Cryptography Exercises Docx Official Open Cryptography Exercises 1

Open Cryptography Exercises For Chapters 1 Through 6 Pdf Do you have a good activity 6* study unit 1. explore how the one time pad (vernam cipher) works. you can watch the video given below or check it out in the internet. determine the ciphertext for the plaintext message 'saddam found' and the one time pad key as ejcitfohadl. Instructions for three cryptography labs using sagemath and python. solutions to the exercises. contribute to cryptobook exercises solutions labs development by creating an account on github.
Cryptography Lab Lab1 Docx At Master Yuzhang Cryptography Github In a nutshell: each letter of the keyword relations picks out 1 of the 26 possible substitution alphabets given in the vigen`ere tableau. thus, any message encrypted by a vigen`ere cipher is a collection of as many simple substitution ciphers as there are letters in the keyword. 1) what are the requirements with respect to the nonce initialisation vector then using cbc mode (and why)? try to thing in attacks: imagine possible attacks, if the required iv properties are not fullfilled. Exercise 12: your opponent has invented a new stream cipher mode of operation for 128 bit key aes. he thinks that ofb could be improved by feeding back into the key port rather than the data port of the aes chip. Whether you're a student pulling an all nighter before a cryptography exam, a developer adding security features to an app, or simply someone who loves puzzles, these hands on exercises will build your confidence one successful decryption at a time.

Exercises Meeting 9 14 Pdf Cryptography Encryption Exercise 12: your opponent has invented a new stream cipher mode of operation for 128 bit key aes. he thinks that ofb could be improved by feeding back into the key port rather than the data port of the aes chip. Whether you're a student pulling an all nighter before a cryptography exam, a developer adding security features to an app, or simply someone who loves puzzles, these hands on exercises will build your confidence one successful decryption at a time. Exercise 1.3 design a perfectly secure encryption scheme diferent from the otp such that m = k = c = {0, 1}n. This page includes material from many of the exercises in the book. it is designed to save you time and potential errors, since you can cut and paste material, rather than having to retype it. The enisa cybersecurity exercise methodology aims to empower and guide organisations in developing effective cybersecurity exercises from start to finish. Cryptography exercises free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses various cryptography exercises involving different ciphers and cryptanalysis techniques.
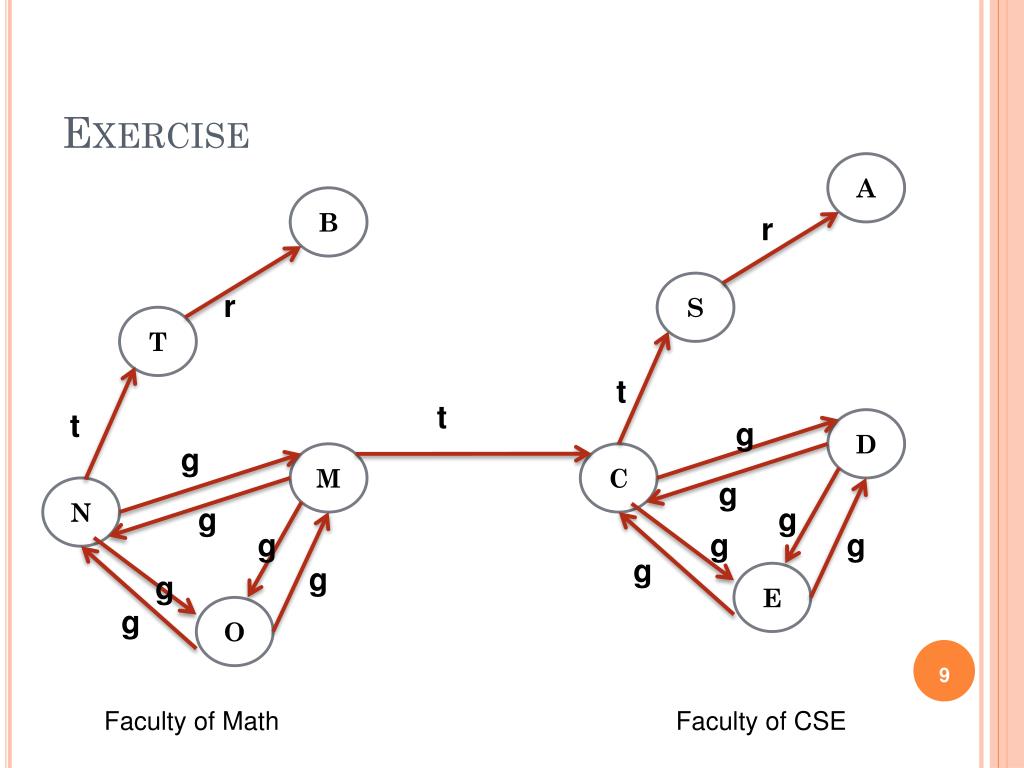
Ppt Exercises Basic Cryptography Key Exchange Protocols Powerpoint Exercise 1.3 design a perfectly secure encryption scheme diferent from the otp such that m = k = c = {0, 1}n. This page includes material from many of the exercises in the book. it is designed to save you time and potential errors, since you can cut and paste material, rather than having to retype it. The enisa cybersecurity exercise methodology aims to empower and guide organisations in developing effective cybersecurity exercises from start to finish. Cryptography exercises free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses various cryptography exercises involving different ciphers and cryptanalysis techniques.
Cryptography Exercises The enisa cybersecurity exercise methodology aims to empower and guide organisations in developing effective cybersecurity exercises from start to finish. Cryptography exercises free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses various cryptography exercises involving different ciphers and cryptanalysis techniques.
Comments are closed.