Cryptography 4 Exercises Computer Science Docsity

Cryptography 4 Exercises Computer Science Docsity Cryptography 4, exercises computer science, exercises for cryptography and system security. Cryptography exercises free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses various cryptography exercises involving different ciphers and cryptanalysis techniques.

Practice Activity Cryptography Pdf Exercise 17: your colleagues urgently need a collision resistant hash function. their code contains already an existing implementation of ecbc mac, using a block cipher with 256 bit block size. The gronsfeld cipher is a modern variant of the vigen`ere cipher in which a key number is used instead of a keyword, e.g. 14965. other ciphers in the next exercises and in the bibliography, including the polybius cipher, the playfair cipher, the adfgvx cipher, and the enigma machine. The above figure depicts the general operation of a cryptographic hash function. typically, the input is padded out to an integer multiple of some fixed length (e., 1024 bits), and the padding includes the value of the length of the original message in bits. 4. what are the different between ssl version 3 and tls? the major version is 3 and the minor major version is 3. version s 1. * ssl use hmac alg., except that the padding bytes concatenation. tls makes use of the same alg. * ssl supports 12 various alert codes. * tls supports all of al rt codes defined in ssl3 with the exception of.
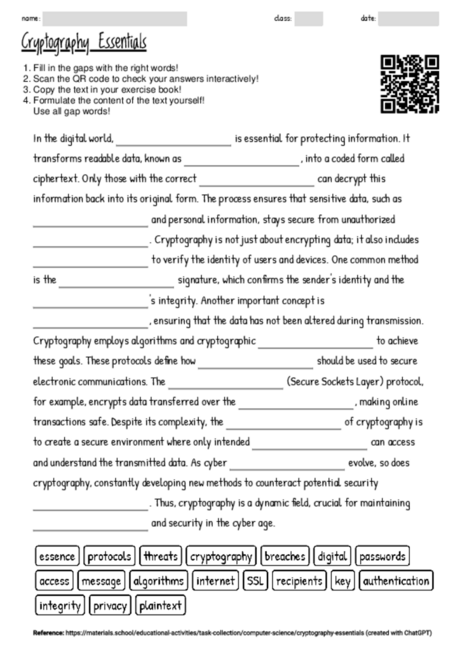
Worksheet With The Topic Cryptography Essentials Materials School The above figure depicts the general operation of a cryptographic hash function. typically, the input is padded out to an integer multiple of some fixed length (e., 1024 bits), and the padding includes the value of the length of the original message in bits. 4. what are the different between ssl version 3 and tls? the major version is 3 and the minor major version is 3. version s 1. * ssl use hmac alg., except that the padding bytes concatenation. tls makes use of the same alg. * ssl supports 12 various alert codes. * tls supports all of al rt codes defined in ssl3 with the exception of. By nadia karichev cryptography is the practice of techniques for secure communication in the presence of third par ties. encryption is the process of hidi. g or transforming data into a secretive data only the party that knows the key is. Looking for exercises in cryptography and system security? download now thousands of exercises in cryptography and system security on docsity. Looking for assignments in cryptography and system security? download now thousands of assignments in cryptography and system security on docsity. Looking for papers in cryptography and system security? download now thousands of papers in cryptography and system security on docsity.

Cryptography Assignment Pdf By nadia karichev cryptography is the practice of techniques for secure communication in the presence of third par ties. encryption is the process of hidi. g or transforming data into a secretive data only the party that knows the key is. Looking for exercises in cryptography and system security? download now thousands of exercises in cryptography and system security on docsity. Looking for assignments in cryptography and system security? download now thousands of assignments in cryptography and system security on docsity. Looking for papers in cryptography and system security? download now thousands of papers in cryptography and system security on docsity.
Comments are closed.