Context Aware Access Policies

An Context Aware Management And Control Mechanism In A Mobile Using context aware access, you can create granular access control security policies for apps based on attributes, such as user identity, location, device security status, and ip address. your. Caa creates granular access control security policies for apps based on attributes, such as user identity, location, device security status, and ip address, and they can be applied to users on personal and managed devices.

Context Aware Access Policies Britive Discover how modern iam platforms leverage context—like location, device, time, and risk signals—to power adaptive, risk based access. explore the benefits, implementation strategies, and common pitfalls of context aware access controls for smarter security. Controlling network access with context aware access policies the following topics explain how to use context aware access policies on cx devices to control access to the network. Using context aware access, you can create granular access control policies for apps that access workspace data based on attributes, such as user identity, location, device security status,. Context aware policies help ensure that every access request meets compliance requirements by enforcing least privilege principles in real time. this level of control provides an audit ready trail of adaptive permissions, simplifying compliance and making it easier to pass audits.
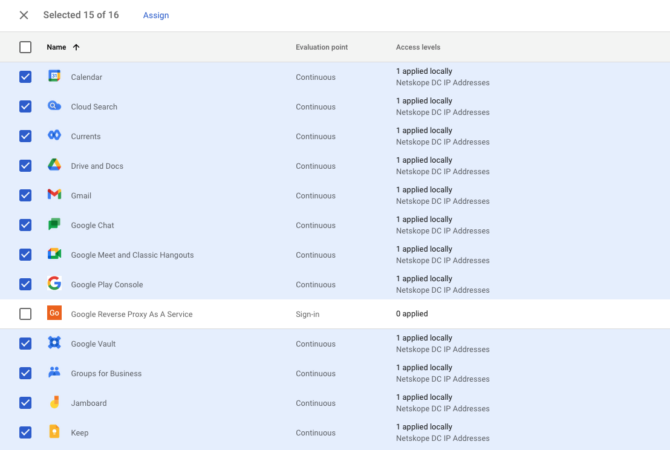
Create Context Aware Access Policies Netskope Knowledge Portal Using context aware access, you can create granular access control policies for apps that access workspace data based on attributes, such as user identity, location, device security status,. Context aware policies help ensure that every access request meets compliance requirements by enforcing least privilege principles in real time. this level of control provides an audit ready trail of adaptive permissions, simplifying compliance and making it easier to pass audits. Context aware network access is a security mechanism that dynamically enforces access policies based on the specific context of a user or device trying to access a system. We’re making it easier to apply context aware access (caa) policies with new insights and recommendations. we’ll proactively surface potential security gaps and suggest pre built caa levels which admins can deploy to remediate the security gaps. To help secure your apps and google cloud resources, you can define granular access controls based on a variety and combination of contextual factors. you can use access context manager to define. Explore microsoft entra conditional access, the zero trust policy engine that integrates signals to secure access to resources.
Comments are closed.