Cryptography 1 Pdf Cryptography Encryption

Module 04 Cryptography And Encryption Pdf Cryptography Public Key Our book provides the reader with a deep understanding of how modern cryp tographic schemes work. we introduce the necessary mathematical concepts in a way that is accessible for every reader with a minimum background in college level calculus. Also known as secret key cryptography or conventional cryptography, symmetric key cryptography is an encryption system in which the sender and receiver of a message share a single, common key that is used to encrypt and decrypt the message.

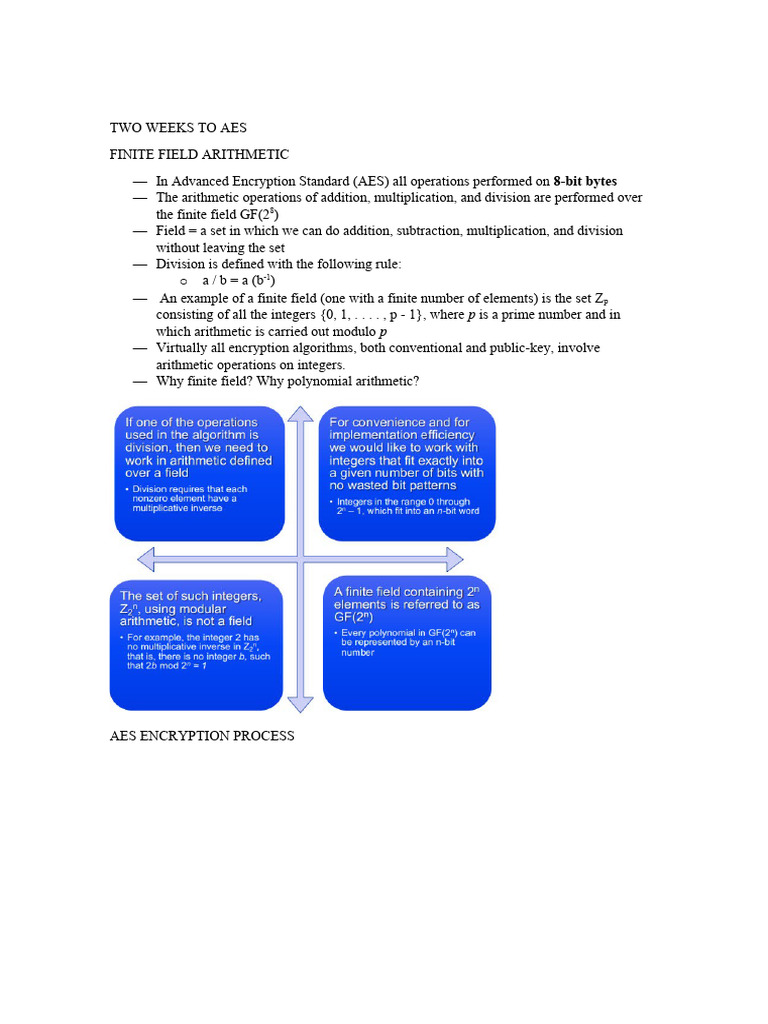
Cryptography 1 Pdf Applied Mathematics Security Engineering The national bureau of standards (nbs) (now called nist, the national institute of standards and technology) put out a call for a modern, public encryption algorithm. It introduces an introduction to cryptography. encryption key. the sender inputs the encryption key into the encryption algorithm along with the plaintext in order to compute the ciphertext. Chapter 1 of 'understanding cryptography' introduces the fundamental concepts of cryptography, including symmetric and asymmetric ciphers, and the importance of key security. Two requirements for secure use of symmetric encryption: a strong encryption algorithm a secret key known only to sender receiver y = ek(x) x = dk(y) assume encryption algorithm is known implies a secure channel to distribute key.

Lab01 Classical Cryptography Pdf Cryptography Encryption While encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that. in this class, we will learn about pseudorandom number generators, digital signatures, zero knowledge proofs, multi party computation, to name just a few examples. In computer based cryptography, it is the art of ciphering an easily understood message or “plain text” into one that cannot be easily deciphered (mel and baker 2001). the basic components for a cryptographic system are a ciphering engine, a key exchange mechanism, and a random number generator. Follows the more traditional form of cryptography with key lengths ranging from 40 to 256 bits. how do we securely distribute the shared secret key between the sender and receiver? what if you want to communicate with multiple people, and each communication needs to be confidential? how many keys do we have to manage? a key for each! key explosion!. This chapter delves into public key cryptography, focusing primarily on its use for encryption. we will explore the concept of public key cryptosystems, which involves not only encryption methods but also key generation and the associated processes for encryption and decryption.

Encryption Pdf Cryptography Encryption Follows the more traditional form of cryptography with key lengths ranging from 40 to 256 bits. how do we securely distribute the shared secret key between the sender and receiver? what if you want to communicate with multiple people, and each communication needs to be confidential? how many keys do we have to manage? a key for each! key explosion!. This chapter delves into public key cryptography, focusing primarily on its use for encryption. we will explore the concept of public key cryptosystems, which involves not only encryption methods but also key generation and the associated processes for encryption and decryption.
Chapter 3 2 Cryptography And Encryption Techniques Pdf Cryptography
Cryptography Pdf Cryptography Encryption

Cryptography Pdf Cryptography Encryption

Understanding Cryptography Pdf Cryptography Encryption

Cryptography 1 Ciphers And Fundamentals Pdf Key Cryptography

Encryption Pdf Cryptography Encryption

Encryption Pdf 2 Pdf Cryptography Key Cryptography

Cryptography Pdf Cryptography Public Key Cryptography

Cryptography V1 0 Pdf Cryptography Encryption
Classical Cryptography Pdf Cryptography Cipher

Day3 Cryptography Pdf Cryptography Encryption

19ecs305 Cryptography And Network Security Pdf Cryptography
Cryptography Pdf Cryptography Encryption
Cryptography Pdf Cryptography Encryption

Cryptography New Pdf Cryptography Encryption
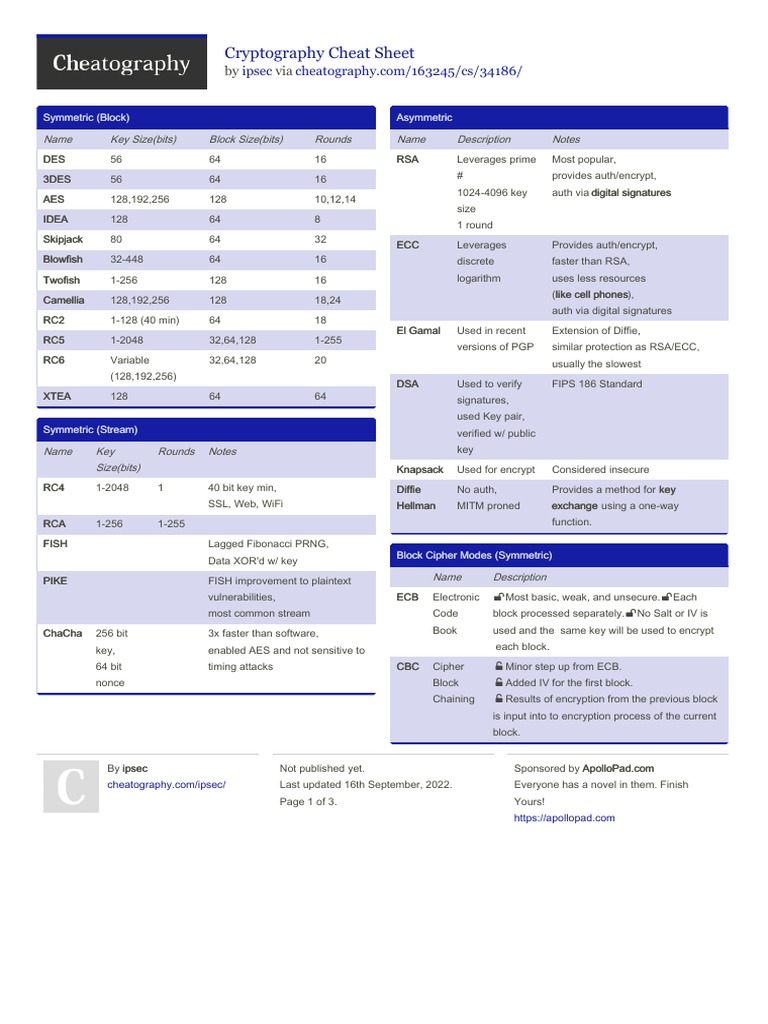
Cryptography Cheat Sheet Pdf Cipher Encryption
Modern Cryptography Primer Book Pdf Cryptography Encryption

Cryptography 1 Pdf Cryptography Encryption

Cryptography 201 Pdf Cryptography Encryption

Modern Cryptography Pdf Cryptography Encryption

Basics Of Cryptography Pdf Cryptography Encryption

Encryption Pdf Cryptography Encryption

Cryptography Pdf Cryptography Encryption

Cryptography Pdf Cryptography Encryption
Cryptography 2 Pdf Cryptography Cipher

C1 Cryptography Overview Pdf Cryptography Encryption

Cryptography Pdf Cryptography Cipher

Cryptography Pdf Cryptography Encryption

Cryptography Module 1 Notes Pdf Cryptography Key Cryptography
Module 1 Part 3 Cryptography Pdf Cryptography Encryption
Cryptography Lecture 4 Notes Pdf Cryptography Encryption
Comments are closed.