Cryptography 2 1 Pdf
Cryptography 2 Pdf Cryptography Cipher I wrote applied cryptography to be both a lively introduction to the field of cryptography and a comprehensive reference. i have tried to keep the text readable without sacrificing accuracy. It presents in a coherent manner most of the important cryptographic tools one needs to implement secure cryptographic systems, and explains many of the cryptographic principles and protocols of existing systems.
Cryptography 2 Pdf Cryptography Cipher Loading…. Online cryptography course preview: this page contains all the lectures in the free cryptography course. to officially take the course, including homeworks, projects, and final exam, please visit the course page at coursera. Pdf | it introduces an introduction to cryptography. | find, read and cite all the research you need on researchgate. While cryptography is the science of securing data, cryptanalysis is the science of analyzing and breaking secure communication. classical cryptanalysis involves an interesting combination of analytical reasoning, application of mathematical tools, pattern finding, patience, determination, and luck.

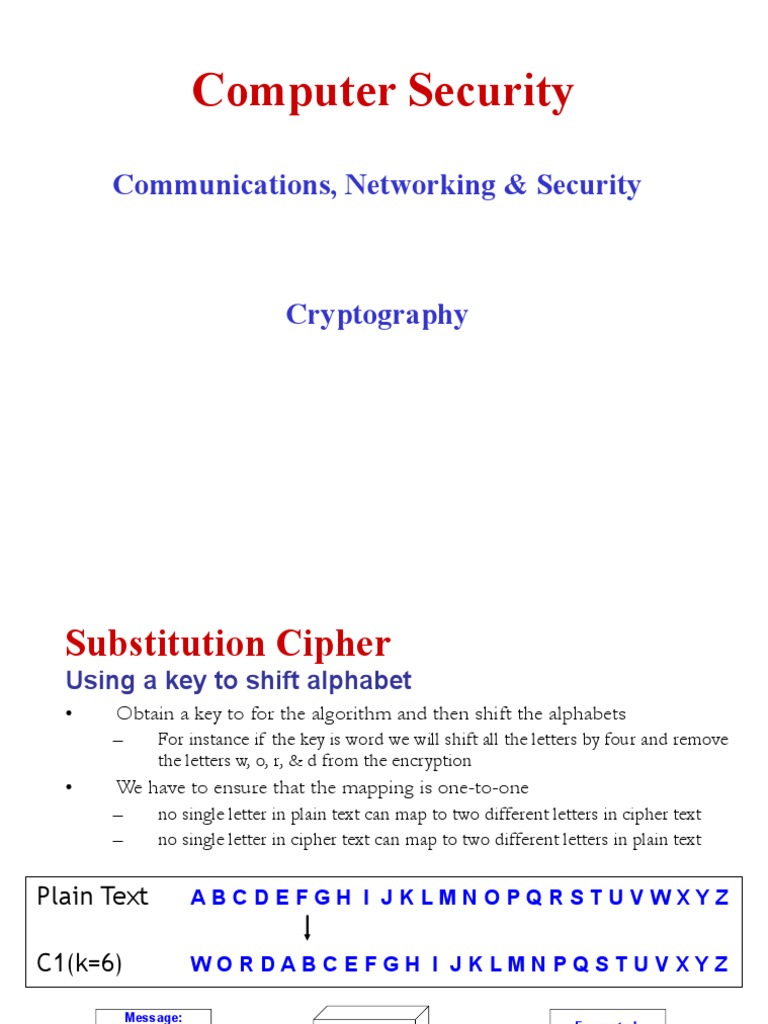
Cryptography Pdf Cryptography Key Cryptography Pdf | it introduces an introduction to cryptography. | find, read and cite all the research you need on researchgate. While cryptography is the science of securing data, cryptanalysis is the science of analyzing and breaking secure communication. classical cryptanalysis involves an interesting combination of analytical reasoning, application of mathematical tools, pattern finding, patience, determination, and luck. Lecture 2. cryptography (1) free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses cryptography and its importance for security. it defines cryptography, encryption, decryption and common cryptographic techniques like symmetric and asymmetric encryption. In this lab you will learn how to use gpg (gnu privacy guard), the open source version of pgp (pretty good privacy), to experiment with symmetric key encryption decryption. symmetric key ciphers are also called secret key ciphers. they are much more efficient than public key ciphers described next. “cryptography lies at the heart of all cybersecuriry technologies, and understanding the role it plays is vital to understanding how to secure cyberspace" (keith m. martin). Our book provides the reader with a deep understanding of how modern cryp tographic schemes work. we introduce the necessary mathematical concepts in a way that is accessible for every reader with a minimum background in college level calculus.
Comments are closed.