Cryptography 18cs744 Hill Cipher

Hill Cipher Pdf Cryptography Secrecy It includes 17 questions in module 1 on topics like symmetric ciphers, substitution techniques, stream ciphers, block ciphers, the data encryption standard (des) algorithm, and hill cipher. Explained the problem clearly.
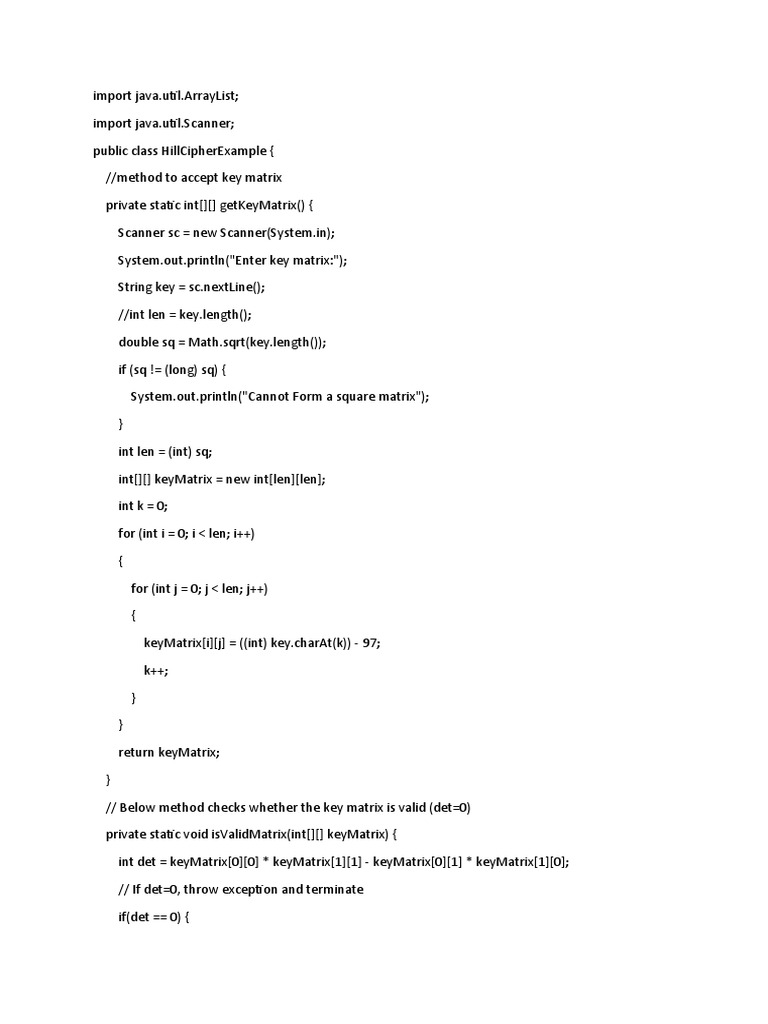
Hill Cipher Pdf Encryption Cryptography This examination paper covers various cryptographic algorithms including playfair, hill, des, rsa, and elgamal. it requires students to explain these algorithms and perform encryption and decryption tasks using specified keys and plaintexts, emphasizing practical applications in cryptography. Hill cipher is a polygraphic substitution cipher based on linear algebra. in this method, each letter of the alphabet is represented by a number modulo 26, commonly using the scheme a = 0, b = 1, …, z = 25. If intruder has an access to part of plaintext and corresponding cipher text generated using hill cipher. part plaintext is tech and corresponding cipher text is nquz. Master the hill cipher through comprehensive step by step examples that progress from simple 2x2 matrix encryption to advanced 3x3 implementations and cryptanalysis techniques. these examples provide complete calculations, demonstrating every stage of the encryption and decryption process.

Hill Cipher Pdf Cryptography Encryption If intruder has an access to part of plaintext and corresponding cipher text generated using hill cipher. part plaintext is tech and corresponding cipher text is nquz. Master the hill cipher through comprehensive step by step examples that progress from simple 2x2 matrix encryption to advanced 3x3 implementations and cryptanalysis techniques. these examples provide complete calculations, demonstrating every stage of the encryption and decryption process. This polygraphic substitution cipher allows hill cipher to function easily with digraphs (two letter blocks), trigraphs (three letter blocks), or any other multiple sized blocks to create a uniform cipher. Sch 18cs744 free download as pdf file (.pdf) or read online for free. Cbcs scheme 18cs744 seventh semester b.e. degree examination, june july 2025 cryptography max. marks: 100 note: answer any five full questions, choosing one full question from each module. The hill cipher is famous because it brings linear algebra into cryptography. instead of substituting letters one at a time, it encrypts blocks (pairs, triples, etc.), which can better obscure single letter frequencies.

Image Encryption Using Advanced Hill Cipher Algorithm Pdf Cipher This polygraphic substitution cipher allows hill cipher to function easily with digraphs (two letter blocks), trigraphs (three letter blocks), or any other multiple sized blocks to create a uniform cipher. Sch 18cs744 free download as pdf file (.pdf) or read online for free. Cbcs scheme 18cs744 seventh semester b.e. degree examination, june july 2025 cryptography max. marks: 100 note: answer any five full questions, choosing one full question from each module. The hill cipher is famous because it brings linear algebra into cryptography. instead of substituting letters one at a time, it encrypts blocks (pairs, triples, etc.), which can better obscure single letter frequencies.

Hill Cipher Pdf Cryptography Encryption Cbcs scheme 18cs744 seventh semester b.e. degree examination, june july 2025 cryptography max. marks: 100 note: answer any five full questions, choosing one full question from each module. The hill cipher is famous because it brings linear algebra into cryptography. instead of substituting letters one at a time, it encrypts blocks (pairs, triples, etc.), which can better obscure single letter frequencies.
Comments are closed.