Create A File Security Profile
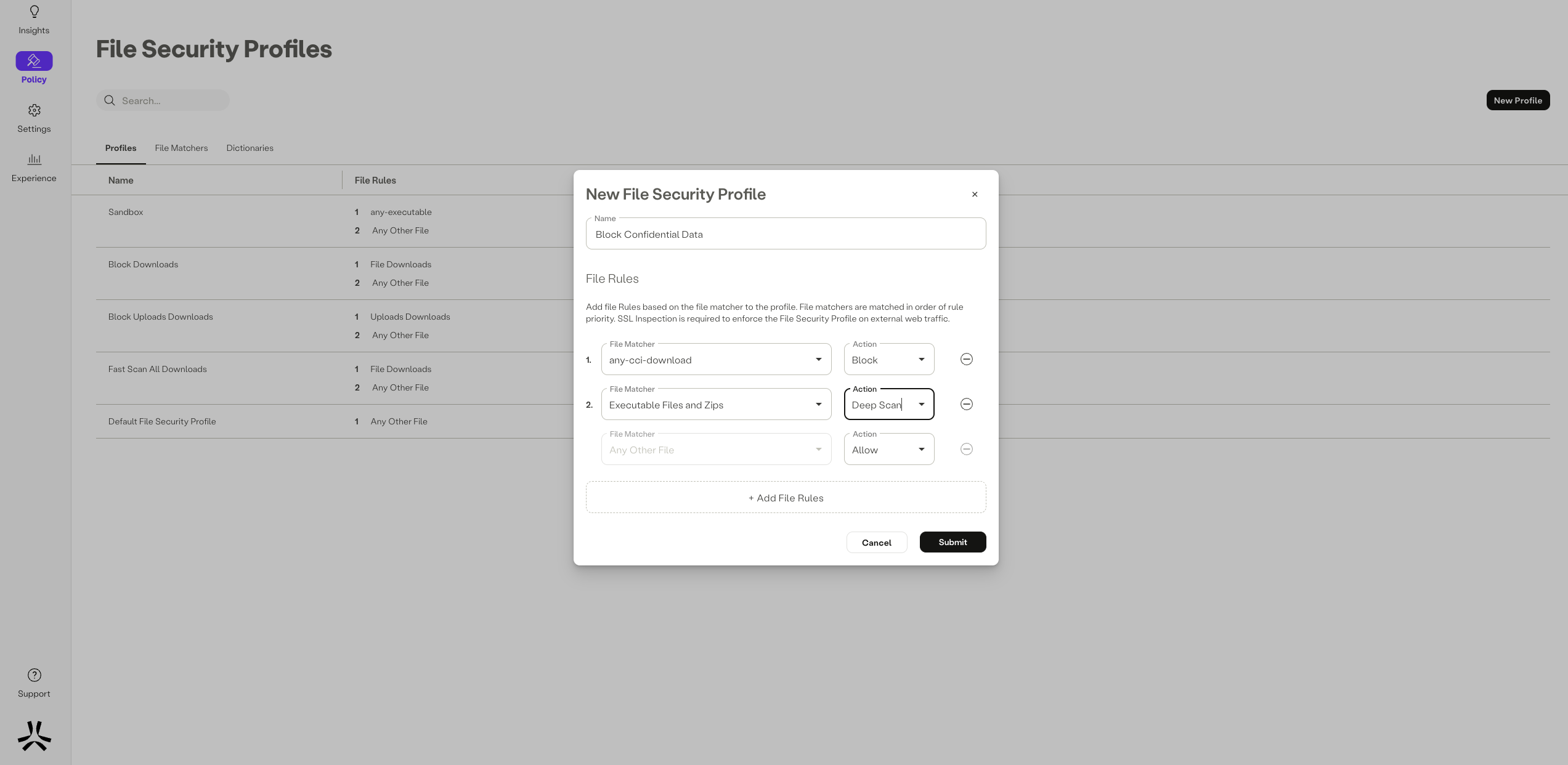
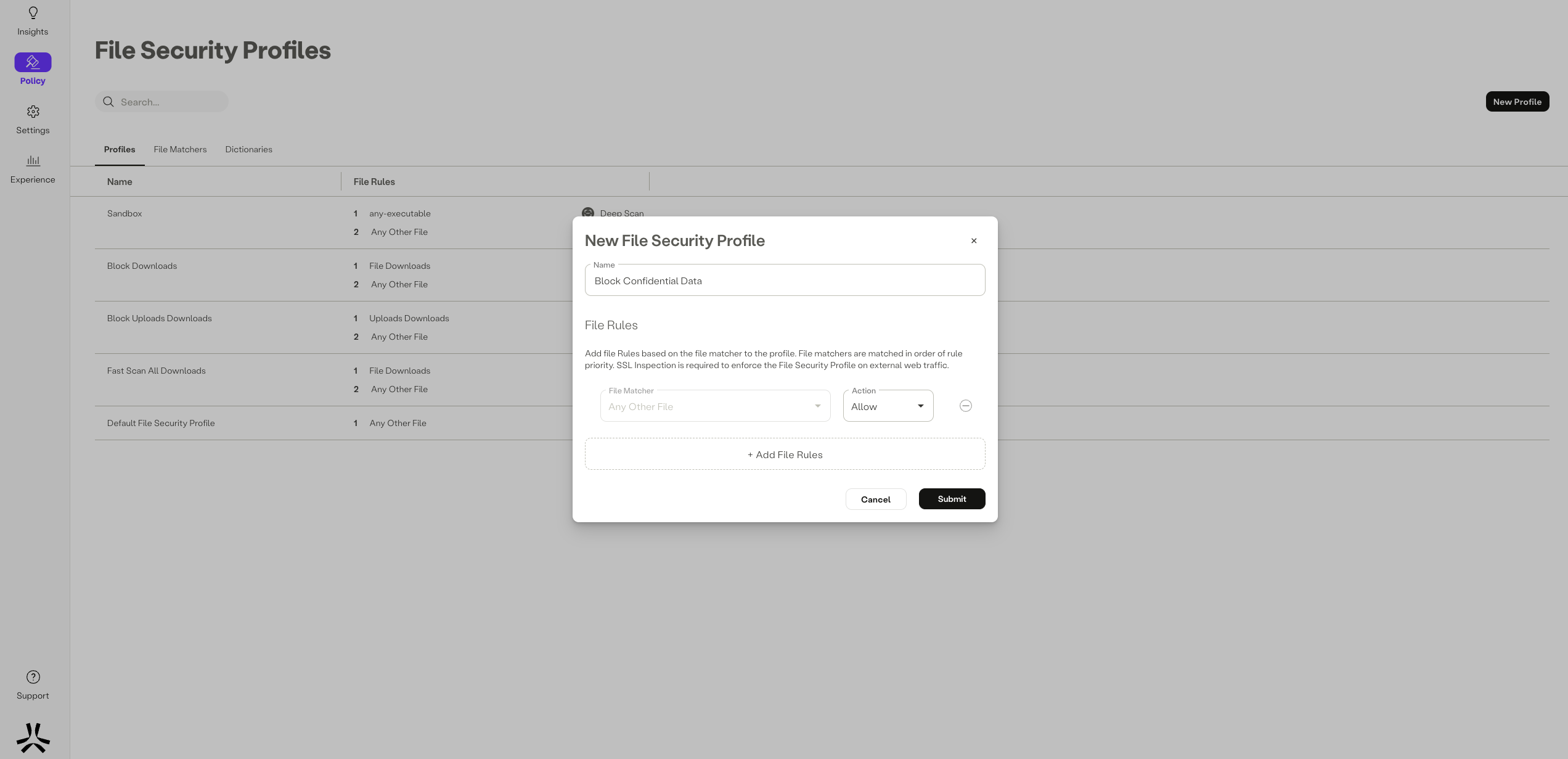
Create A File Security Profile Navigate to policy >file security. under the profiles tab, click the new profile button. enter a name. begin adding file matchers to the fsp by clicking the add file rules button, then select a file matcher from the dropdown. next, select an action to be applied upon match with this file matcher. For recommendations on the best practice settings for security profiles, review the best practices for creating security profiles.
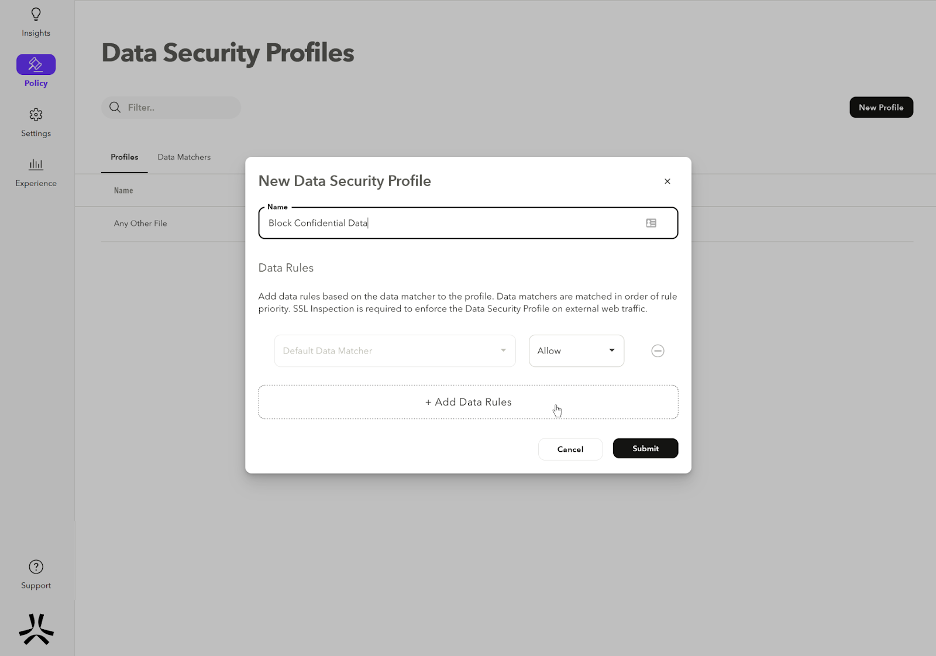
Create A Data Security Profile Scenario: in this lab, we are going to become familiar with different types of security profile such as antivirus, file filter, ips and dns filter. webterm2 acts as a local computer and we set a security profile on traffic passing from port2 to port1. Creating a security profile enables you to grant your users only the permissions that they need. for each permission group, there is a set of resources and supported set of actions. Docker's default seccomp profile is an allowlist which specifies the calls that are allowed. the table below lists the significant (but not all) syscalls that are effectively blocked because they are not on the allowlist. the table includes the reason each syscall is blocked rather than white listed. When you deploy a fortigate cnf instance in fortimanager mode, you can configure all security profiles, such as antivirus, application control, web filtering, and ssl deep inspection, through fortimanager.
Create A File Security Profile Docker's default seccomp profile is an allowlist which specifies the calls that are allowed. the table below lists the significant (but not all) syscalls that are effectively blocked because they are not on the allowlist. the table includes the reason each syscall is blocked rather than white listed. When you deploy a fortigate cnf instance in fortimanager mode, you can configure all security profiles, such as antivirus, application control, web filtering, and ssl deep inspection, through fortimanager. You can create the secure client profile using the secure client profile editor, a gui based configuration tool that is available as part of the secure client software package. You must first upload a client image before creating a client profile. profiles are deployed to administrator defined end user requirements and authentication policies on endpoints as part of cisco secure client, and they make the preconfigured network profiles available to end users. Configure the parameters described in the table below for the new profile, and then click create. note that the create download profile window includes two tabs: general and file types. This section describes the purpose of security profiles in kaspersky endpoint security cloud, as well as how to create, configure, copy, apply, and delete security profiles.

Security Profile Risk Ledger You can create the secure client profile using the secure client profile editor, a gui based configuration tool that is available as part of the secure client software package. You must first upload a client image before creating a client profile. profiles are deployed to administrator defined end user requirements and authentication policies on endpoints as part of cisco secure client, and they make the preconfigured network profiles available to end users. Configure the parameters described in the table below for the new profile, and then click create. note that the create download profile window includes two tabs: general and file types. This section describes the purpose of security profiles in kaspersky endpoint security cloud, as well as how to create, configure, copy, apply, and delete security profiles.

How To Protect Personal File Security In The Digital Age Configure the parameters described in the table below for the new profile, and then click create. note that the create download profile window includes two tabs: general and file types. This section describes the purpose of security profiles in kaspersky endpoint security cloud, as well as how to create, configure, copy, apply, and delete security profiles.
Comments are closed.