Controlled Access Protocol Reservation

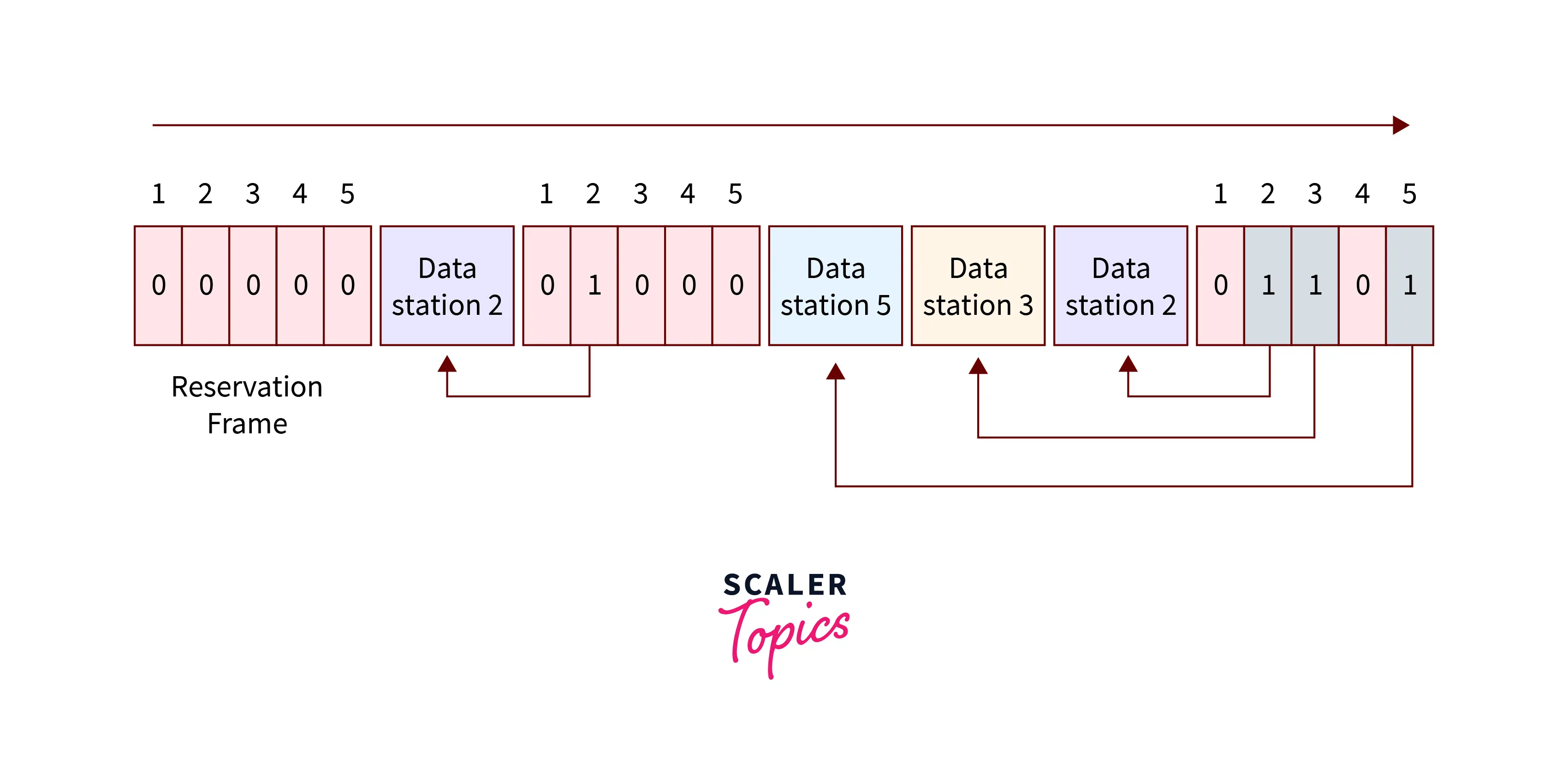
Controlled Access Protocol Reservation Empower Youth What is controlled access? in controlled access, before transmitting data, a station must first obtain permission to access the channel. at any given time, only one node can send data, preventing collisions. this coordination is achieved using one of three methods: reservation polling token passing reservation. Controlled access protocols allow only one node to send at a time to avoid message collisions. there are three main controlled access methods: reservation, polling, and token passing. reservation methods divide time into intervals, with reservation frames preceding data frames to reserve slots.
Controlled Access Protocol Scaler Topics Controlled access protocols in computer networks explained with reservation, polling, and token passing methods, features, pros, and limitations. In the reservation method, the device makes a reservation before sending data over a channel. time is divided into intervals, and at a particular interval, the device sends frames over a channel that has made the reservation. Whether you’re preparing for gate, ugc net, btech, mca, or university exams, this video is your one stop guide to mastering this important computer networks topic. 🚀 🔹 what’s covered in this. Three common controlled access protocol methods are reservation, token passing, and polling. in reservation, a station needs to make a reservation then only it can transmit the data on the medium.
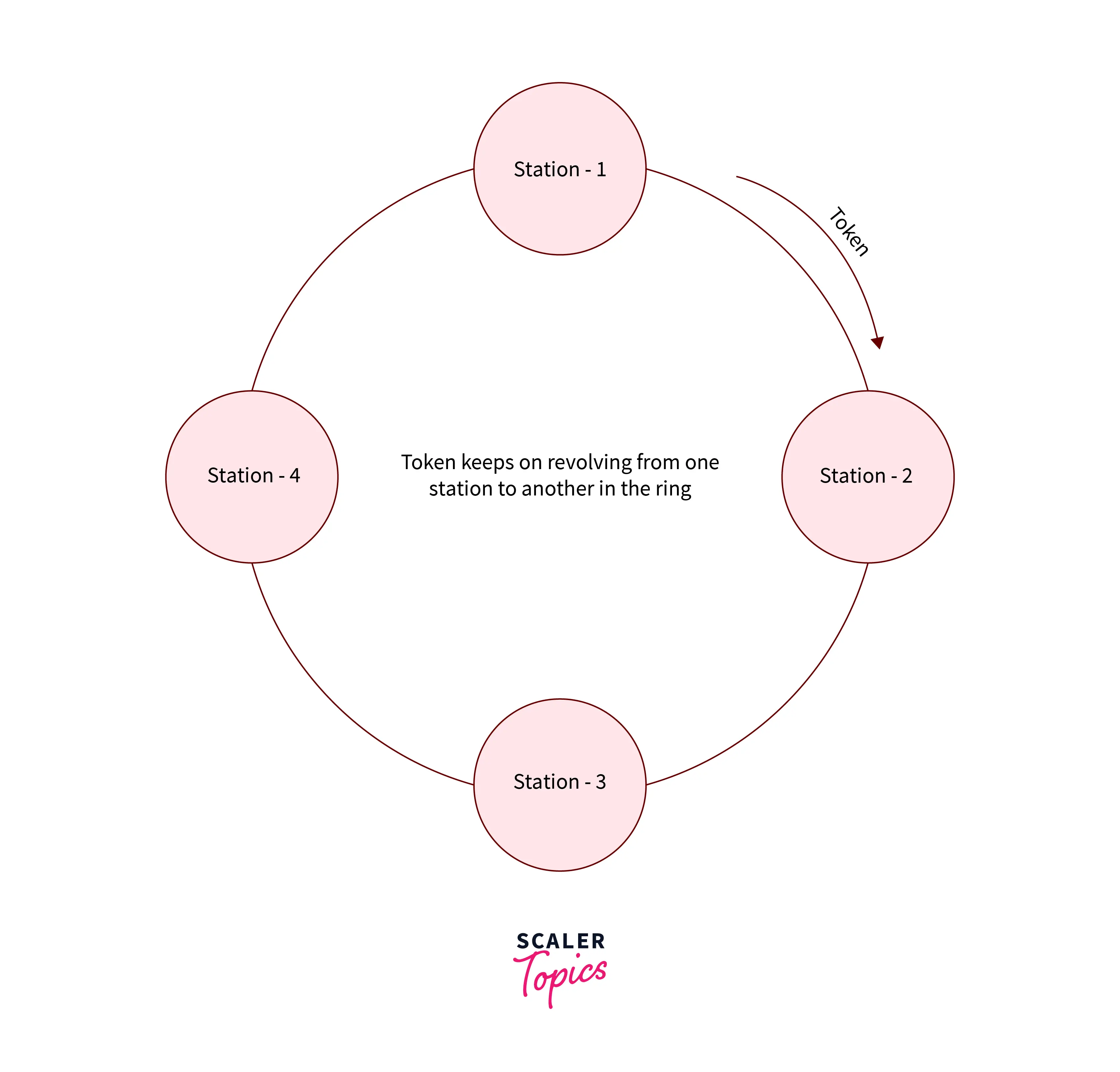
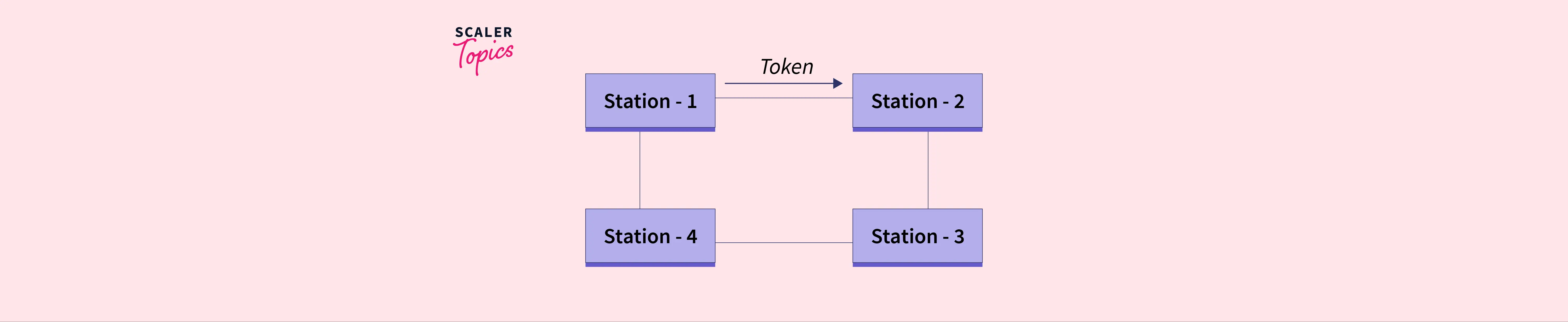
Controlled Access Protocol Scaler Topics Whether you’re preparing for gate, ugc net, btech, mca, or university exams, this video is your one stop guide to mastering this important computer networks topic. 🚀 🔹 what’s covered in this. Three common controlled access protocol methods are reservation, token passing, and polling. in reservation, a station needs to make a reservation then only it can transmit the data on the medium. Control access protocols allow only one node to send at a time. in this way, the collision of messages on shared media can be avoided. 1. reservation. according to the reservation, every station needs to make a reservation before transmitting the data. How do reservation based protocols work in controlled access? answer: reservation based protocols require devices to reserve the right to transmit before sending data. The three main approaches are reservation, where stations reserve time slots; polling, where a controller sequentially checks each station; and token passing, which uses a token to grant transmission rights in a logical ring. Controlled access protocols primarily grant permission to send only one node at a time. its three common methods are reservation, token passing, and polling.
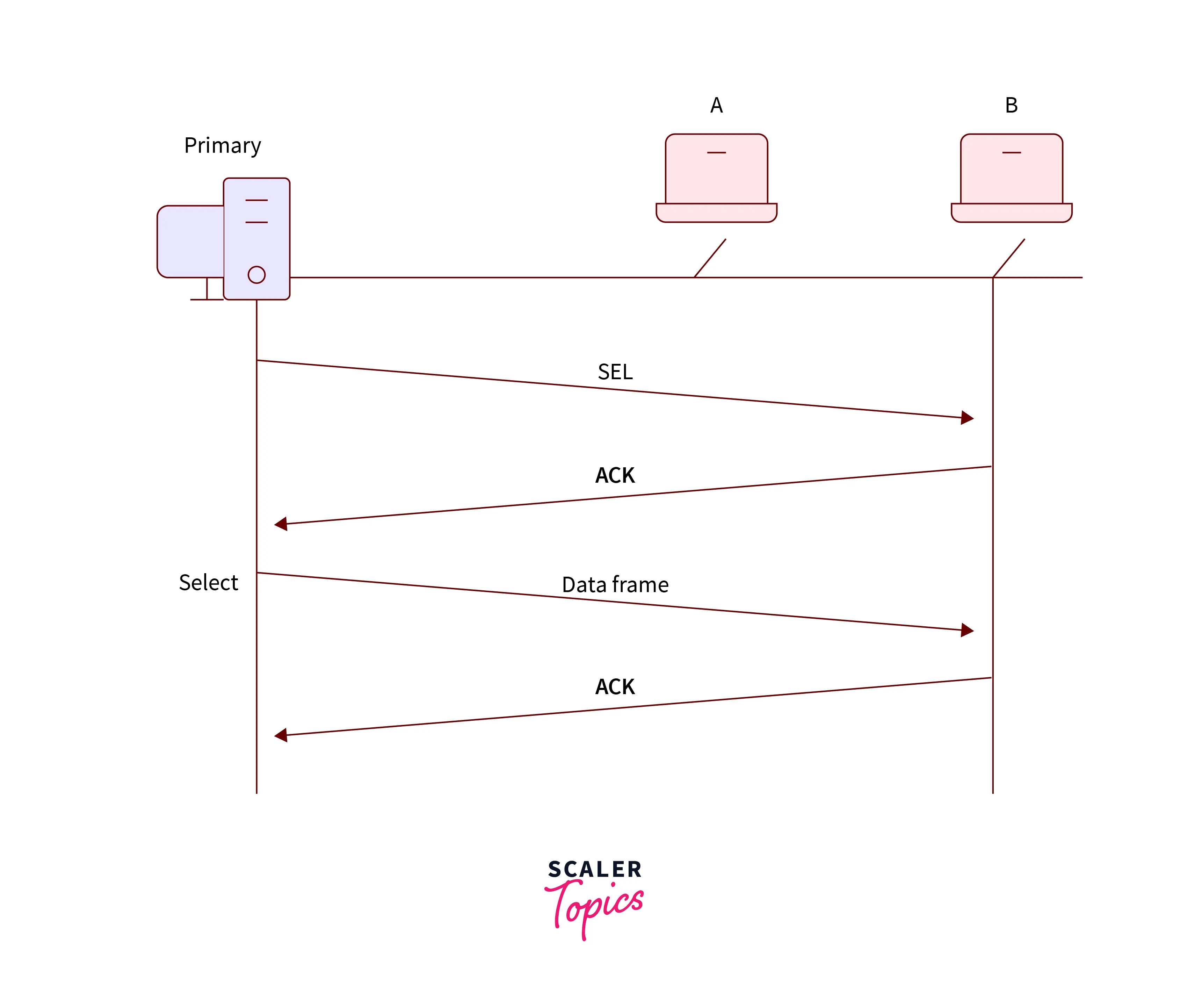
Controlled Access Protocol Scaler Topics Control access protocols allow only one node to send at a time. in this way, the collision of messages on shared media can be avoided. 1. reservation. according to the reservation, every station needs to make a reservation before transmitting the data. How do reservation based protocols work in controlled access? answer: reservation based protocols require devices to reserve the right to transmit before sending data. The three main approaches are reservation, where stations reserve time slots; polling, where a controller sequentially checks each station; and token passing, which uses a token to grant transmission rights in a logical ring. Controlled access protocols primarily grant permission to send only one node at a time. its three common methods are reservation, token passing, and polling.
Controlled Access Protocol Scaler Topics The three main approaches are reservation, where stations reserve time slots; polling, where a controller sequentially checks each station; and token passing, which uses a token to grant transmission rights in a logical ring. Controlled access protocols primarily grant permission to send only one node at a time. its three common methods are reservation, token passing, and polling.
Comments are closed.