Create A Workspace Aqua Security Workshop
Create A Workspace Aqua Security Workshop The cloud9 workspace should be built by an iam user with administrator privileges, not the root account user. please ensure you are logged in as an iam user, not the root account user. To start the workshop, follow one of the following depending on whether you are… once you have completed with either setup, continue with create a workspace.
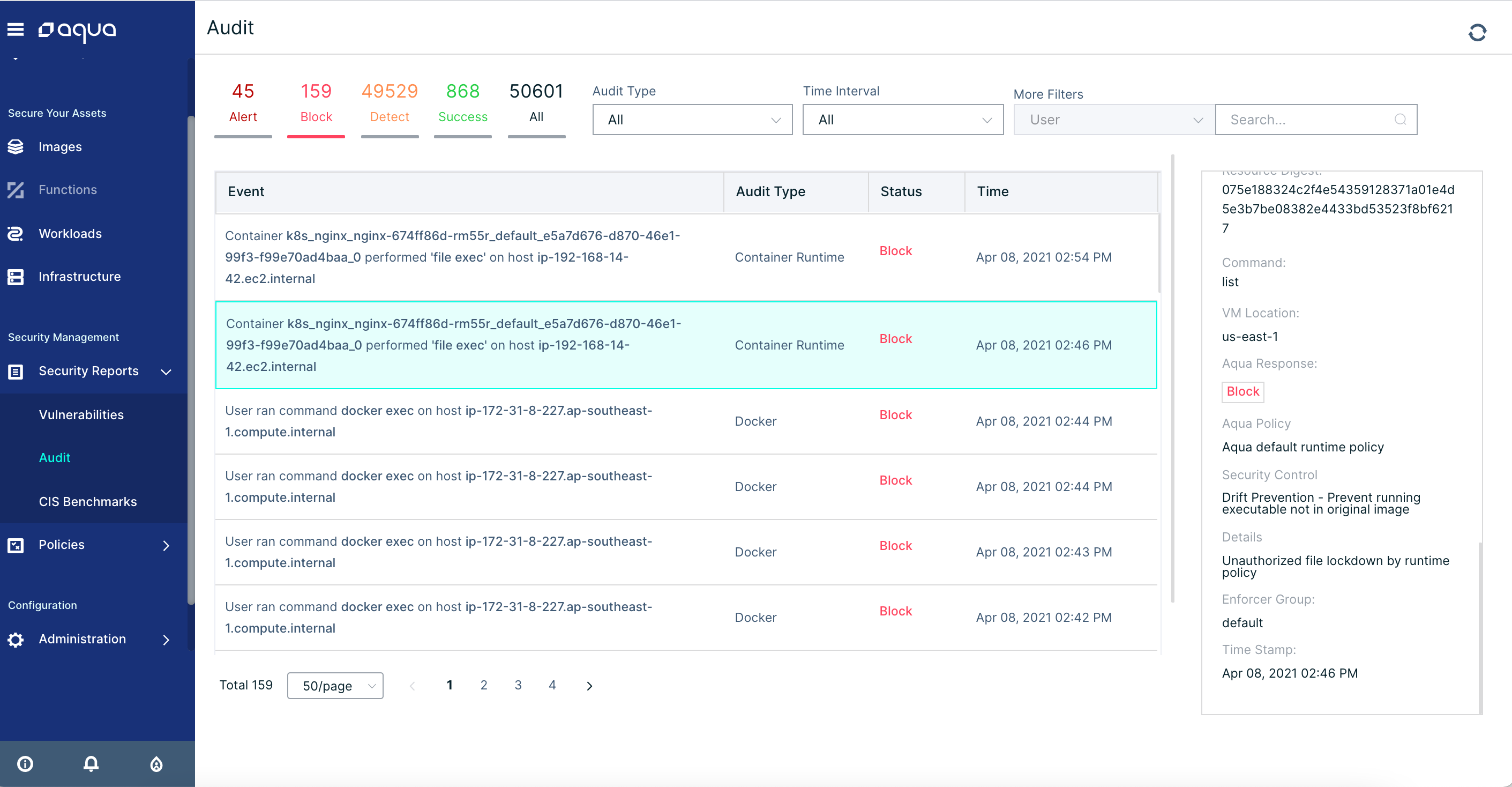
Forensics Aqua Security Workshop Choose “t3.small” for instance type, take all default values and click create environment when it comes up, customize the environment by closing the welcome tab and opening a new terminal tab in the main work area. Running the workshop on your own create a workspace install kubernetes tools create an iam role for your workspace attach the iam role to your workspace update iam settings for your workspace. From quick, practical courses to comprehensive and in depth explorations of our features, learn everything you need to know about the aqua platform to secure your cloud native tools. Discover how to expand customers’ security expertise to better defend against today’s increasingly complex and sophisticated attacks with free virtual microsoft security immersion workshops.
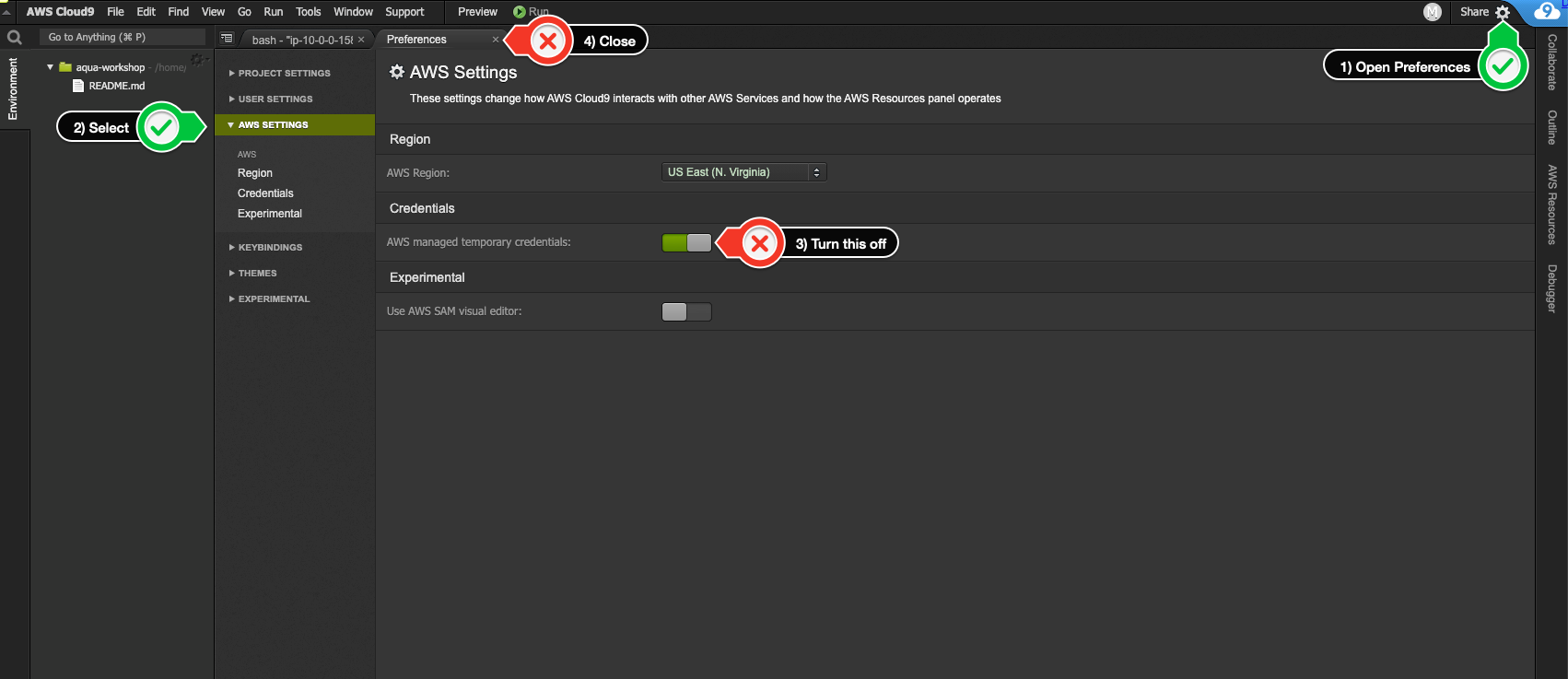
Update Iam Settings For Your Workspace Aqua Security Workshop From quick, practical courses to comprehensive and in depth explorations of our features, learn everything you need to know about the aqua platform to secure your cloud native tools. Discover how to expand customers’ security expertise to better defend against today’s increasingly complex and sophisticated attacks with free virtual microsoft security immersion workshops. Whatever your budget or need, we make finding the perfect workspace easy. from flexible memberships to move in ready offices, we give you the space and solutions to do your best work. By simulating real world cyber threats in both virtual and in person settings, the workshops aim to accelerate sales, increase product adoption, and equip sales teams, partners, and workforce skilling teams with practical tools to effectively demonstrate and sell cybersecurity products. Plan: define security policies and compliance requirements using the aqua console. code: scan source code and infrastructure as code (iac) with trivy for vulnerabilities and misconfigurations. build: integrate trivy into ci cd pipelines to scan container images before deployment. This repository explains different methods for deploying each aqua component. aqua components can be deployed on multiple platforms such as kubernetes, aws ecs, red hat openshift, and no orchestrator, using different deployment methods such as manifests, helm charts, operators, proprietary cli tools, rpm, and scripts.

Aqua Security Chiron Whatever your budget or need, we make finding the perfect workspace easy. from flexible memberships to move in ready offices, we give you the space and solutions to do your best work. By simulating real world cyber threats in both virtual and in person settings, the workshops aim to accelerate sales, increase product adoption, and equip sales teams, partners, and workforce skilling teams with practical tools to effectively demonstrate and sell cybersecurity products. Plan: define security policies and compliance requirements using the aqua console. code: scan source code and infrastructure as code (iac) with trivy for vulnerabilities and misconfigurations. build: integrate trivy into ci cd pipelines to scan container images before deployment. This repository explains different methods for deploying each aqua component. aqua components can be deployed on multiple platforms such as kubernetes, aws ecs, red hat openshift, and no orchestrator, using different deployment methods such as manifests, helm charts, operators, proprietary cli tools, rpm, and scripts.
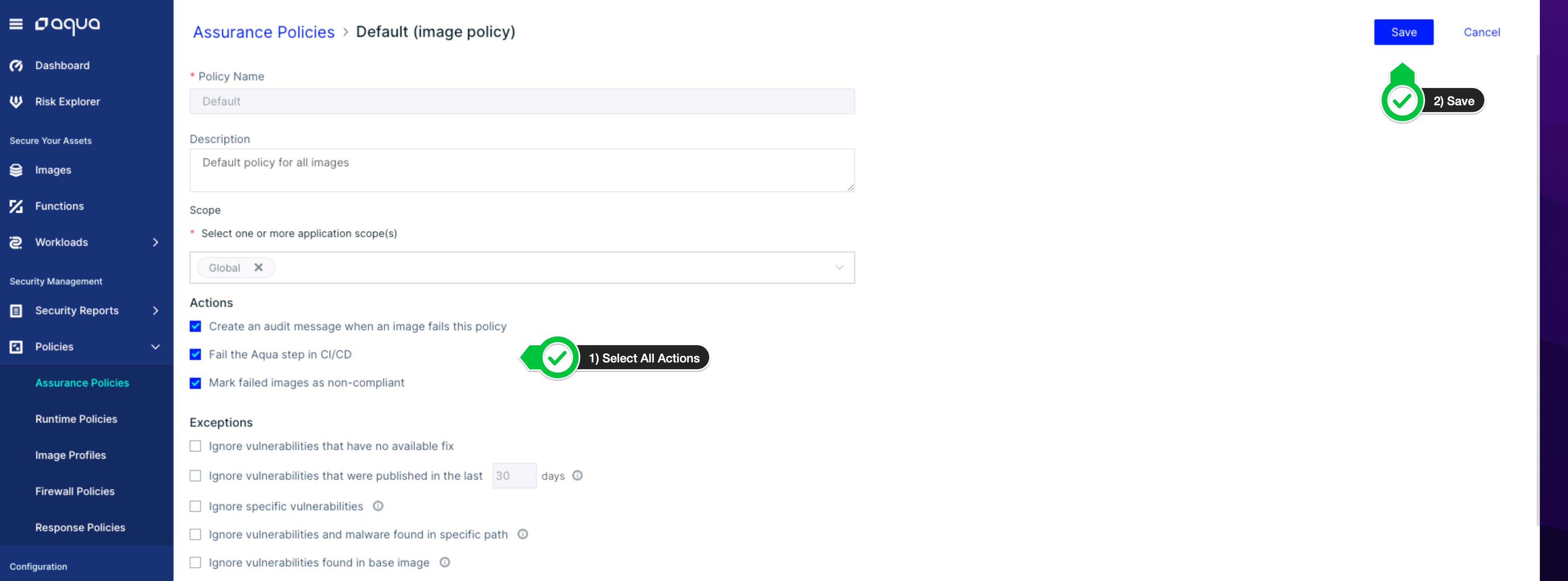
Configuring Assurance Policy Aqua Security Workshop Plan: define security policies and compliance requirements using the aqua console. code: scan source code and infrastructure as code (iac) with trivy for vulnerabilities and misconfigurations. build: integrate trivy into ci cd pipelines to scan container images before deployment. This repository explains different methods for deploying each aqua component. aqua components can be deployed on multiple platforms such as kubernetes, aws ecs, red hat openshift, and no orchestrator, using different deployment methods such as manifests, helm charts, operators, proprietary cli tools, rpm, and scripts.
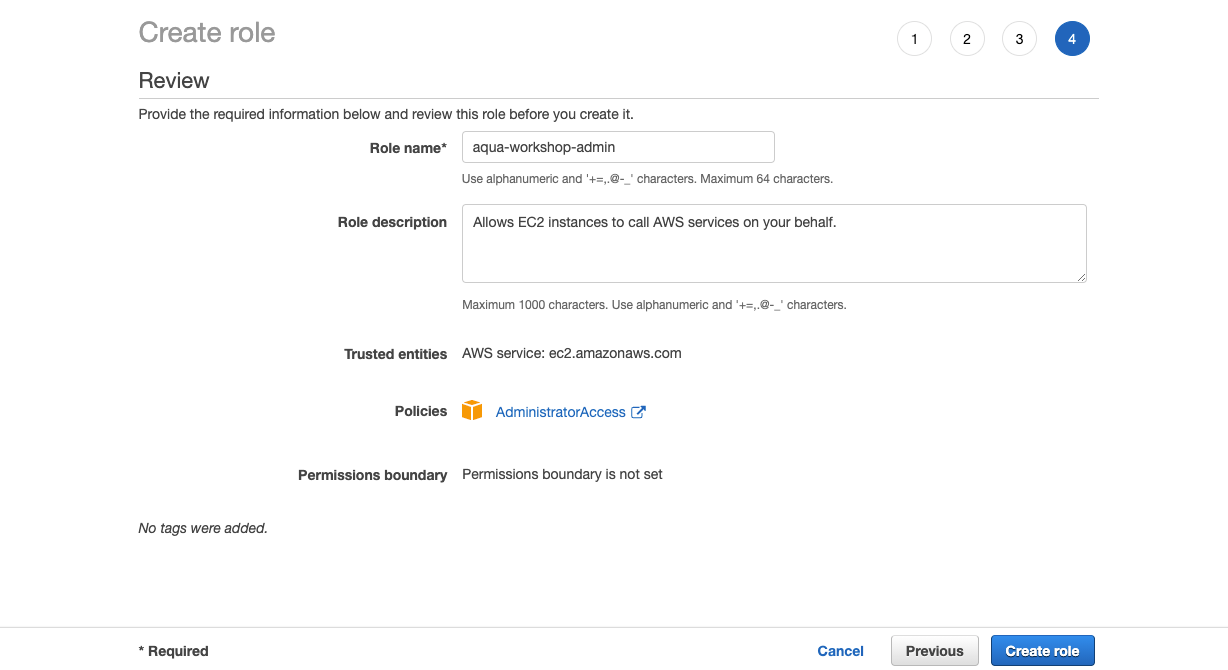
Create An Iam Role For Your Workspace Aqua Security Workshop
Comments are closed.