Creating A Secure Sandbox For Untrusted Code

Code Sandbox Examples Codesandbox In this tutorial, we will be building a simple sandbox solution. note that this is not the perfect one (many companies have worked years together on security), but still it manages to give you an idea of building your own sandbox. what will be the consequences if you don't use a sandbox?. This guide will walk you through everything you need to know to securely run untrusted code using vmware or virtualbox, from understanding risks to implementing best practices for isolation, monitoring, and recovery.

Codesandbox Epictools Create a sandbox for each developer or student, and run their code in the sandbox. this way, you can run multiple development environments in parallel without them interfering with each other. Codejail manages execution of untrusted code in secure sandboxes. it is designed primarily for python execution, but can be used for other languages as well. security is enforced with apparmor. In javascript, you can create a simple sandbox environment using the with statement and new function. this method restricts the execution scope of the code, preventing it from accessing. This guide explains what a remote code execution sandbox is, how isolation models differ, what security controls are required in production, and how to evaluate platforms without oversimplifying the tradeoffs.

Unable To Create Repository From Sandbox Issue 7222 Codesandbox In javascript, you can create a simple sandbox environment using the with statement and new function. this method restricts the execution scope of the code, preventing it from accessing. This guide explains what a remote code execution sandbox is, how isolation models differ, what security controls are required in production, and how to evaluate platforms without oversimplifying the tradeoffs. Paul hammant's blog: building a secure container sandbox on chromeos for testing untrusted code. We’ll dive into the core components, walk through a step by step implementation, and discuss limitations and best practices to ensure robust isolation of untrusted code. Explore how secure sandboxes confine untrusted code with enforced access control, confidentiality, and integrity in modern computing systems. How can you view or run untrusted content using windows sandbox? first, refer to the instructions provided in our documentation to determine if your device meets the requirements and learn how to install windows sandbox.

Set Up Your First Vm Sandbox Codesandbox Paul hammant's blog: building a secure container sandbox on chromeos for testing untrusted code. We’ll dive into the core components, walk through a step by step implementation, and discuss limitations and best practices to ensure robust isolation of untrusted code. Explore how secure sandboxes confine untrusted code with enforced access control, confidentiality, and integrity in modern computing systems. How can you view or run untrusted content using windows sandbox? first, refer to the instructions provided in our documentation to determine if your device meets the requirements and learn how to install windows sandbox.
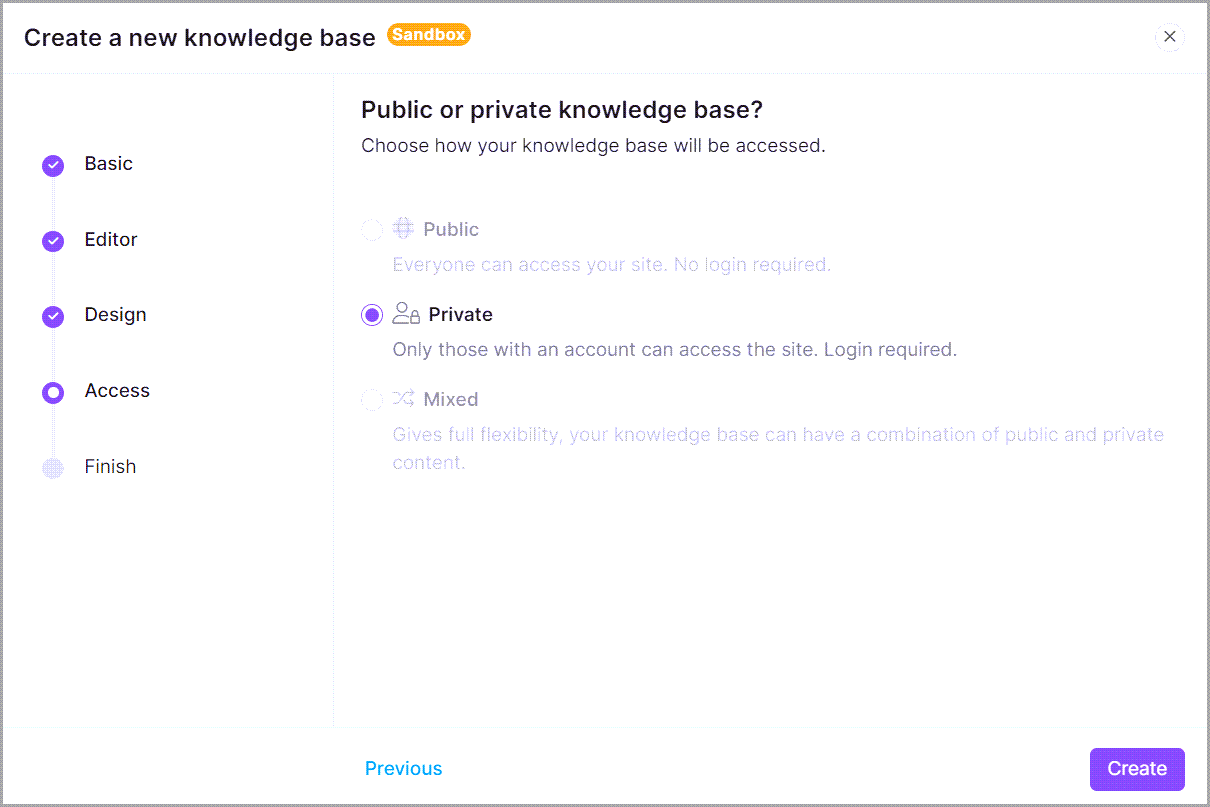
Creating A Sandbox Project Explore how secure sandboxes confine untrusted code with enforced access control, confidentiality, and integrity in modern computing systems. How can you view or run untrusted content using windows sandbox? first, refer to the instructions provided in our documentation to determine if your device meets the requirements and learn how to install windows sandbox.
Comments are closed.