Creating A Malware Analysis Environment

Malware Analysis Lab Setup Pdf Building the right malware analysis lab is the first step for every researcher. use this guide and download our free custom tools to aid your research. Verifying that you are not a robot.
Building A Malware Analysis Lab Pdf Malware Antivirus Software Ready to explore the world of cybersecurity and analyze real world exploits safely? this gold standard guide provides everything you need to build a professional grade, fully isolated malware analysis lab on your own computer using virtualbox. In this installment, i’m setting up a dedicated malware analysis lab within my home environment. this lab will feature two virtual machines (vms) specifically designed for analyzing. By setting up a controlled, isolated environment, organizations can detect and mitigate threats before they compromise critical systems. in this guide, we will walk through the process of setting up a malware sandbox for effective threat analysis. If you’re planning to dive into malware analysis, this pdf guide is an excellent starting point. “step by step malware analysis lab setup” by ammar hakim haris walks you through the entire process of building a safe and isolated analysis lab — even if it’s your first time setting one up.

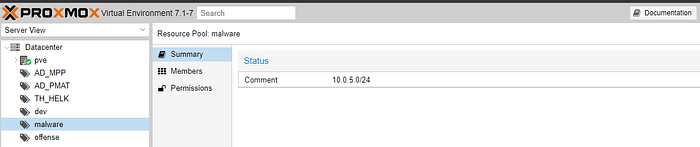
Creating A Virtualised Malware Analysis Lab Environment Kraven Security By setting up a controlled, isolated environment, organizations can detect and mitigate threats before they compromise critical systems. in this guide, we will walk through the process of setting up a malware sandbox for effective threat analysis. If you’re planning to dive into malware analysis, this pdf guide is an excellent starting point. “step by step malware analysis lab setup” by ammar hakim haris walks you through the entire process of building a safe and isolated analysis lab — even if it’s your first time setting one up. Malware labs must be separated from other networks to prevent infections from spilling outside of the lab. at a minimum, the analysis labs themselves should only be accessible one way via a specific interface. In this guide, we walked through the step by step process of setting up a malware analysis lab, from choosing a hypervisor to configuring network settings, security measures, and essential tools. In this guide, we’ll walk through the steps together, ensuring you have the right environment to analyse the malicious software. before starting, let’s take a quick look at the safe malware handling procedures. isolation: always conduct malware analysis in a controlled and isolated environment. In the following guide, we’ll look at how to build an ideal first sandbox that can help you start this career. first, you’ll need software to create virtual machines (from now on referred to as vms) and a windows iso.

Creating A Virtualised Malware Analysis Lab Environment Kraven Security Malware labs must be separated from other networks to prevent infections from spilling outside of the lab. at a minimum, the analysis labs themselves should only be accessible one way via a specific interface. In this guide, we walked through the step by step process of setting up a malware analysis lab, from choosing a hypervisor to configuring network settings, security measures, and essential tools. In this guide, we’ll walk through the steps together, ensuring you have the right environment to analyse the malicious software. before starting, let’s take a quick look at the safe malware handling procedures. isolation: always conduct malware analysis in a controlled and isolated environment. In the following guide, we’ll look at how to build an ideal first sandbox that can help you start this career. first, you’ll need software to create virtual machines (from now on referred to as vms) and a windows iso.
Creating A Virtualised Malware Analysis Lab Environment Kraven Security In this guide, we’ll walk through the steps together, ensuring you have the right environment to analyse the malicious software. before starting, let’s take a quick look at the safe malware handling procedures. isolation: always conduct malware analysis in a controlled and isolated environment. In the following guide, we’ll look at how to build an ideal first sandbox that can help you start this career. first, you’ll need software to create virtual machines (from now on referred to as vms) and a windows iso.

Creating A Virtualised Malware Analysis Lab Environment Kraven Security
Comments are closed.