Cryptography Assignment Pdf Cipher Cryptography

Cryptography Assignment Pdf Key Cryptography Cryptography This document contains 5 sets of cryptography assignment questions for students. set 1 contains questions about fermat's theorem, modular arithmetic, solving simultaneous equations, symmetric vs asymmetric encryption, block cipher design principles, and caesar and cipher feedback ciphers. Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k.
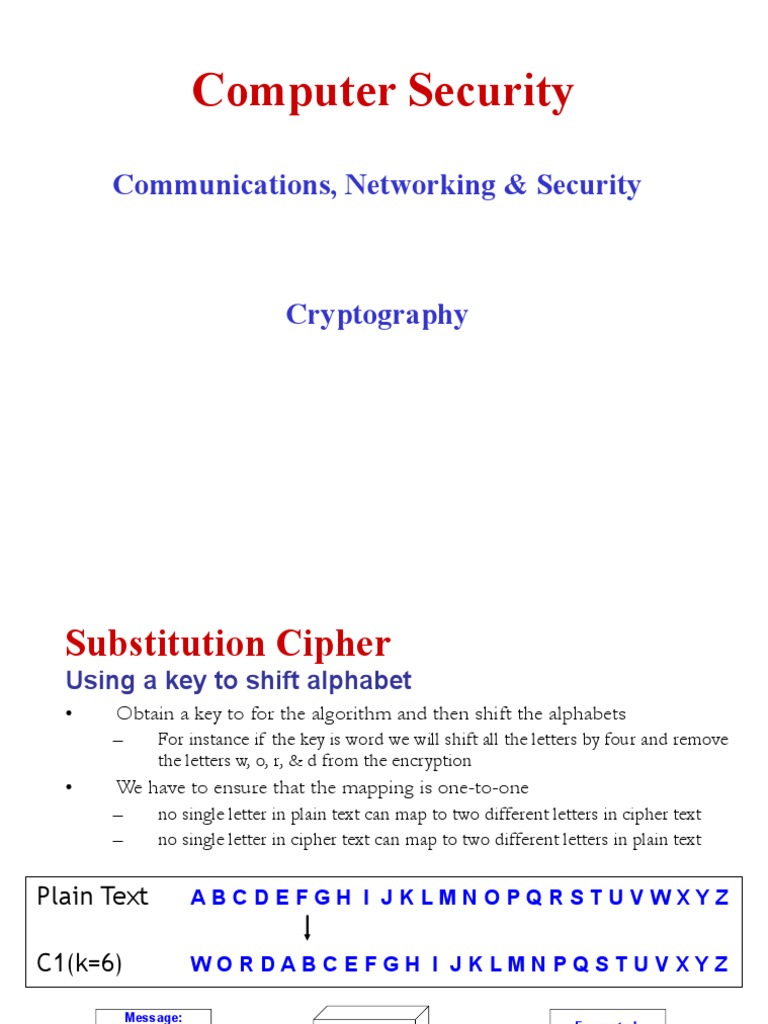
Cryptography 2 Pdf Cryptography Cipher Cipher (cryptographic algorithm): one to one correspondence between symbols of original message (plaintext p) and symbols of its equivalent in secret writing (ciphertext c). Exercise 12: your opponent has invented a new stream cipher mode of operation for 128 bit key aes. he thinks that ofb could be improved by feeding back into the key port rather than the data port of the aes chip. Digital signatures can use public key cryptography for digital signatures if alice encrypts a message with her private key. The caesar cipher we’ll start by using historical, pen and paper ciphers on ordinary letters—it’s easier to see what’s happening, and the principles are the same.

Assignment 1 Pdf Cryptography Cipher Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme. Assignment# 3 name: hafiz haseeb ur rehman course: ct 575 cryptography instructor: dr. mubashir khan frequency analysis is simply the ratio of the occurrence of any given letter in the ciphertext . its founded on the idea that, in any specific language (such as english or german etc. ), certain letters or combinations of letters occur more frequently than others . the mechanism (“how. In today's lecture, we will explore how cryptography motivates solutions to the security concerns we discussed in monday's lecture. to do so, we will discuss: cryptography is the study of secure communication techniques in the presence of an adversary. others from understanding that same message. This document is a worksheet for a cryptography and network security course. it contains definitions of key terms like cryptography, encryption, decryption, and types of attacks.

Assignment Cns Pdf Cipher Key Cryptography In today's lecture, we will explore how cryptography motivates solutions to the security concerns we discussed in monday's lecture. to do so, we will discuss: cryptography is the study of secure communication techniques in the presence of an adversary. others from understanding that same message. This document is a worksheet for a cryptography and network security course. it contains definitions of key terms like cryptography, encryption, decryption, and types of attacks.
Comments are closed.