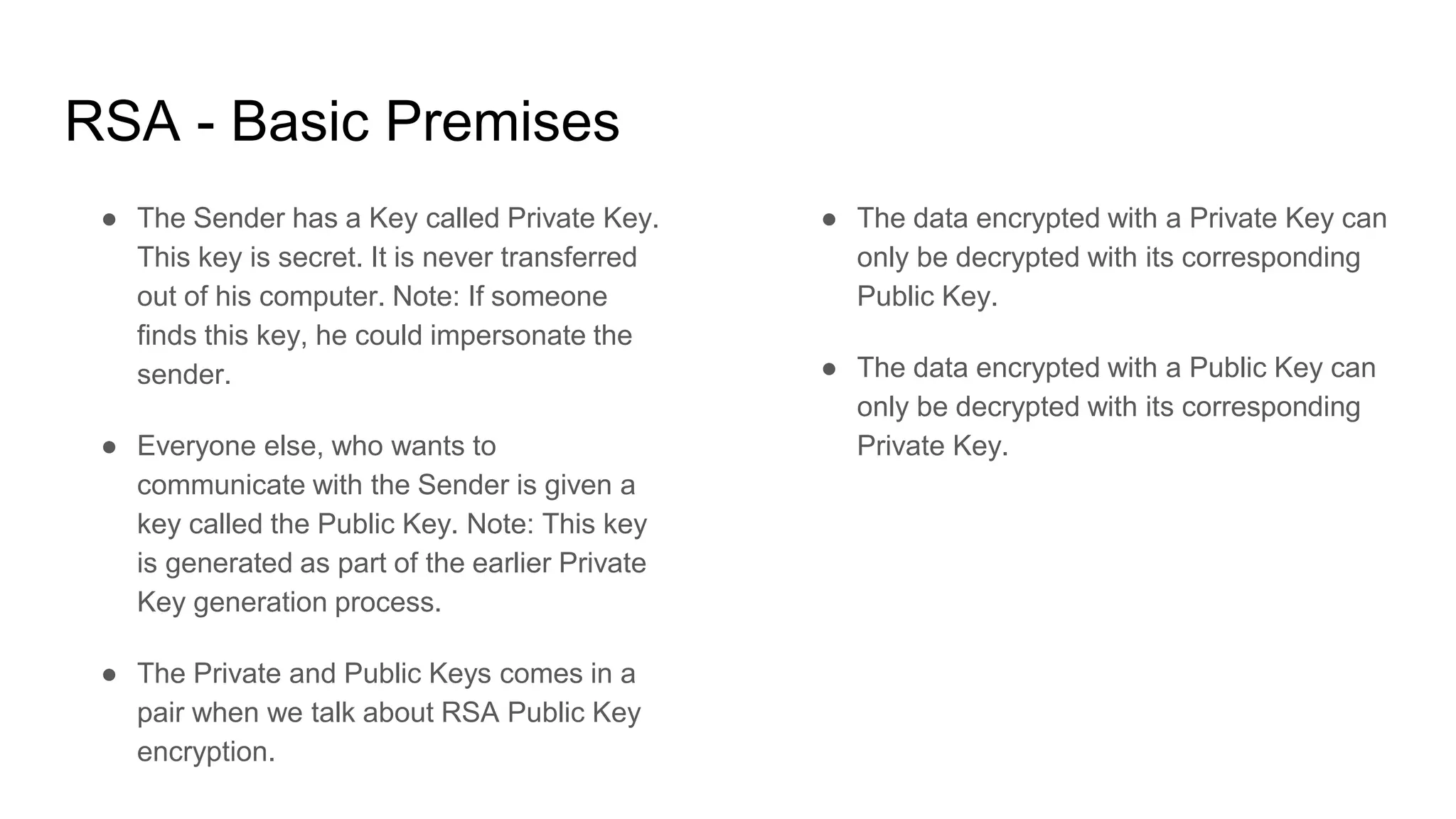
Asymmetric Cryptography Notes Pdf Pdf Public Key Cryptography The document provides an overview of asymmetric encryption, highlighting key algorithms such as rsa, diffie hellman, and elliptic curve cryptography. it explains how rsa employs a pair of keys (private and public) for secure communication, ensuring integrity, confidentiality, and non repudiation. Note 30.* 30 3 asymmetric key cryptography an asymmetric key (or public key) cipher uses two keys: one private and one public. we discuss two algorithms: rsa and diffie hellman.
Cryptography Simplified Asymmetric Encryption Ppt 1. random secret key (“session key”; discard when done) 2. encrypt message w session key & symmetric alg. encrypt session key w recipient’s public key (==> “digital envelope”) send encrypted message digital envelope. Asymmetric key cryptography free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. cryptography and system security ppt. Dive deep into classical encryption techniques, block ciphers, advanced encryption standards, rsa, diffie hellman, and elliptic curve cryptography. understand plaintext, ciphertext, encryption, and decryption methods. Explore our comprehensive powerpoint presentation on symmetric and asymmetric key cryptography. fully editable and customizable, it offers in depth insights into encryption methods and their applications. perfect for educational and professional use.
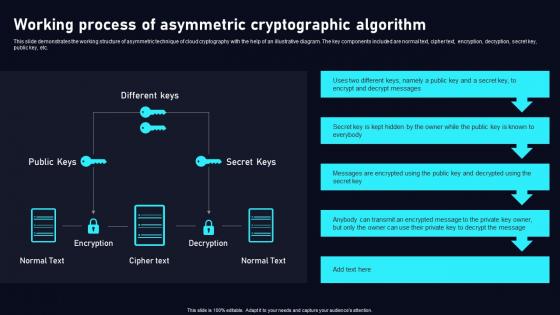
Asymmetric Cryptography Powerpoint Templates Slides And Graphics Dive deep into classical encryption techniques, block ciphers, advanced encryption standards, rsa, diffie hellman, and elliptic curve cryptography. understand plaintext, ciphertext, encryption, and decryption methods. Explore our comprehensive powerpoint presentation on symmetric and asymmetric key cryptography. fully editable and customizable, it offers in depth insights into encryption methods and their applications. perfect for educational and professional use. Download our asymmetric encryption presentation template for ms powerpoint and google slides to highlight the types, applications, pros, and cons of this cryptographic technique. This document discusses asymmetric key cryptography and the rsa cryptosystem. it begins by distinguishing between symmetric and asymmetric key cryptography, noting they serve complementary roles. it then covers the basics of public key cryptography using two keys: a private key and public key. Substitution ciphers a cipher that substitutes one character with another. these can be as simple as swapping a list, or can be based on more complex rules. these are not secure anymore, but they used to be quite common. what has changed?. Asymmetric key cryptography free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. this document summarizes asymmetric key cryptography and the rsa cryptosystem.
Comments are closed.