Cryptography 101 Xor Cipher

Cr 1 2 Xor Cipher Pdf Cryptanalysis Encryption What is the xor cipher? (definition) xor encryption is a symmetrical encryption decryption method based on the use of the logical binary operator xor (also called exclusive or, symbolized by ⊕). this technique consists of combining each bit of the message with a key bit, using the xor operation. With this logic, a string of text can be encrypted by applying the bitwise xor operator to every character using a given key. to decrypt the output, merely reapplying the xor function with the key will remove the cipher.
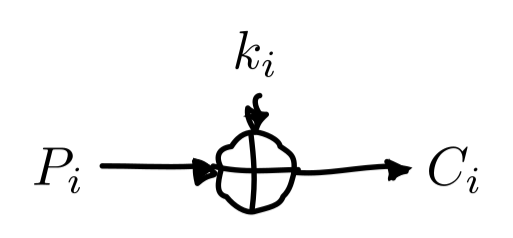
Xor Cryptography Use our online tool to encrypt or decrypt xor encryption, binary, hexadecimal or text. To understand why, we need to first introduce the and, or and xor bitwise operations. specifically why xor must be used when performing the one time pad on computers. Due to its effectiveness and simplicity, the xor encryption is an extremely common component used in more complex encryption algorithms used nowadays. the xor encryption algorithm is an example of symmetric encryption where the same key is used to both encrypt and decrypt a message. The basic idea behind xor encryption is, if you don't know the xor encryption key before decrypting the encrypted data, it is impossible to decrypt the data. for example, if you xor two unknown variables you cannot tell what the output of those variables is.
Github Maaz25925 Xor Cipher Due to its effectiveness and simplicity, the xor encryption is an extremely common component used in more complex encryption algorithms used nowadays. the xor encryption algorithm is an example of symmetric encryption where the same key is used to both encrypt and decrypt a message. The basic idea behind xor encryption is, if you don't know the xor encryption key before decrypting the encrypted data, it is impossible to decrypt the data. for example, if you xor two unknown variables you cannot tell what the output of those variables is. Description: xor is often used in generating checksums to verify data integrity. by xoring data blocks together, you can create a simple checksum that helps identify errors in transmission. Online cryptography course preview: this page contains all the lectures in the free cryptography course. to officially take the course, including homeworks, projects, and final exam, please visit the course page at coursera. The xor cipher is a simple, yet powerful cryptographic method for securing data. in its simplest form, only a secret key is necessary to perform both encryption and decryption using the bitwise exclusive or operation, often denoted with a circle plus, ⊕. Xor encryption is a type of symmetric encryption so it simplifies key management as compared to asymmetric encryption methods. it can be easily customized by using different keys, allowing for a wide range of encryption variations.
Comments are closed.