Cryptographic Algorithms And Security Protocols Overview Course Hero

Applied Crypto Cryptographic Protocols And Key Exchange In 2023 It is also known as the "code of practice for information security management" and outlines a set of required security controls that organizations should use to protect their information assets. The course aims to provide an introduction to cryptographic techniques. the main objective is for students to learn and understand basic algorithms for symmetric and asymmetric cryptography and their mathematical principles, as well as their applications to fundamental security protocols.
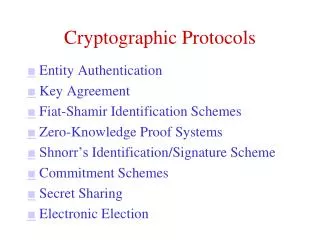
Ppt Cryptographic Algorithms Powerpoint Presentation Free Download Understanding cryptographic algorithms and protocols is essential for ensuring data security in today’s digital landscape. mastery of these concepts will equip computer science students with the knowledge needed to protect sensitive information effectively. A cryptographic algorithm is also known as an encryption algorithm. a cryptographic algorithm uses an encryption key to hide the information and convert it into an unreadable format. Discover how protocols like ssl tls, ssh, and pgp protect confidentiality, integrity, and authentication in digital transactions and interactions. explore key types of cryptographic protocols, their functions, and their importance in cybersecurity. Blockchains and cryptocurrencies utilize wealth of cryptographic protocols (implemented as open source software, written in high level programming languages, using advanced cryptography libraries, running on fast pcs servers).

Study Guide On Cryptographic Attacks And Protocols Course Hero Discover how protocols like ssl tls, ssh, and pgp protect confidentiality, integrity, and authentication in digital transactions and interactions. explore key types of cryptographic protocols, their functions, and their importance in cybersecurity. Blockchains and cryptocurrencies utilize wealth of cryptographic protocols (implemented as open source software, written in high level programming languages, using advanced cryptography libraries, running on fast pcs servers). Cryptographic protocols overview. this document provides lecture notes on cryptographic protocols. it begins with an introduction that describes terminology, prerequisites in number theory and complexity theory, and assumptions like the discrete log assumption. * gen often takes no input for a symmetric key encryption scheme, but may take as input a security parameter for a public key encryption algorithm; for example, the security parameter can be the number of bits of the modulus for rsa dec must be deterministic. This course features a rigorous introduction to modern cryptography, with an emphasis on the fundamental cryptographic primitives of public key encryption, digital signatures, pseudo random number generation, and basic protocols and their computational complexity requirements. Specify a protocol to be used by the two principals that makes use of the security algorithm and the secret information to achieve a particular security service.

Cryptography And Network Security Concepts Attacks And Models Cryptographic protocols overview. this document provides lecture notes on cryptographic protocols. it begins with an introduction that describes terminology, prerequisites in number theory and complexity theory, and assumptions like the discrete log assumption. * gen often takes no input for a symmetric key encryption scheme, but may take as input a security parameter for a public key encryption algorithm; for example, the security parameter can be the number of bits of the modulus for rsa dec must be deterministic. This course features a rigorous introduction to modern cryptography, with an emphasis on the fundamental cryptographic primitives of public key encryption, digital signatures, pseudo random number generation, and basic protocols and their computational complexity requirements. Specify a protocol to be used by the two principals that makes use of the security algorithm and the secret information to achieve a particular security service.

Understanding Cryptography Concepts Techniques And Course Hero This course features a rigorous introduction to modern cryptography, with an emphasis on the fundamental cryptographic primitives of public key encryption, digital signatures, pseudo random number generation, and basic protocols and their computational complexity requirements. Specify a protocol to be used by the two principals that makes use of the security algorithm and the secret information to achieve a particular security service.
Comments are closed.