Cryptographic Hash Functions Pdf Secrecy Security Engineering

Cryptographic Hash Functions Pdf Cryptography Security Engineering Cryptographic hash functions free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. a cryptographic hash function takes an input of arbitrary size and outputs a fixed size digest. The essence of the use of a hash function for message integrity is as follows. the sender computes a hash value as a function of the bits in the message and transmits both the hash value and the message.
Cryptographic Hash Function And Its Properties Pdf Cryptography Cryptographic hashes are also known as “cryptographic checksums” or “message digests”. In our design of hash functions (for aiding the proofs) we have assumed that the hash function is ideal. one important requirement was that the only way to learn the hash of a value is by actually computing it!. These slides are based partly on lawrie brown’s slides supplied with william stallings’s book “cryptography and network security: principles and practice,” 5th ed, 2011. Bob re computes a message hash and verifies the digest with alice’s message digest.

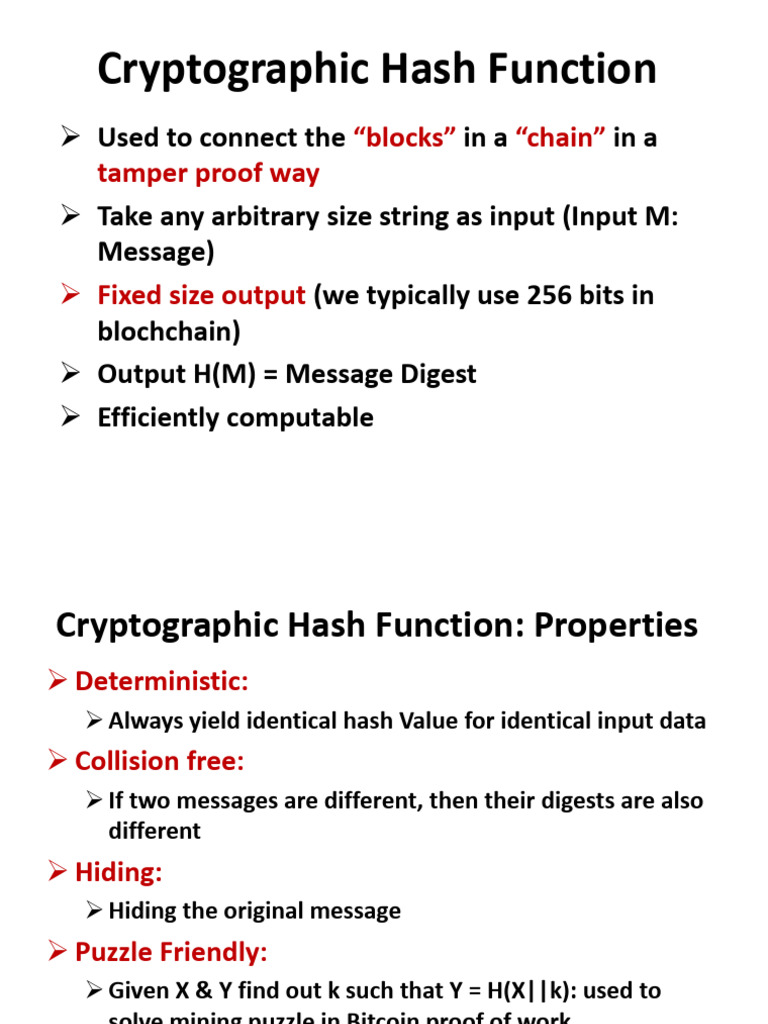
Understanding Cryptographic Hash Functions And Their Applications These slides are based partly on lawrie brown’s slides supplied with william stallings’s book “cryptography and network security: principles and practice,” 5th ed, 2011. Bob re computes a message hash and verifies the digest with alice’s message digest. The recent trend in studies in the field of artificial intelligence will encourage more researchers to focus on ai supported hash function designs. P1 and p2 could be domain names in a certificate, images, pdfs, etc. any digital image. this is one of the two ways md5 is broken (other is plain old collision resistance), and is how we generated the two images with the same md5 sum for the example from the citizen lab report. Cryptographic hash functions we expect a cryptographic hash function satisfy the following properties. Keccak uses a new “sponge construction" chaining mode, based on a fixed permutation, that can readily be adjusted to trade generic security strength for throughput, and can generate larger or smaller hash outputs as required.
Cryptographic Hash Functions The recent trend in studies in the field of artificial intelligence will encourage more researchers to focus on ai supported hash function designs. P1 and p2 could be domain names in a certificate, images, pdfs, etc. any digital image. this is one of the two ways md5 is broken (other is plain old collision resistance), and is how we generated the two images with the same md5 sum for the example from the citizen lab report. Cryptographic hash functions we expect a cryptographic hash function satisfy the following properties. Keccak uses a new “sponge construction" chaining mode, based on a fixed permutation, that can readily be adjusted to trade generic security strength for throughput, and can generate larger or smaller hash outputs as required.

Unit 4 Cryptographic Hash Functions Pdf Cryptography Encryption Cryptographic hash functions we expect a cryptographic hash function satisfy the following properties. Keccak uses a new “sponge construction" chaining mode, based on a fixed permutation, that can readily be adjusted to trade generic security strength for throughput, and can generate larger or smaller hash outputs as required.
Comments are closed.