Control Flow Graph Wake
Lsp Control Flow Graph Wake Generates a control flow graph of a function or modifier by clicking on the code lens using the language server protocol. direction of the graph. whether to generate links to the source code. wake is a python based solidity development and testing framework with built in vulnerability detectors. With the ability to make accurate predictions under different inflow conditions and turbine yaw angles in less than 15 ms, the graph neural network approach has the potential to be utilised in wind farm control and optimisation problems including yaw angle based wake steering.
Control Flow Graph Wake Now, control flow graphs are not merely of theoretical interest! like abstract syntax trees, they are used as a form of static analysis when compiling program code or analysing it for errors. Representation of the wakes in a wind farm using a net work of fvw models, with an indication of the graph connecting the wakes which have been individually simulated. A control flow graph (cfg) is the graphical representation of control flow or computation during the execution of programs or applications. control flow graphs are mostly used in static analysis as well as compiler applications, as they can accurately represent the flow inside a program unit. • wind speed 8 m s, ti 7.3%, neutral conditions • ideal yaw control, no low pass filtering nor rate saturation • farm wide coherence model from vigueras rodriguez, 2010.
Github Ethanblake4 Control Flow Graph Dart Library For Creating And A control flow graph (cfg) is the graphical representation of control flow or computation during the execution of programs or applications. control flow graphs are mostly used in static analysis as well as compiler applications, as they can accurately represent the flow inside a program unit. • wind speed 8 m s, ti 7.3%, neutral conditions • ideal yaw control, no low pass filtering nor rate saturation • farm wide coherence model from vigueras rodriguez, 2010. Result: hierarchical cfg with tarjan intervals. irreducible subraph is an interval! back edges are not unique!. A control flow graph is a data structure built on top of the intermediate code representation (rtl instruction chain or trees) abstracting the control flow behavior of compiled function. Function basic block control flow analysis: determine control structure of a program and build control flow graphs (cfgs) data flow analysis: determine the flow of data values and build data flow graphs (dfgs). Transformer based malware detection systems operating on graph modalities such as control flow graphs (cfgs) achieve strong performance by modeling structural relationships in program behavior. however, their robustness to adversarial evasion attacks remains underexplored. this paper examines the vulnerability of a roberta based malware detector that linearizes cfgs into sequences of function.
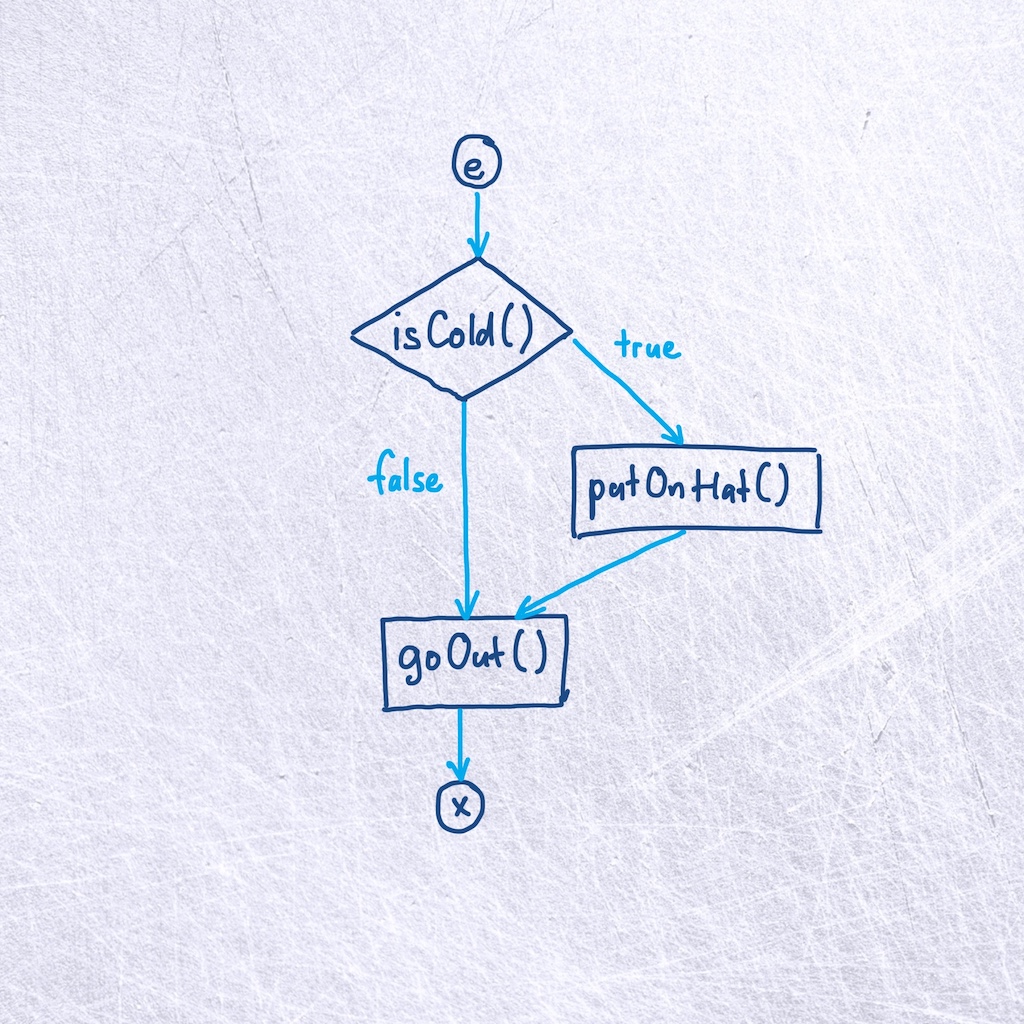
Control Flow As Graph 2 Selection Result: hierarchical cfg with tarjan intervals. irreducible subraph is an interval! back edges are not unique!. A control flow graph is a data structure built on top of the intermediate code representation (rtl instruction chain or trees) abstracting the control flow behavior of compiled function. Function basic block control flow analysis: determine control structure of a program and build control flow graphs (cfgs) data flow analysis: determine the flow of data values and build data flow graphs (dfgs). Transformer based malware detection systems operating on graph modalities such as control flow graphs (cfgs) achieve strong performance by modeling structural relationships in program behavior. however, their robustness to adversarial evasion attacks remains underexplored. this paper examines the vulnerability of a roberta based malware detector that linearizes cfgs into sequences of function.
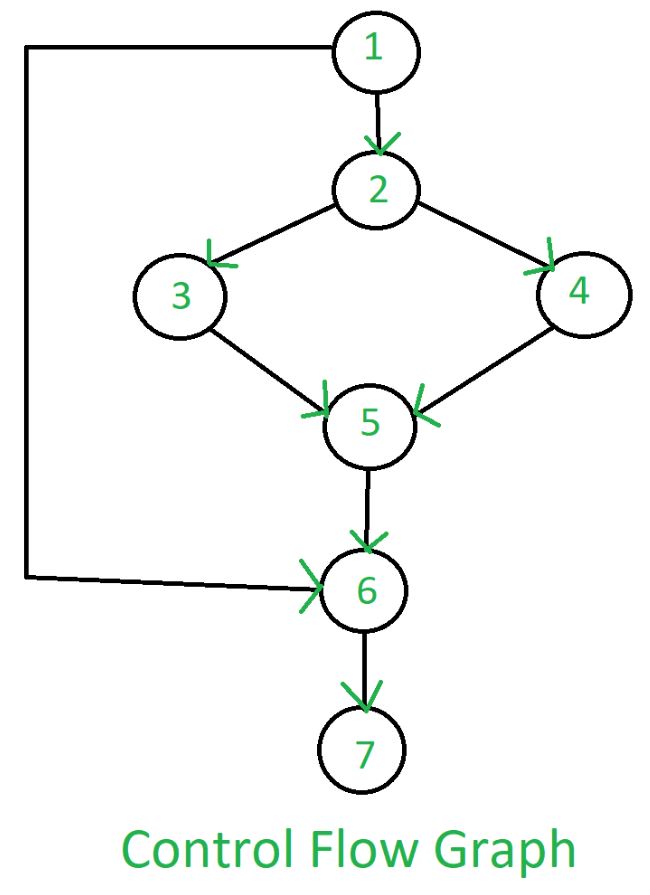
Control Flow Graph Cfg Software Engineering Geeksforgeeks Function basic block control flow analysis: determine control structure of a program and build control flow graphs (cfgs) data flow analysis: determine the flow of data values and build data flow graphs (dfgs). Transformer based malware detection systems operating on graph modalities such as control flow graphs (cfgs) achieve strong performance by modeling structural relationships in program behavior. however, their robustness to adversarial evasion attacks remains underexplored. this paper examines the vulnerability of a roberta based malware detector that linearizes cfgs into sequences of function.
Comments are closed.