Corelan Exploit Writing Series Stack Based Overflows

Peter Van Eeckhoutte S Blog Exploit Writing Tutorial Part 1 Stack A way to bridge theory and execution. 🚀 part 1 — stack based buffer overflows (windows 11 x64) we’re kicking things off with part 1 of the original series: 👉 exploit writing tutorial part 1 in the first video, we exploit a stack based buffer overflow on a modern windows 11 x64 environment. by the end of the tutorial, you will have. More specifically, in this video we will be exploiting a stack based buffer overflow on a windows 11 (x64) based virtual machine! by the end of the tutorial, you will have learned how these.
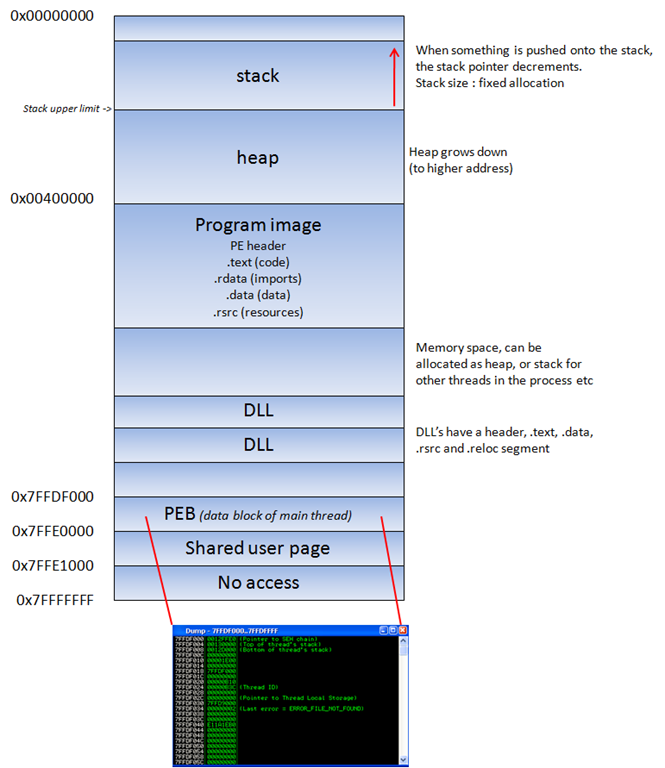
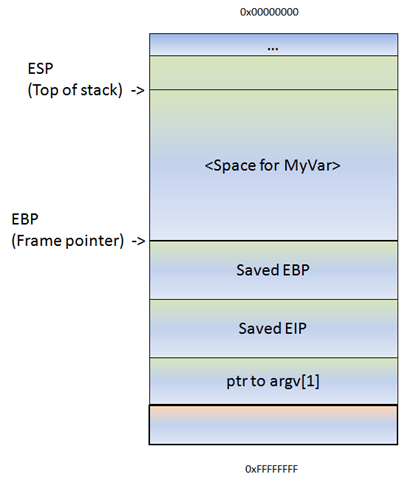
Exploit Writing Tutorial Part 1 Stack Based Overflows Corelan When a buffer on the stack overflows, the term stack based overflow or stack buffer overflow is used. when you are trying to write past the end of the stack frame, the term stack overflow is used. don’t mix those two up, as they are entirely different. the next step is to determining the buffer size to write exactly into eip. A comprehensive tutorial by peter van eeckhoutte on exploit writing, focusing on stack based buffer overflows using the easy rm to mp3 conversion utility. learn vulnerability anal…. Corelan stack is a windows stack exploit development training. learn stack frames, calling conventions, seh overwrites, dep bypasses, rop frameworks, rop decoding, finding bad characters, egghunters on windows 11? memory layout, and real world exploitation techniques. Corelan research publishes in depth tutorials and technical research on exploit development, vulnerability analysis, memory corruption, and low level security internals.
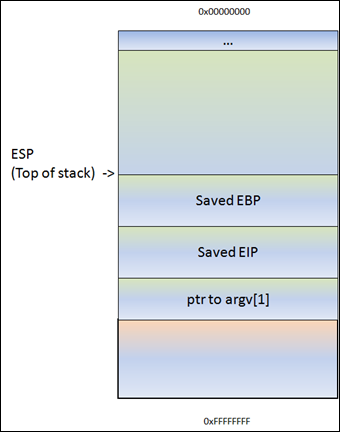
Exploit Writing Tutorial Part 1 Stack Based Overflows Corelan Corelan stack is a windows stack exploit development training. learn stack frames, calling conventions, seh overwrites, dep bypasses, rop frameworks, rop decoding, finding bad characters, egghunters on windows 11? memory layout, and real world exploitation techniques. Corelan research publishes in depth tutorials and technical research on exploit development, vulnerability analysis, memory corruption, and low level security internals. Since 2009, we have published deep technical tutorials covering topics such as stack based exploitation, heap exploitation, shellcoding, reverse engineering and debugging. Corelan research publishes in depth tutorials and technical research on exploit development, vulnerability analysis, memory corruption, and low level security internals. In the first 2 parts of the exploit writing tutorial series, i have discussed how a classic stack buffer overflow works and how you can build a reliable exploit by using various techniques to jump to the shellcode. Ever since i’ve started this blog, writing a basic tutorial about writing buffer overflows has been on my “to do” list but i never really took the time to do so (or simply forgot about it).
Exploit Writing Tutorial Part 1 Stack Based Overflows Corelan Since 2009, we have published deep technical tutorials covering topics such as stack based exploitation, heap exploitation, shellcoding, reverse engineering and debugging. Corelan research publishes in depth tutorials and technical research on exploit development, vulnerability analysis, memory corruption, and low level security internals. In the first 2 parts of the exploit writing tutorial series, i have discussed how a classic stack buffer overflow works and how you can build a reliable exploit by using various techniques to jump to the shellcode. Ever since i’ve started this blog, writing a basic tutorial about writing buffer overflows has been on my “to do” list but i never really took the time to do so (or simply forgot about it).
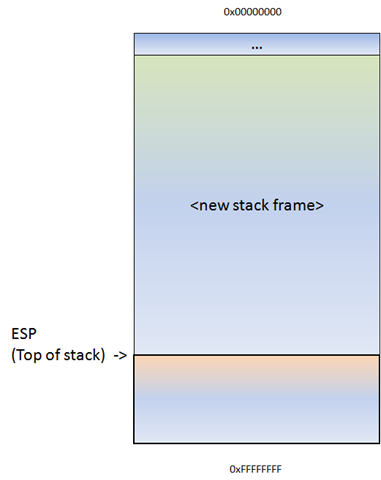
Exploit Writing Tutorial Part 1 Stack Based Overflows Corelan In the first 2 parts of the exploit writing tutorial series, i have discussed how a classic stack buffer overflow works and how you can build a reliable exploit by using various techniques to jump to the shellcode. Ever since i’ve started this blog, writing a basic tutorial about writing buffer overflows has been on my “to do” list but i never really took the time to do so (or simply forgot about it).
Comments are closed.