Cracking Weak Cryptography Before Quantum Computing Does

How Quantum Computing Threatens Cryptography In Banking Real Risks Government agencies around the globe have sounded the alarm on shoring up cryptography, as some experts predict quantum's arrival as early as spring of 2030, which will subsequently imperil. Two analyses suggest that quantum computers could crack ubiquitous security keys and cryptocurrencies before the decade is over.

Can Quantum Computing Break Traditional Encryption What Experts Say Black hat europe 2023 – london – researchers from microsoft, its github subsidiary, and spain based banco santander here today released a set of open source tools that identify and pinpoint weak cryptography in software, so organizations and developers can jumpstart locking down their security posture for a post quantum computing reality. Worries over crypto’s defenselessness against quantum computing has inspired a project that automates the discovery of insecure cryptographic algorithms in open source software. Google published a paper on march 31 that states that bitcoin's cryptography could be impacted by quantum computing sooner than previously stated. Quantum computers need fewer qubits to crack crypto than thought: google mar 31, 2026 google has updated its estimates of the quantum computing resources needed to break elliptic curve cryptography.

Can Quantum Computing Break Traditional Encryption What Experts Say Google published a paper on march 31 that states that bitcoin's cryptography could be impacted by quantum computing sooner than previously stated. Quantum computers need fewer qubits to crack crypto than thought: google mar 31, 2026 google has updated its estimates of the quantum computing resources needed to break elliptic curve cryptography. Post quantum cryptography refers to cryptographic algorithms designed to be secure against attacks from both classical and quantum computers. nist has been standardizing these algorithms to replace vulnerable systems like rsa before quantum computers become capable of breaking them. Despite the critical dependence of cryptocurrencies on quantum vulnerable ecdlp based cryptography, the inter section of quantum computing and blockchain technology remains under explored. They went on to show this approach could allow a quantum computer to break 256 bit elliptic curve cryptography (ecc) in 10 days while using 100 times less overhead than previously estimated. Objective this study provides a comprehensive analysis of quantum threats to cryptography through systematic review of 67 recent publications (2018–2025), identifying vulnerabilities,.
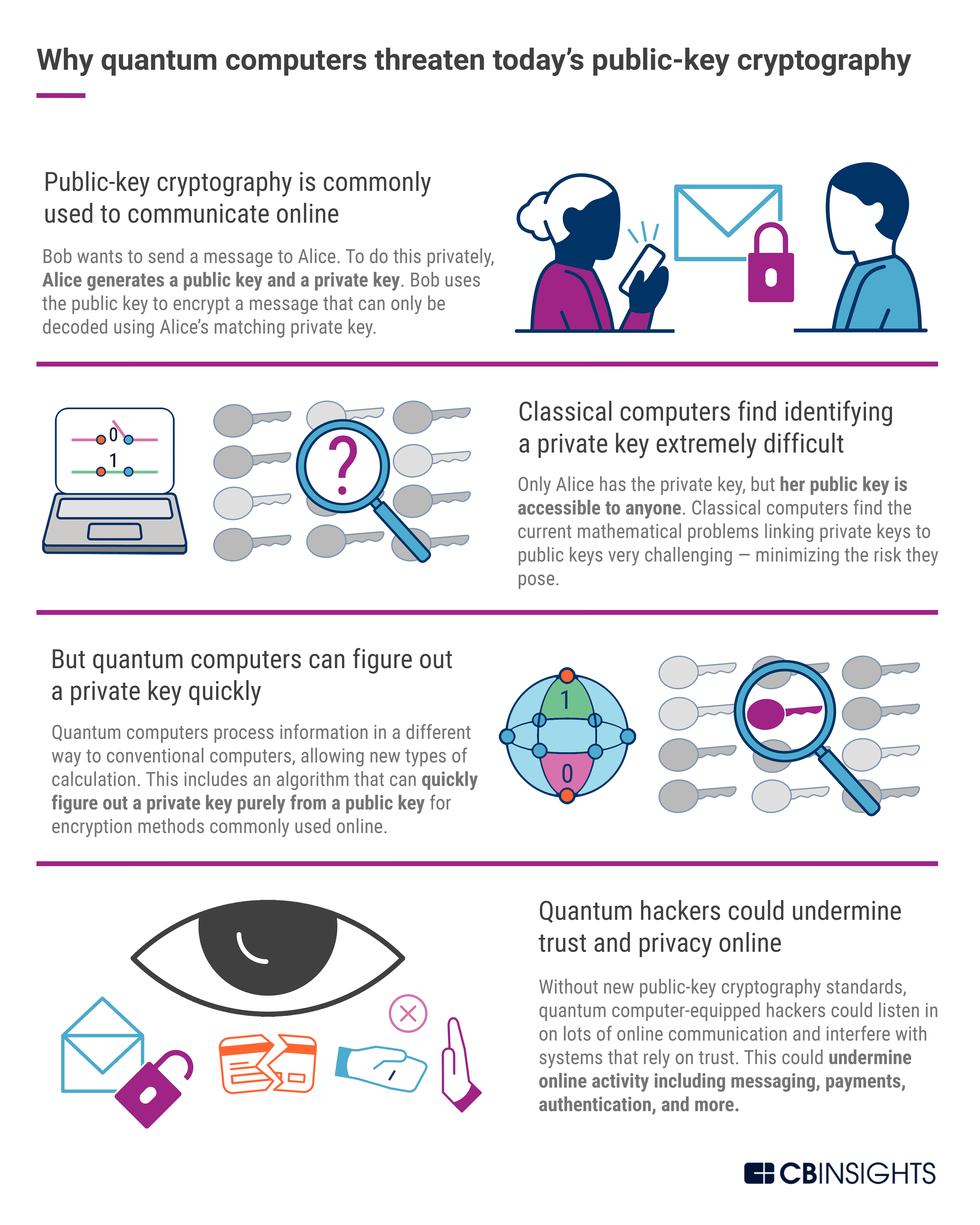
Post Quantum Cryptography A Look At How To Withstand Quantum Computer Post quantum cryptography refers to cryptographic algorithms designed to be secure against attacks from both classical and quantum computers. nist has been standardizing these algorithms to replace vulnerable systems like rsa before quantum computers become capable of breaking them. Despite the critical dependence of cryptocurrencies on quantum vulnerable ecdlp based cryptography, the inter section of quantum computing and blockchain technology remains under explored. They went on to show this approach could allow a quantum computer to break 256 bit elliptic curve cryptography (ecc) in 10 days while using 100 times less overhead than previously estimated. Objective this study provides a comprehensive analysis of quantum threats to cryptography through systematic review of 67 recent publications (2018–2025), identifying vulnerabilities,.
Quantum Computers Take Massive Step Forward For Cryptography Decrypt They went on to show this approach could allow a quantum computer to break 256 bit elliptic curve cryptography (ecc) in 10 days while using 100 times less overhead than previously estimated. Objective this study provides a comprehensive analysis of quantum threats to cryptography through systematic review of 67 recent publications (2018–2025), identifying vulnerabilities,.
Quantum Cryptography The Future Of Unbreakable Security Afralti
Comments are closed.